The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added a high-severity flaw in the Service Location Protocol (SLP) to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation.
Tracked as CVE-2023-29552 (CVSS score: 7.5), the issue relates to a denial-of-service (DoS) vulnerability that could be weaponized to launch massive DoS amplification attacks.
It was disclosed by Bitsight and Curesec earlier this April.

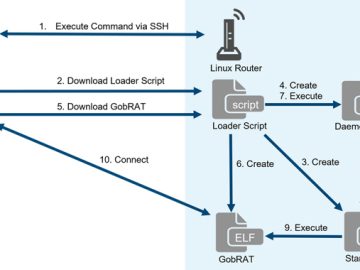
“The Service Location Protocol (SLP) contains a denial-of-service (DoS) vulnerability that could allow an unauthenticated, remote attacker to register services and use spoofed UDP traffic to conduct a denial-of-service (DoS) attack with a significant amplification factor,” CISA said.
SLP is a protocol that allows systems on a local area network (LAN) to discover each other and establish communications.
The exact details surrounding the nature of exploitation of the flaw are currently unknown, but Bitsight previously warned that the shortcoming could be exploited to stage DoS with a high amplification factor.
“This extremely high amplification factor allows for an under-resourced threat actor to have a significant impact on a targeted network and/or server via a reflection DoS amplification attack,” it said.
In light of real-world attacks employing the flaw, federal agencies are required to apply the necessary mitigations, including disabling the SLP service on systems running on untrusted networks, by November 29, 2023, to secure their networks against potential threats.