- Introduction
- The Anatomy of a Modern Ransomware Attack
- Stage 1: Initial Access
- Stage 2: Dwell Time and Lateral Movement
- Stage 3: Execution and Extortion
- The Full-Spectrum Business Impact of a Ransomware Attack
- Disruption to Business Operations
- Cascading Financial Costs
- The Long-Term Damage to Brand Reputation
- The Hard Road to Recovery
- Building Resilience Against Ransomware
- Challenges Facing Enterprises
- How Threat Intelligence Shuts Down Ransomware Attacks
- Ransomware Is a Business Resiliency Test

Introduction
When ransomware struck Change Healthcare in February 2024, the attack paralyzed prescription processing across the United States, forcing pharmacies to turn patients away and hospitals to revert to paper records. The breach affected 190 million Americans and cost UnitedHealth Group over $2.4 billion, making it the largest healthcare data breach in U.S. history.
The incident exposed a critical reality: ransomware attacks have evolved far beyond data encryption into sophisticated operations that can halt business operations, drain financial reserves, and permanently damage corporate reputations.
According to Verizon’s 2025 Data Breach Investigations Report (DBIR), ransomware was present in 44% of all breaches analyzed, up from 32% the previous year. IBM’s Cost of a Data Breach Report 2025 found that ransomware incidents average $5.08 million. That figure represents only the direct costs and not the cascading impacts on operations, customer trust, and competitive positioning.
This article will explain the mechanics of a modern ransomware attack and analyze its broader impact on business operations, financial stability, and brand reputation, while demonstrating how comprehensive threat intelligence is essential for both prevention and mitigation.
The Anatomy of a Modern Ransomware Attack
Ransomware is malicious software that encrypts or exfiltrates a victim’s data, rendering it unusable until a ransom is paid, typically in cryptocurrency. What distinguishes modern ransomware from earlier variants is the sophistication of the attack chain and the devastating effectiveness of multi-stage extortion tactics.
Per IBM, customer personally identifiable information (PII) appeared in 53% of breaches—more than any other data type. Employee PII was stolen in 37% of cases, while intellectual property (33%) and other corporate data (34%) were each compromised in roughly one-third of incidents.
Stage 1: Initial Access
Attackers exploit unpatched software vulnerabilities, steal credentials, or infiltrate through phishing and third-party suppliers to gain that critical first foothold. These vectors account for the majority of ransomware entry points:
- Compromised credentials: IBM X-Force’s 2025 Threat Intelligence Index reports that identity-based attacks make up 30% of total intrusions, with attackers increasingly using valid accounts rather than brute-force hacking. This shift reflects the growing sophistication of credential theft operations.
- Unpatched software vulnerabilities: Exploited vulnerabilities now represent 20% of all breaches, approaching credential abuse as the top initial access vector. Edge devices and VPNs are particularly targeted, with attacks on these assets increasing eight-fold from the previous year, according to Verizon’s DBIR.
- Third-party or supply-chain compromise: According to IBM, supply-chain intrusions represent 15% of breaches and the second costliest at $4.91 million per breach. Supply chain attacks took the longest to detect and contain at a combined 267 days, highlighting the challenge of securing interconnected business ecosystems.
- Social engineering and phishing: Per ENISA’s Threat Landscape 2025 report, AI was used in over 80% of observed phishing activity, making these attacks more convincing and harder to detect.
Stage 2: Dwell Time and Lateral Movement
Dwell time is the period after initial entry that attackers spend discreetly mapping the network and gathering intelligence before executing their final attack. This reconnaissance phase is critical to maximizing the damage and ransom potential.
During this phase, attackers focus on three key objectives:
- Escalating privileges to gain administrator-level access, allowing them to disable security controls and access sensitive systems
- Identifying high-value assets such as financial servers, domain controllers, and backup systems that can be used as leverage
- Exfiltrating large volumes of sensitive data to use as additional extortion material in double-extortion schemes
When organizations’ own security teams identified breaches, mean time to identify was 172 days with 52 days to contain, for a total of 224 days of dwell time, according to IBM’s research. This extended period gives attackers ample opportunity to prepare for maximum impact.
Stage 3: Execution and Extortion
In the final stage, attackers encrypt systems and demand payment for a decryption key. However, encryption is often just the beginning of the extortion process.
