Statistics across all threats
The percentage of ICS computers on which malicious objects were blocked has been decreasing since the beginning of 2024. In Q4 2025, it was 19.7%. Over the past three years, the percentage has decreased by 1.36 times, and by 1.25 times since Q4 2023.
Percentage of ICS computers on which malicious objects were blocked, Q1 2023–Q4 2025
Regionally, in Q4 2025, the percentage of ICS computers on which malicious objects were blocked ranged from 8.5% in Northern Europe to 27.3% in Africa.
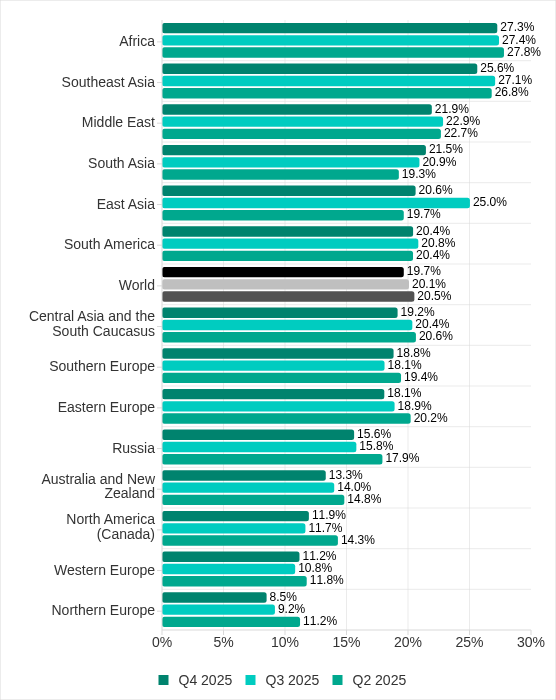
Regions ranked by percentage of ICS computers on which malicious objects were blocked
Four regions saw an increase in the percentage of ICS computers on which malicious objects were blocked. The most notable increases occurred in Southern Europe and South Asia. In Q3 2025, East Asia experienced a sharp increase triggered by the local spread of malicious scripts, but the figure has since returned to normal.
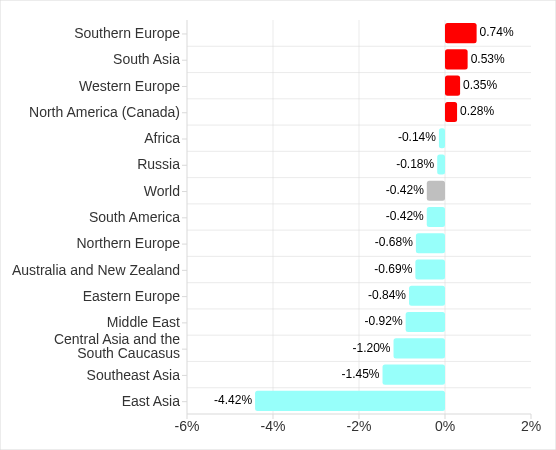
Changes in percentage of ICS computers on which malicious objects were blocked, Q4 2025
Feature of the quarter: worms in email
In Q4 2025, the percentage of ICS computers on which wormsinemailattachments were blocked increasedinallregions of the world.
Many of the blocked threats were related to the worm Backdoor.MSIL.XWorm. This malware is designed to persist on the system and then remotely control it.
Interestingly, this threat was not detected on ICS computers in the previous quarter, yet it appeared in all regions in Q4 2025.
A study found that the active spread of Backdoor.MSIL.XWorm via phishing emails was likely linked to the use by hackers of another malware obfuscation technique that was actively used during massive phishing campaigns in Q4 2025. These campaigns have been known since 2024 as “Curriculum-vitae-catalina”.
The attackers distributed phishing emails to HR managers, recruiters, and employees responsible for hiring. The messages were disguised as responses from job applicants with subjects such as “Resume” or “Attached Resume” and contained a malicious executable file under the guise of a curriculum vitae. Typically, the file was named Curriculum Vitae-Catalina.exe. When executed, it infected the system.
In Q4 2025, the threat spread across regions in two waves — one in October and another in November. Russia, Western Europe, South America, and North America (Canada) were attacked in October. A spike in Backdoor.MSIL.XWorm blocking was observed in other regions in November. The attack subsided in all regions in December.
