People in certain professions, such as healthcare, law, and corporations, often rely on password protection when sending files via email, believing it provides adequate security against prying eyes. However, simple password protection on a PDF or Excel file is not as sure-fire as it may seem.
Protecting files with passwords without encrypting the data within is generally ineffective, as it can be easily circumvented. When experts refer to password protection as a security measure, they typically describe situations where a password is the sole method of accessing data, which usually has built-in protection against hacking, either through software or hardware encryption.
Most password protection methods use some form of encryption, but is there a clear choice between software and hardware encryption when it comes to protecting your personal or business files from theft, loss, or hacking?
Is “Password Protection” enough?
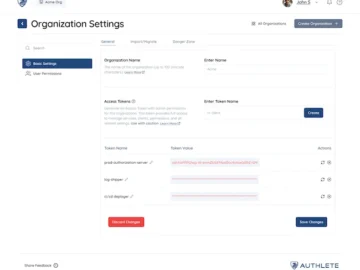
Many office applications provide a built-in option to “password-protect” files. These apps generally use software encryption on the files to protect the data. The level of encryption is not always specified to the user, who can be left unaware of what security technology is being used beyond the password protection.
For reference, Windows offers BitLocker encryption, which supports state-of-the-art Advanced Encryption Standard (AES) 256-bit and is the basic standard anyone should insist on for software encryption.
IT leaders value software encryption for its cost-effective implementation, lack of specialized hardware requirements, and easily licensable encryption software if needed. However, these conveniences create a false sense of security, as they come with serious security drawbacks and introduce a single point of failure. If hackers can utilize common attack methods, like social engineering, to extract a user’s password or encryption keys from a computer’s memory or obtain drive recovery keys, the encryption becomes ineffective.
Additionally, software encryption relies on your computer’s processing power, which can impact system performance when handling large encrypted files like images or videos.
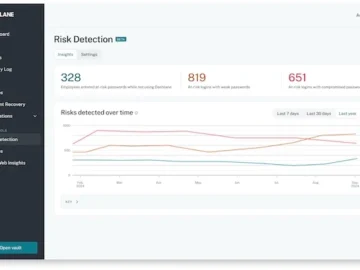
Most critically, software encryption does not prevent password guessing, often known as “brute force” or “dictionary” attacks, where hackers use automated tools to make millions of attempts in very short periods of time. This doesn’t require advanced or costly tools —many solutions for removing passwords and decrypting files are freely available online.
Given the prevalence of short passwords, typically around eight characters, and the capability of high-performance computers to guess billions of passwords per second, even robustly software-encrypted files can be accessed quickly by bad actors. In short, it takes just one failure or oversight to compromise your entire network.
Beyond software encryption
For environments where “nice-to-have” data security isn’t enough, hardware-encrypted drives are the best way to secure your data.
Unlike software encryption, hardware encryption is powered by a separate microprocessor dedicated to user authentication and data encryption. These processes are separated from the rest of the device, allowing a drive to protect against brute force attacks, making it exponentially harder to crack, if not nearly impossible, without a crypto-erase of the drive that destroys the data forever.
A dedicated security processor also means encryption processes can run much faster, as all data processing is handled on the device, not your computer.
Because of their components and design, hardware-encrypted drives cost more than software-encryption options, and can safeguard against theft or loss, providing greater physical layers of security.
A lost or stolen drive with well-designed hardware encryption does not generally constitute a data breach, as attempts to access data on that drive will cause it to wipe all contents. For companies held to privacy laws like HIPAA, GDPR, and CCPA, the initial premium of hardware-encrypted drive cost is quickly dwarfed by the legal and reputational cost of a breach.
Why invest in hardware encryption?
There are multiple reasons to recommend hardware-based encryption:
- Harder to attack: Hardware-encrypted drives are designed to resist attacks, with the ability to track the total password attempts and crypto-erase the drive after a certain number. Because of this, cybercriminals prioritize hacking software-based solutions as lower-hanging fruit.
- Physically and digitally resilient: Hardware-encrypted drives have added protections against physical tampering. They use epoxy to form a protective seal around a drive’s internal components, making them tamper-resistant against physical attacks. Best-in-class FIPS 140-3 Level 3 drives even have penetration-tested features like shutting down when excessive temperatures or voltages are reached and conduct a self-test when booting to detect anomalies.
- Portability: Hardware-encrypted USBs and external SSDs let you securely take your data outside of the office without common risks like emailing financial documents to an accountant or attorney or storing sensitive data on the cloud. An external drive allows you to back up as much as 8TB of data away from the internet in a location you control.
Recovering data
Data recovery is another point of distinction for hardware- and software-based encryption tech. With ransomware attacks rising, regular backups are critical to data recovery, and for all encryption choices, the best solution is a 3-2-1 backup strategy.
3. Make three copies of the data,
2. Make two different media or drives in case of failure or corruption
1. Store one drive in a separate location.
The prudent choice
At the end of the day, password protection can only offer a basic level of data security. For those requiring robust data protection, hardware encryption is should be the preferred method for safeguarding data.
With AES 256-bit encryption, resilience to brute force attacks, and dedicated microprocessors, it provides the enhanced level of security professionals and organizations need to deal with their sensitive data, making investing in secure methods like hardware encryption – not just a smart choice but a necessary one.