How They Got Hacked Episode Fifty Nine 59

Source link
Related Articles
All Mix →Keep it simple, Scanner | Blog
Table of Contents Merge conflicts 1. Complex code 2. Cognitive load 3. What usage showed Spring cleaning Tom Shelton-Lefley | 20 June 2023 at 14:02…
Buddhism’s Fundamental Contradiction
I apologize for being so late to the game here, but aren’t the Buddhist concepts of Karma and the inevitable unfolding of the universe inconsistent?…
The mutual benefits of bug bounty programs
Table of Contents Understanding bug bounty programs How do bug bounty programs benefit organizations? Strengthening organizational security Cost-effectiveness compared to traditional security measures Legal and…
The key to ensuring software quality and reliability
Table of Contents Bug reintroduction Broken functionality Increased technical debt Delayed time to market Damaged reputation What is retesting? How does regression testing differ from…
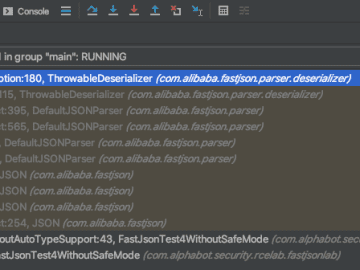
Fastjson: exceptional deserialization vulnerabilities – Alphabot Security
Table of Contents Intro Typical Fastjson RCEs (using the autoType-feature) Now it gets interesting… The global Fastjson instance How many autoType checks? But can you…
Broken Access Control – Lab #4 User role can be modified in user profile | Short Version
Broken Access Control – Lab #4 User role can be modified in user profile | Short Version Source link