How They Got Hacked Episode Forty Eight 48

Source link
Related Articles
All Mix →The Story of the Million Dollar Bounty
On the evening of January 30th, I checked my phone one last time before going to bed as we millennials do to simulate waking up…
[tl;dr sec] #260 – Reddit’s Self Hosted Code Scanning, Build an Offensive AI Agent, OpenSSF’s Package Analysis
Table of Contents Reddit's flexible code scanner for any CLI tool, an agent that analyzes JS and tests routes, new tool to scan OSS packages…
Modern Science on Self-Control, and 4 Things You Can Do Immediately to Improve It
Table of Contents The Sugar Study The Wear and Tear Study The Abstract Thinking Study How to Raise Your Self-Control Image from scientificamerican.com Scientists are…
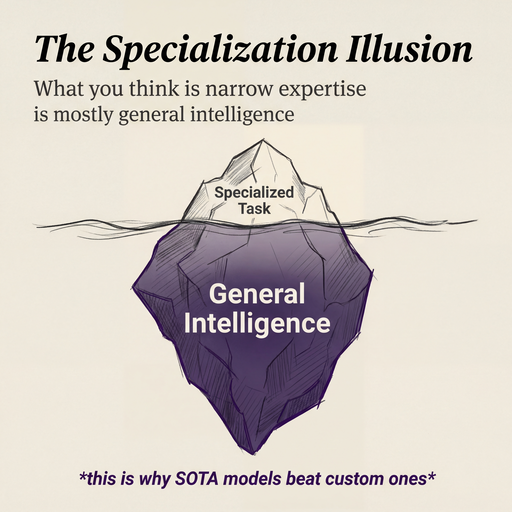
Why I believe in SOTA models over custom ones
I’ve never been a big believer in training custom models. I’ve also never believed in fine-tuning. Going all the way back to 2023, my intuition…
Hacker’s Health: Adverse Effects of Doomscrolling
Question: “I spend the majority of my time researching and keeping up with current affairs. I don’t feel like anything is wrong, but then I…
Performing a “Cold-Boot” Proof of Concept Without Princeton’s Bit-Unlocker
Most in the information security community have heard of the “cold-boot” attack against encryption products that was recently released by Princeton. They put out a…

![[tl;dr sec] #260 - Reddit's Self Hosted Code Scanning, Build an Offensive AI Agent, OpenSSF's Package Analysis](https://image.cybernoz.com/wp-content/uploads/2025/03/tldr-sec-260-Reddits-Self-Hosted-Code-Scanning-Build.png)