How They Got Hacked Episode Forty Six 46

Source link
Related Articles
All Mix →Some Thoughts on the Future of IT
I see the cloud as a means by which business units will disentangle themselves from internal IT shops, eventually moving to a model where internal…
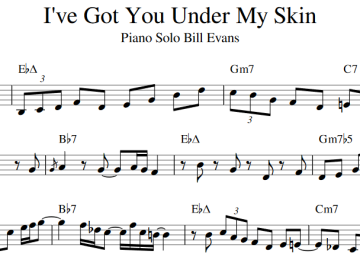
I’ve Got You Under My Skin, Bill Evans Solo Transcription – honoki
Download my transcription of Bill Evans’ piano solo in I’ve Got You Under My Skin below. The solo starts around the 1:04 mark on the…
Wallarm at Black Hat USA 2023 Booth #3131
Table of Contents Expo Hours Visit Our Booth Win A Nintendo Switch! Executive Briefing Wallarm is excited to be back at Black Hat USA this…
“I am the greatest!” New HackerOne Quarterly Leaderboards
Who was the greatest? Muhammad Ali of course. For hackers on HackerOne, the answer is on our new Leaderboard! HackerOne is proud to present the…
HackerOne in DevSecOps | HackerOne
I’m not going to define DevSecOps in yet another blog post. There are plenty of great resources for that. I do want to set the…
Take control of your security posture: The Burp Suite Enterprise Edition winter update | Blog
Table of Contents Manage your security, your way. Available now in Burp Suite Enterprise Edition Take control of your priorities by managing your own issue…