How They Got Hacked Episode Fifty Seven 57

Source link
Related Articles
All Mix →Pentesting for iOS Mobile Applications
Table of Contents iOS Testing Methodologies Common iOS Vulnerabilities Improper Credential Usage Insecure Authentication or Authorization Inadequate Privacy Controls iOS Best Practices Careful Scoping Skills-Based…
They are all Injection Vulnerabilities! – Security Simplified
They are all Injection Vulnerabilities! – Security Simplified Source link
The Real Future of Tech · Joseph Thacker
Table of Contents Good Calls Big Picture of The Future Bye In 2016, my friend Daniel Miessler wrote a book called “The Real Internet of…
The relentless rise of atmospheric CO2 since 1950
Table of Contents The numbers tell a stark story Why Mauna Loa matters The pre-industrial baseline What drives the acceleration? The path forward The Keeling…
Security and Obscurity: Does Changing Your SSH Port Lower Your Risk?
My opinion on security and obscurity is that obscurity can in fact help improve an already sound security posture. That’s keeping in mind that it…
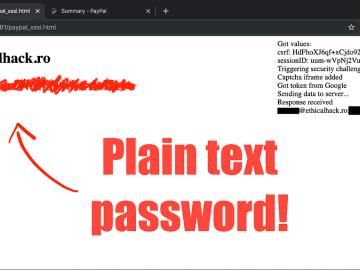
The Bug That Exposed Your PayPal Password
And Credit Card Number Too Continue reading on Medium » Source link