How They Got Hacked Episode Fifty Eight 58

Source link
Related Articles
All Mix →A Highly Concise Summary of “Atlas Shrugged”
Here’s a clean little summary of Ayn Rand’s book, Atlas Shrugged, from this Wall Street Journal article: Sound familiar yet? The point of the piece…
XOXO: We Love Coinbase for Loving Bug Bounties
Besides being the world’s most popular way to buy and sell bitcoin, ethereum, and litecoin, Coinbase is a trailblazer in hacker-powered security. They started their…
A recap of the Q&A session on Twitter
A recap of the Q&A session on Twitter [This article was originally posted in June 2020. It disappeared from the blog when a data-center from…
Why is securing the external attack surface a hot topic for security experts right now?
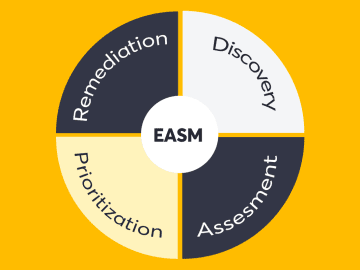
Table of Contents EASM – An Evolving Discipline of Security Implementing EASM in your organization Discovery Assessment Prioritization Remediation Common mistakes when implementing EASM Imbalance between…
Shopify Thanks Over 300 Hackers, Pays $850,000+ to Hackers in Three Years
Shopify’s commerce platform has awarded hackers more than $850,000 in bounties for helping secure its $55 billion-plus customer transactions and data. As a leading commerce…
Blackberry | Daniel Miessler
Got me a Blackberry. My old Nokia has been irking me as of late, and I have been wanting to get myself a new phone…