The highest percentage of ICS computers on which Backdoor.MSIL.XWorm was blocked was observed in regions where threats from email clients had been historically blocked at high rates on ICS computers: Southern Europe, South America, and the Middle East.
At the same time, in Africa, where USB storage media are still actively used, the threat was also detected when removable devices were connected to ICS computers.
Selected industries
The biometrics sector has historically led the rankings of industries and OT infrastructures surveyed in this report in terms of the percentage of ICS computers on which malicious objects were blocked.
These systems are characterized by accessibility to and from the internet, as well as minimal cybersecurity controls by the consumer organization.
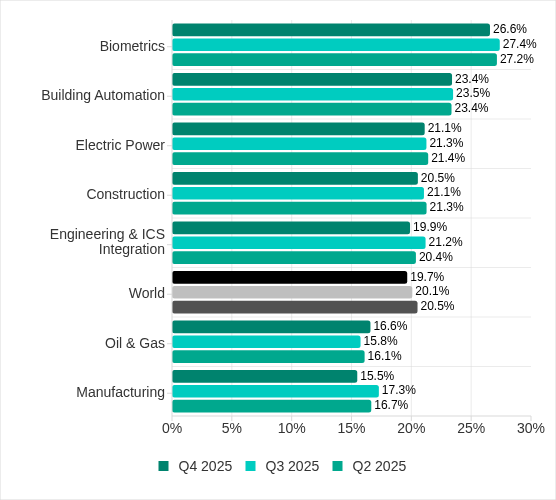
Rankings of industries and OT infrastructure by percentage of ICS computers on which malicious objects were blocked
In Q4 2025, the percentage of ICS computers on which malicious objects were blocked increased only in one sector: oil and gas. The corresponding figures increased in two regions: Russia, and Central Asia and the South Caucasus.
However, if we look at a broader time span, there is a downward trend in all the surveyed industries.
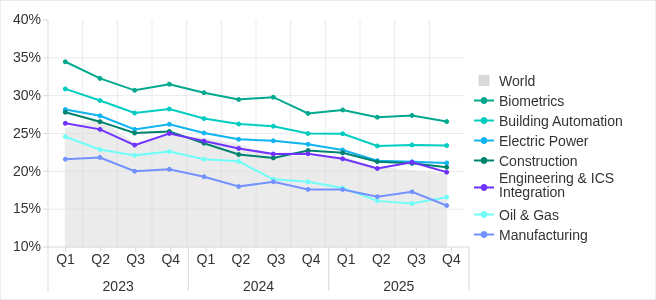
Percentage of ICS computers on which malicious objects were blocked in selected industries
Diversity of detected malicious objects
In Q4 2025, Kaspersky protection solutions blocked malware from 10,142 different malware families of various categories on industrial automation systems.
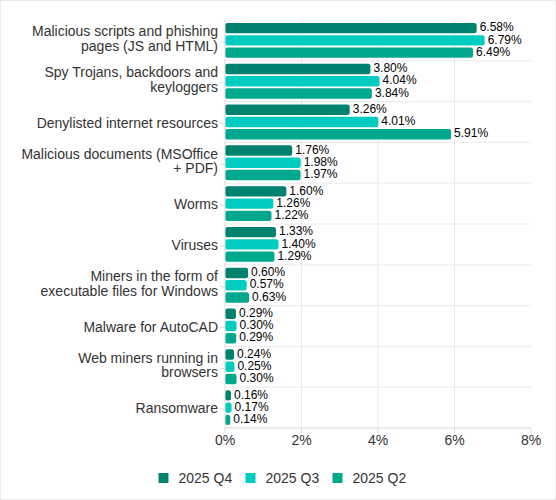
Percentage of ICS computers on which the activity of malicious objects from various categories was blocked
In Q4 2025, there was an increase in the percentage of ICS computers on which worms, and miners in the form of executable files for Windows were blocked. These were the only categories that exhibited an increase.
Main threat sources
Depending on the threat detection and blocking scenario, it is not always possible to reliably identify the source. The circumstantial evidence for a specific source can be the blocked threat’s type (category).
