How do companies respond to 0days in 3rd party software?

Source link
Related Articles
All Mix →GitHub Celebrates Four Years of Bug Bounties: Q&A with VP of Security, Shawn Davenport
GitHub celebrated the fourth anniversary of its Security Bug Bounty program and released a comprehensive recap of a record-breaking 2017 to mark the moment. To…
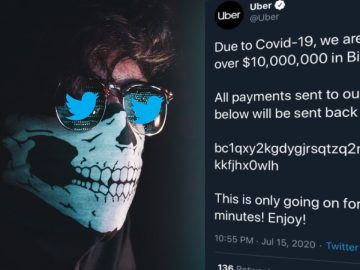
How easy is it to tweet as anyone? | Twitter Hacks & Bug Bounty
How easy is it to tweet as anyone? | Twitter Hacks & Bug Bounty Source link
No. 381 Nurturing High-Performers, AI Business Takeover, Cyber Threats, and Diversifying Production 🌐🤖📱
*|INTERESTED:Memberful Plans:UL Subscription (Annual) (53074)|* *|END:INTERESTED|* *|INTERESTED:Memberful Plans:UL Subscription (Annual) (53074)|**|ELSE:|* *|END:INTERESTED|* Unsupervised Learning is a Security, AI, and Meaning-focused podcast that looks at how…
Jailbreaks, Injections, and Agentic Risks
AI has officially moved out of the novelty phase. What began with people messing around with LLM-powered GenAI tools for content creation has rapidly evolved…
The story behind HackerOne’s first anniversary gift for employees
The HackerOnesie instantly became famous the day it was introduced in 2017. Although it has been known to carry magical powers, it is now one…
Debunked: Is a subdomain takeover ‘game over’ for companies?
Table of Contents How subdomain takeover was discovered Subdomains – gateway into the inner workings of an organization Danger Danger: Dangling CNAME records How a…