How They Got Hacked Episode Forty Nine 49

Source link
Related Articles
All Mix →[Integration] You can now integrate Detectify with Slack
Slack is the first of Detectify’s workflow integrations. One of the many advantages of Slack is that it’s a single point of contact for all the…
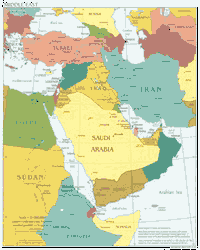
10 Things Everyone Should Know About the Middle East
Most people–especially in the West–know very little about the Middle East and the people that live there. This lack of knowledge hurts our ability to…
Free Will and Punishment
It seems to me that the decision, both as an individual and as a society, to either punish or rehabilitate criminals hinges on the degree…
HackerOne is a 2019 Cyber Catalyst Designated Cybersecurity Solution
HackerOne has been chosen as a 2019 Cyber CatalystSM designated cybersecurity solution. HackerOne Bounty was selected by Cyber Catalyst insurers as a solution that can…
Q: HOW do you get started in bug bounty?? How do you build your automation?!
Q: HOW do you get started in bug bounty?? How do you build your automation?! Source link
Hacker’s Health: Adverse Effects of Doomscrolling
Question: “I spend the majority of my time researching and keeping up with current affairs. I don’t feel like anything is wrong, but then I…