How to conduct a basic security code review | Security Simplified

Source link
Related Articles
All Mix →How To Find Broken Access Control Vulnerabilities in the Wild
Table of Contents What Is Broken Access Control? BAC Example 1: An e-commerce website allows unauthorized viewing of customer details BAC Example 2: A bank…
Unsupervised Learning Newsletter NO. 384
Unsupervised Learning is a Security, AI, and Meaning-focused podcast that looks at how best to thrive as humans in a post-AI world. It combines original…
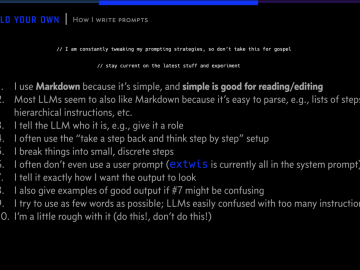
How To Write Effective AI Prompts (Updated)
Table of Contents I use Markdown because it’s simple, and simple is good for reading/editing. Most LLMs seem to also like Markdown because it’s easy…
IQ Is Real, And It Matters
I was just reading through this list of questions that Microsoft asks applicants and was struck by the thought that we, as a society, should…
Hacker News is the New Reddit
Anyone who likes Reddit needs to check out another similar site called Hacker News. It’s rather like Reddit used to be before it went mainstream,…
[tl;dr sec] #184 – Public Cloud Security Breaches, OWASP Top 10 for LLMs, Living Off the Orchard: macOS Binaries
Table of Contents Oops! AGI Did It Again 📢 Secure remote access to shared resources 📜 In this newsletter… AppSec Web Security 📢 GitGuardian just…