In “double extortion” attacks, adversaries also threaten to leak exfiltrated data on public or dark-web sites. ENISA reports that ransomware groups have adopted aggressive double- and triple-extortion tactics, exploiting regulatory compliance fears to pressure victims into paying.
The current ransom landscape shows interesting trends. While the average cost of a ransomware breach remains high ($5.08 million), fewer organizations are willing to pay ransoms: 63% refused to pay in 2025 compared to 59% in 2024, according to IBM. This resistance may be contributing to declining ransom demands, with the median payment dropping to $115,000.
Importantly, IBM found that involving law enforcement can reduce the cost of a ransomware attack by $1 million on average, yet only 40% of organizations contacted law enforcement in 2025, down from 53% the previous year.
The Full-Spectrum Business Impact of a Ransomware Attack
Ransomware triggers a damaging chain reaction across operations, finance, and brand reputation that extends far beyond the initial encryption event.
Disruption to Business Operations
When critical systems are locked, every minute counts. IBM’s research found that 86% of organizations experienced operational disruption due to their data breach, with impacts varying by industry:
- Manufacturing faces production lines that stop and supply chains that stall, often triggering contractual penalties with customers and partners. The inability to fulfill orders or meet delivery schedules creates a ripple effect throughout the supply chain.
- Healthcare organizations confront canceled appointments and delayed care. In some cases, patient safety is directly at risk when electronic health records become inaccessible or medical devices are compromised.
- Retail and logistics operations see point-of-sale systems and fulfillment networks freeze, halting transactions globally. E-commerce platforms go dark, and customers are unable to complete purchases or track shipments.
Even with decryption keys, recovery can take weeks as teams rebuild servers, revalidate backups, and ensure no hidden backdoors remain. This extended downtime multiplies the operational impact and compounds financial losses.
Cascading Financial Costs
The ransom itself is only one line item in a much larger financial impact. Cybersecurity Ventures predicts global ransomware damage costs will reach $275 billion by 2031, with a new attack occurring every 2 seconds.
Direct costs include:
- Ransom payments (when made)
- Incident response retainers and forensics investigations
- Legal and regulatory compliance fines
- Emergency security upgrades and remediation
Indirect costs often exceed direct expenses:
- Lost productivity and revenue during downtime: Lost business costs (revenue from system downtime, lost customers, reputational damage) averaged $1.38 million, according to IBM.
- Increased cyber insurance premiums: Organizations often face dramatically higher premiums or reduced coverage after an incident.
- Delays to innovation and strategic projects: Post-breach response costs (help desk, credit monitoring, legal expenditures, product discounts) averaged $1.2 million, while notification costs (to data subjects, regulators, and third parties) averaged $0.39 million.
The Long-Term Damage to Brand Reputation
The most enduring consequence of a ransomware attack can be reputational loss. The prevalence of double extortion makes every attack a potential public relations crisis.
Public exposure through data leaks posted on ransomware “leak sites” can include intellectual property, trade secrets, and sensitive customer data. This stolen information is often weaponized to pressure organizations into paying, but even payment doesn’t guarantee data won’t be leaked or sold.
Erosion of trust follows when customers, investors, and partners question a company’s reliability and security posture. In competitive markets, this loss of confidence translates directly to lost business.
Competitive disadvantage emerges as breached organizations may lose bids or contract renewals due to perceived security weaknesses. Customers migrate to competitors who can demonstrate stronger security controls.
Partner risk increases when B2B partners and suppliers view the breached company as a supply chain liability, potentially terminating relationships or demanding costly security audits and improvements.
Brand recovery can take years, often requiring sustained PR campaigns, customer compensation programs, and long-term monitoring for data misuse in the wild.
The data types most at risk for reputational harm, per IBM, include:
- Customer PII, compromised in 53% of breaches at $160 per record
- Medical data, though less common overall, commands significant reputational concern in healthcare
- Employee PII, compromised in 37% of breaches
The Hard Road to Recovery
Full recovery means more than restoring systems. It encompasses business operations returning to normal, compliance obligations being met (including fines paid), customer confidence and employee trust being restored, and controls being in place to prevent future breaches.
