How to learn anything in Computer Science or Cybersecurity | Security Simplified

Source link
Related Articles
All Mix →Integrate HackerOne directly into your website with Embedded Submissions
Receiving vulnerabilities has never been easier with the release of our newest integration: Embedded Submissions. What started with Email forwarding in 2017, is now being…
Keep the Robots Out of the Gym
AI is getting so good now (at the end of 2025) that I now have a new, primary recommendation going into 2026: Think very carefully…
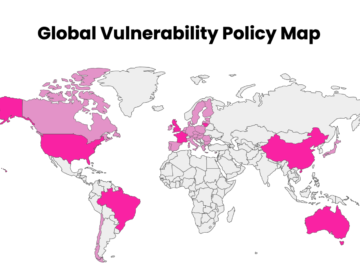
How To Use HackerOne’s Global Vulnerability Policy Map
To help organizations keep up with the shifting landscape of VDP mandates and recommendations, HackerOne has developed the Global Vulnerability Policy Map, an interactive map-based…
A Practical Guide to Investigating IoT Devices with the SecurityTrails API
The last decade is arguably one of exceptional growth and transformation, with technologies like the Internet of Things (IoT) leading us to add sensory awareness…
Hive Five 208 – Nobody Cares
Table of Contents The Bee's Knees Fyxer AI: Automate Emails, Meetings, and Team Tasks in Seconds Table of Contents Updates Work Level up Explore Learned…
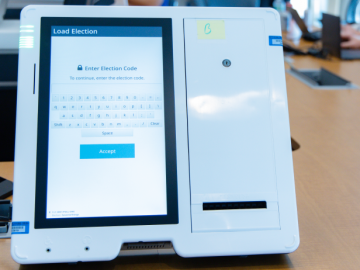
Boosting Election Integrity With Coordinated Vulnerability Disclosure [4 Insights]
Table of Contents 1. This year, The first collaborative engagement dedicated to establishing trust and demonstrating progress through coordinated vulnerability disclosure occurred at the Election…