Impostor Syndrome and How we Talk about it in Infosec

Source link
Related Articles
All Mix →Intigriti insights: React2Shell CVE-2025-55182 | Intigriti
This blog explores the widespread and critical state of the React2Shell vulnerability. It provides a technical overview, suggested mitigations, and actions to safeguard people, processes,…
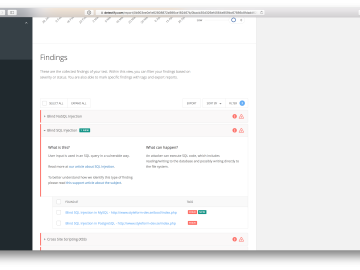
5 things we’ve done to make your Detectify experience better
Table of Contents 1) More transparency on what tests we have performed 2) Manual findings export to JIRA 3) See what findings are new 4)…
An Attorney’s View of Vulnerability Disclosure
Vulnerability Disclosure Programs (VDPs) are not only being promoted by more and more organizations and officials, they’re an easy-to-implement yet critical part of any company’s…
Dalfox 2.10 Released ︎ | HAHWUL
Table of Contents What’s New in v2.10.0? Performance Breakthrough More Highlights Cleaner Code Bug Fixes Thank You Get It Here Final Thoughts Mar 24, 2025…
Continuously Hack Yourself because WAF security is not enough
Table of Contents WAF’s Got My Back… right? Scanners Gonna Scan Signatures vs. Payloads Trusting ethical hackers to help verify relevant vulnerabilities How to Continuously…