In IBM’s Cost of a Data Breach report, 65% of organizations were still in the process of recovering from their breach at the time of reporting. Among organizations that fully recovered, 76% said recovery took longer than 100 days, with 26% requiring more than 150 days to achieve full recovery.
[CTA] For a deeper walkthrough of how to prepare, respond, and recover from modern ransomware attacks, read our ransomware response guide.
Building Resilience Against Ransomware
Despite growing awareness, ransomware thrives because traditional defenses focus on detection after compromise, not prevention. The reactive security model leaves organizations perpetually one step behind adversaries who continuously evolve their tactics.
Threat actors continuously adapt their tactics, techniques, and procedures (TTPs), using legitimate tools, cloud infrastructure, and AI-generated phishing to evade signature-based detection. This evolution demands a corresponding shift in defensive strategy.
Recorded Future’s State of Threat Intelligence 2025 report found that 68% of enterprises now rely on threat intelligence to enhance detection and 43% use it for strategic planning, underscoring the shift toward proactive defense.
Challenges Facing Enterprises
A reactive posture remains the norm. PwC’s 2025 Global Digital Trust Insights reports that only 24% of organizations invest significantly more in proactive measures than reactive ones, despite the proven cost-effectiveness of prevention over remediation.
Speed mismatches create vulnerability windows. Per Verizon’s DBIR, organizations took a median of 32 days to fully patch or remediate edge device vulnerabilities, yet attackers often exploit these within zero days of disclosure, leaving organizations perpetually exposed during the patch cycle.
Skills shortages continue to constrain security teams. While improving from 53% the previous year, 48% of organizations still reported high levels of security skills shortage, according to IBM. This gap limits the ability to implement and maintain advanced security controls.
