How They Got Hacked Episode Fifty Nine 59

Source link
Related Articles
All Mix →Search in Zola: Fuse.js vs. Elasticlunr.js
Table of Contents What is Fuse.js and Elasticlunr.js? Why Compare These Two? Fuse.js: Simple and Powerful Fuzzy Search Elasticlunr.js: Advanced Search Option How to Integrate…
Would You Put AI Art In Your House?
Created/Updated: December 19, 2022 I’ve been thinking for a couple of weeks about making and hanging some AI art in my house. But I immediately…
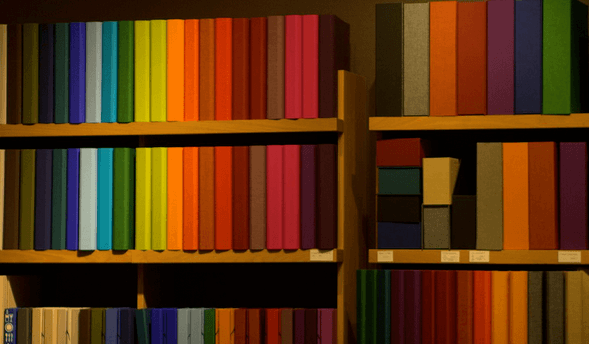
The Rainbow Book List | Daniel Miessler
OrangeDoD Trusted Computer System Evaluation Criteria GreenDoD Password Management Guideline TanA Guide to Understanding Audit in Trusted Systems Bright BlueTrusted Product Evaluations – A Guide…
More improvements to Attack Surface Custom Policies
Table of Contents Tl;dr We’ve made a few improvements to Attack Surface Custom Policies, such as viewing alerts more easily and deleting custom policies. We’ve…
Reflected XSS: Advanced Exploitation Guide
Table of Contents Reflected XSS Stored XSS DOM-based XSS Step 1: Reflection Step 2: Injection Step 3: Payload (proof of concept) Cross-site scripting vulnerabilities are,…