Impostor Syndrome and How we Talk about it in Infosec

Source link
Related Articles
All Mix →Measuring productivity with GitHub issues
Table of Contents Getting quality data Plotting with Pandas You aim for what you measure How long does it take for a bug to get…
Huxley vs. Orwell: Whose Dystopia is Winning?
I posted here an absolutely brilliant and terrifying political cartoon. It’s about the way in which America (the West?) will fall. Will it be due…
DLL Hijacking via URL files
This blogpost describes how I got annoyed by vulnerabilities in 3rd party Windows applications, which allowed to execute local files but without parameters. So I…
How can I scope third-party assets?
You asked, and we answered. At Intigriti, we’ve been paying close attention to the questions most frequently asked by those with a bug bounty program…
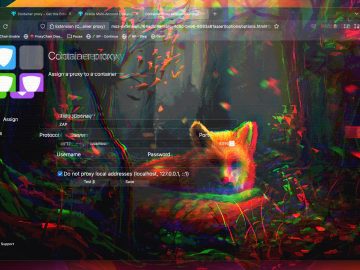
Firefox + Container + Proxy = Hack Env
Table of Contents TL;DR Container x Proxy Install Addons Multi-Account Containers Container Proxy Set-up Set Containers Set Proxy for Containers Go! Only Multi-Account Containers Conclusion…
Yes. LLMs can create convincingly human output. · rez0
Table of Contents Why So Serious Strategies For Generating Human-like Text Full Examples With Real Output Conclusion Why LLMs don’t sound human, strategies to fix…