How Threat Intelligence Shuts Down Ransomware Attacks
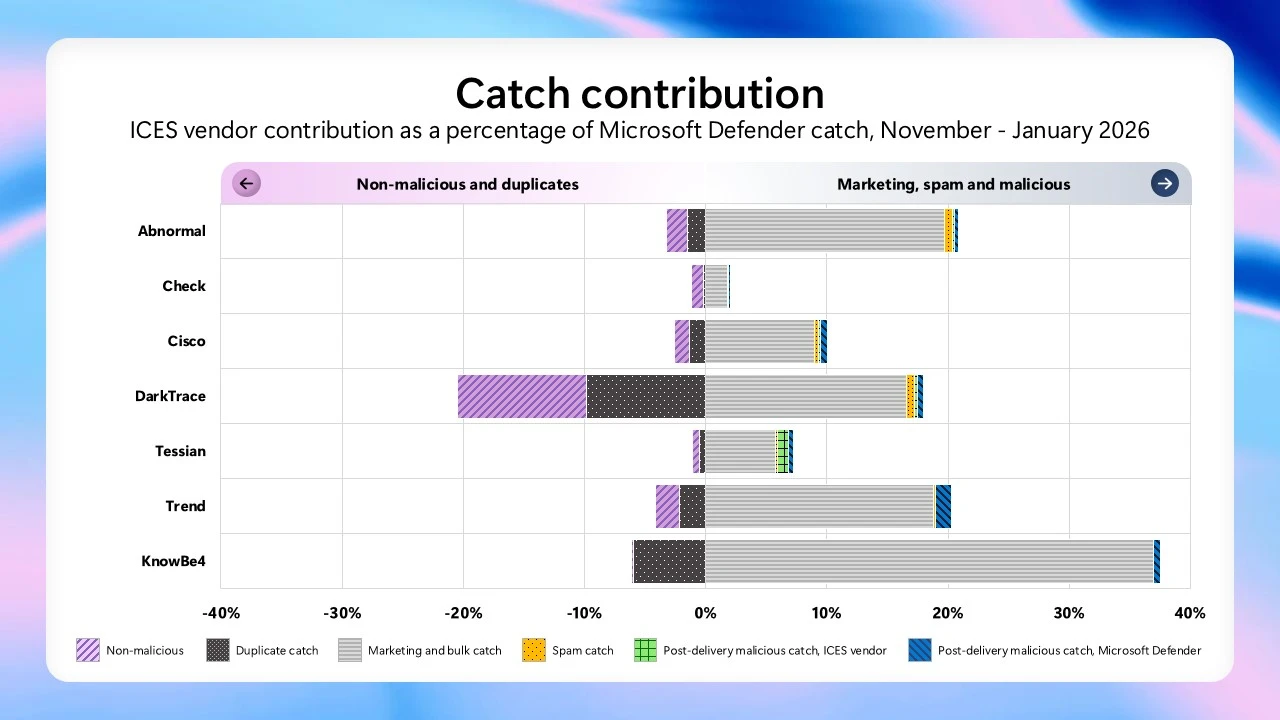
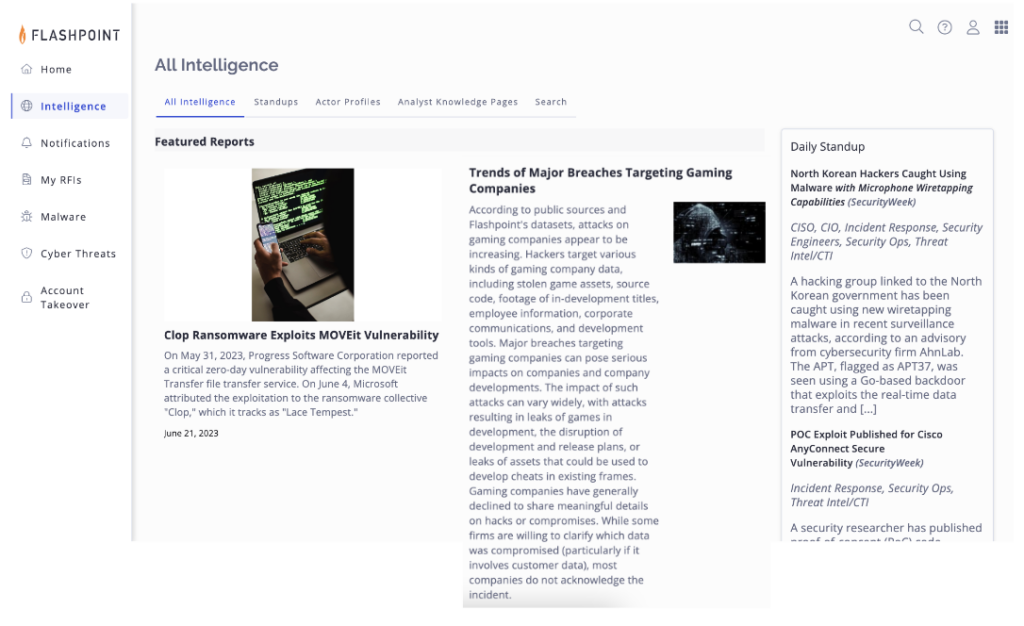
Threat intelligence shifts ransomware defense from reactive to preventive. By exposing active ransomware groups, exploited vulnerabilities, and compromised credentials, it gives teams clarity on where to focus first.
Instead of treating every alert the same, intelligence identifies what’s urgent and what’s noise. Teams can patch the vulnerabilities ransomware groups are exploiting right now, block their infrastructure, and monitor for leaked data.
Automation and AI amplify this advantage by correlating signals, flagging attack patterns, and triggering workflows faster than attackers can move.
Challenge
Intelligence Solution
Prioritizing vulnerabilities
Stolen credentials
Identifying unknown assets
Data leaks and brand damage
Third-party compromise
Emerging threats
Ransomware Is a Business Resiliency Test
Ransomware is a business-level risk, not just an IT problem. It simultaneously stresses operations, finances, and brand reputation while requiring coordination across legal, communications, operations, IT, and executive leadership.
Modern ransomware attacks expose how well an organization can maintain operations, safeguard trust, and recover under pressure. The organizations that weather these attacks most successfully are those that have invested in comprehensive, intelligence-driven security programs before an incident occurs.
According to Recorded Future’s State of Threat Intelligence 2025, 91% of enterprises plan to increase investment in threat intelligence over the next year, underscoring the industry-wide shift toward proactive, intelligence-driven resilience.
The most effective strategy is proactive defense. Threat intelligence gives organizations the visibility and speed to prevent, detect, and neutralize attacks before they escalate into business-threatening crises.
See how Recorded Future helps enterprises detect ransomware threats early, protect brand reputation, and recover faster.