The internet (visiting malicious or compromised internet resources; malicious content distributed via messengers; cloud data storage and processing services and CDNs), email clients (phishing emails), and removable storage devices remain the primary sources of threats to computers in an organization’s technology infrastructure.
In Q4 2025, the percentage of ICS computers on which malicious objects from various sources were blocked decreased. All sources except email clients saw their lowest levels in three years.
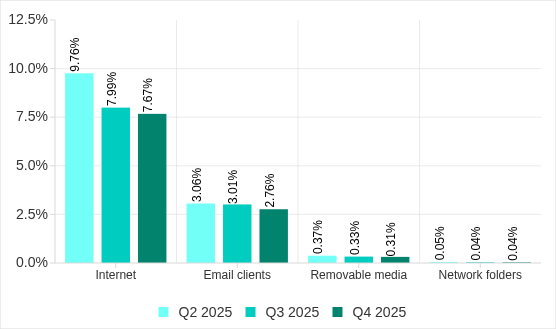
Percentage of ICS computers on which malicious objects from various sources were blocked
The same computer can be attacked by several categories of malware from the same source during a quarter. That computer is counted when calculating the percentage of attacked computers for each threat category, but is only counted once for the threat source (we count unique attacked computers). In addition, it is not always possible to accurately determine the initial infection attempt. Therefore, the total percentage of ICS computers on which various categories of threats from a certain source were blocked can exceed the percentage of computers affected by the source itself.
- In Q4 2025, the percentage of ICS computers on which threats from the internet were blocked decreased to 7.67% and reached its lowest level since the beginning of 2023. The main categories of internet threats are malicious scripts and phishing pages, and denylisted internet resources. The percentage ranged from 3.96% in Northern Europe to 11.33% in South Asia.
- The main categories of threats from email clients blocked on ICS computers were malicious scripts and phishing pages, spyware, and malicious documents. Most of the spyware detected in phishing emails was delivered as a password archive or a multi-layered script embedded in office document files. The percentage of ICS computers on which threats from email clients were blocked ranged from 0.64% in Northern Europe to 6.34% in Southern Europe.
- The main categories of threats that were blocked when removable media was connected to ICS computers were worms, viruses, and spyware. The percentage of ICS computers on which threats from removable media were blocked ranged from 0.05% in Australia and New Zealand to 1.41% in Africa.
- The main categories of threats that spread through network folders in Q4 2025 were viruses, AutoCAD malware, worms, and spyware. The percentage of ICS computers on which threats from network folders were blocked ranged from 0.01% in Northern Europe to 0.18% in East Asia.
Threat categories
Typical attacks blocked within an OT network are multi-step sequences of malicious activities, where each subsequent step of the attackers is aimed at increasing privileges and/or gaining access to other systems by exploiting the security problems of industrial enterprises, including OT infrastructures.
Malicious objects used for initial infection
In Q4 2025, the percentage of ICS computers on which denylisted internet resources were blocked decreased to 3.26%. This is the lowest quarterly figure since the beginning of 2022, and it has decreased by 1.8 times since Q2 2025.
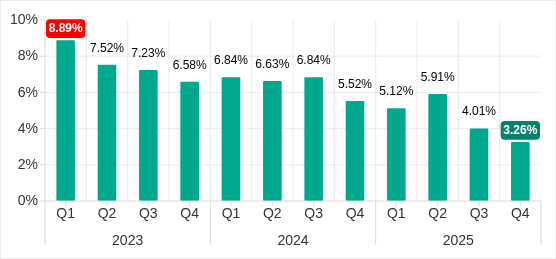
Percentage of ICS computers on which denylisted internet resources were blocked, Q1 2023–Q4 2025
Regionally, the percentage of ICS computers on which denylisted internet resources were blocked ranged from 1.74% in Northern Europe to 3.93% in Southeast Asia, which displaced Africa from first place. Russia rounded out the top three regions for this indicator.
The percentage of ICS computers on which malicious documents were blocked increased for three consecutive quarters. However, in Q4 2025 it decreased by 0.22 pp to 1.76%.
