How They Got Hacked Episode Fifty Eight 58

Source link
Related Articles
All Mix →Your cybersecurity starter pack | victoria.dev
Basic security best practices to share with your non-technical friend. Readers of my blog typically know more about technology and cybersecurity than most people. This…
No. 381 Nurturing High-Performers, AI Business Takeover, Cyber Threats, and Diversifying Production 🌐🤖📱
*|INTERESTED:Memberful Plans:UL Subscription (Annual) (53074)|* *|END:INTERESTED|* *|INTERESTED:Memberful Plans:UL Subscription (Annual) (53074)|**|ELSE:|* *|END:INTERESTED|* Unsupervised Learning is a Security, AI, and Meaning-focused podcast that looks at how…
BUILD A RESILIENT SECURITY POSTURE WITH VULNERABILITY INTELLIGENCE AND CYBERSECURITY RATINGS
Reducing risk is the fundamental reason organizations invest in cybersecurity. The threat landscape grows and evolves, creating the need for a proactive, continual approach to…
AI is About to Feel Like AGI, and You Need to Get Ready
Created/Updated: November 21, 2022 I just wrote a piece similar to this last week, but this one drives the point home even more. Basically, the…
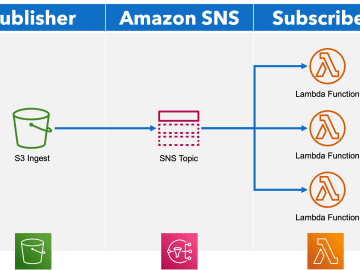
Exploiting Improper Validation of Amazon Simple Notification Service SigningCertUrl
Note: This is the “text notes” version of my DEF CON 30 Cloud Village Lightning Talk. The talk was not recorded so this is the…
Your First 90 Days as Security Lead, Part 1: Building Your Security Foundation
Congratulations! You’ve just been named the new security lead for your organization. You probably have many projects swirling through your mind, like addressing a critical…