How They Got Hacked Episode Fifty Two 52

Source link
Related Articles
All Mix →Windows File Sharing: Facing the Mystery
Of course, nearly everyone is familiar with one main concept — the well-worn and widely known view that Windows file sharing services are potentially very…
Why I Think Google Chrome Will Be Highly Successful
I’m seriously impressed with Google’s newbile browser offering, Chrome. I like the simplicity of its interface, its speed, and most of all how it handles…
My OpenAI Event Predictions (May 2024)
Table of Contents What I anticipate All about agents A personal DA A mix of agent stuff Summary I don’t have any insider knowledge—unless you…
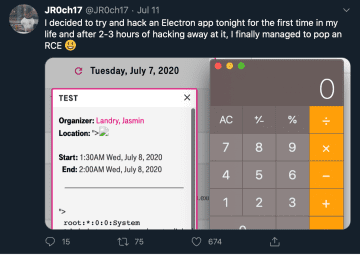
Open Sesame: Escalating Open Redirect to RCE With Electron Code Review | by Eugene Lim | The Startup
Table of Contents Discovering Vulnerable Config Attempting XSS Bypassing CSP The Room of Requirement Drive-By Code Execution For better or worse, Node.js has rocketed up…
Sponsored Interview: Pentera | Daniel Miessler
July 10, 2023 Daniel Miessler speaks with Aviv Cohen about Pentera’s Automated Security Validation platform, which is similar but different to automated pen testing and…
Introducing HackerOne Gateway Internal Network Testing: Superior Security for Internal Networks
Table of Contents Our Solution: Precision Internal Network Testing with Zero Trust Control Understanding Cloudflared and IPsec in Gateway INT Context Key Benefits Looking Ahead…