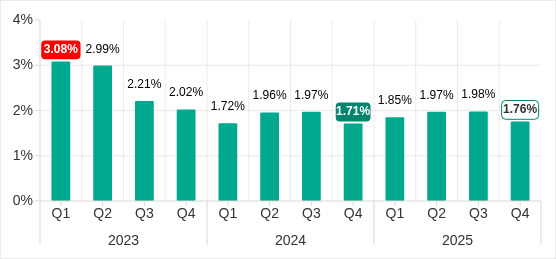
Percentage of ICS computers on which malicious documents were blocked, Q1 2023–Q4 2025
Regionally, the percentage ranged from 0.46% in Northern Europe to 3.82% in Southern Europe. In Q4 2025, the indicator increased in Eastern Europe, Russia, and Western Europe.
The percentage of ICS computers on which malicious scripts and phishing pages were blocked decreased to 6.58%. Despite the decline, this category led the rankings of threat categories in terms of the percentage of ICS computers on which they were blocked.
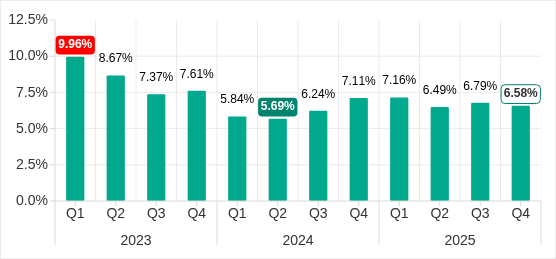
Percentage of ICS computers on which malicious scripts and phishing pages were blocked, Q1 2023–Q4 2025
Regionally, the percentage ranged from 2.52% in Northern Europe to 10.50% in South Asia. The indicator increased in South Asia, South America, Southern Europe, and Africa. South Asia saw the most notable increase, at 3.47 pp.
Next-stage malware
Malicious objects used to initially infect computers deliver next-stage malware — spyware, ransomware, and miners — to victims’ computers. As a rule, the higher the percentage of ICS computers on which the initial infection malware is blocked, the higher the percentage for next-stage malware.
In Q4 2025, the percentage of ICS computers on which spyware, ransomware and web miners were blocked decreased. The rates were:
- Spyware: 3.80% (down 0.24 pp). For the second quarter in a row, spyware took second place in the rankings of threat categories in terms of the percentage of ICS computers on which it was blocked.
- Ransomware: 0.16% (down 0.01 pp).
- Web miners: 0.24% (down 0.01 pp), this is the lowest level observed thus far in the period under review.
The percentage of ICS computers on which miners in the form of executable files for Windows were blocked increased to 0.60% (up 0.03 pp).
Self-propagating malware
Self-propagating malware (worms and viruses) is a category unto itself. Worms and virus-infected files were originally used for initial infection, but as botnet functionality evolved, they took on next-stage characteristics.
To spread across ICS networks, viruses and worms rely on removable media and network folders and are distributed in the form of infected files, such as archives with backups, office documents, pirated games and hacked applications. In rarer and more dangerous cases, web pages with network equipment settings, as well as files stored in internal document management systems, product lifecycle management (PLM) systems, resource management (ERP) systems and other web services are infected.
In Q4 2025, the percentage of ICS computers on which worms were blocked increased by 1.6 times to 1.60%. As mentioned above, this increase is related to a global phishing attack that spread the Backdoor.MSIL.XWorm backdoor worm across all regions of the world. The percentage increased in all regions. The biggest increase (up by 2.16 times) was in Southern Europe. The malware was primary distributed through email clients, and Southern Europe led the way in terms of the percentage of ICS computers on which threats from email clients were blocked.
The percentage of ICS computers on which viruses were blocked decreased to 1.33%.
AutoCAD malware
This category of malware can spread in a variety of ways, so it does not belong to a specific group.
After an increase in the previous quarter, the percentage of ICS computers on which AutoCAD malware was blocked decreased to 0.29% in Q4 2025.
For more information on industrial threats see the full version of the report.


![Fake CAPTCHA page at the URL https://evs.grupotuis[.]buzz/0capcha17/](https://image.cybernoz.com/wp-content/uploads/2026/03/How-we-uncovered-a-Horabot-campaign-and-how-you-can-468x340.png)