Info stealers and how to protect against them

Info stealers, the type of malware with its purpose in the name, can cripple businesses and everyday users alike. So, how do you protect against them?
Info stealers, also known as information stealers, are a type of malicious software (malware) designed to covertly collect sensitive and personal information from a victim’s computer or network. These pieces of malware are created with the intent of stealing valuable data, such as login credentials, financial information, personal details, and more.
- Info stealers are specifically designed to capture and transmit data from the infected system. This data may include usernames, passwords, credit card numbers, social security numbers, and other sensitive information.
- Info stealers can be delivered through various means, including malicious email attachments, infected websites, or as a payload delivered by other types of malware.
- Once installed on a system, info stealers often aim to remain undetected for as long as possible. They may use various tactics to evade antivirus and other security measures.
- Many info stealers are additionally equipped with remote control capabilities, allowing the attacker to manage the malware and extract data remotely.
- Info stealers can target individuals, businesses, or organizations, depending on the goals of the attackers. High-profile targets may be chosen for the potential value of the stolen information.
- There are various types of info stealers, each with its own specific focus. For example, some may target login credentials, while others may focus on financial data or intellectual property.
- Some info stealers may use encryption techniques to hide their communication with command-and-control servers, making it more challenging for security systems to detect malicious activities.

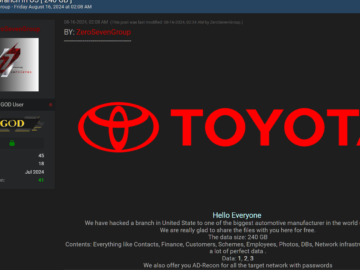
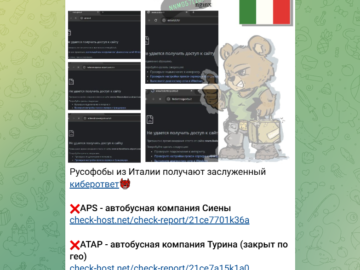
Trade on the dark web
Our research team explored some Telegram channels and Dark Web markets and found some info stealers for sale.


It’s worth mentioning that there are many more info stealers, as they’re often stored in private dark web markets or forums and not available for random users.
Our research team also found some bank logs for sale, info stealers were possibly used to steal these logs.

“Cashout bank logs” typically refer to a type of cybercrime where individuals gain unauthorized access to banking information, often through phishing attacks or hacking, and then use that information to withdraw money or make unauthorized transactions.
- Bank logs: These are sets of data containing sensitive information about a bank account. This information can include login credentials (username and password), account numbers, and other details that allow someone to access and control the account.
- Cashout: The term “cashout” refers to the process of extracting money from compromised bank accounts. This can be done through various means, such as making unauthorized withdrawals from ATMs, transferring funds to other accounts, or making fraudulent purchases.
- Illegal activities: Accessing someone else’s bank account information without authorization is illegal and considered a form of cybercrime. It violates privacy and security regulations, and individuals involved in such activities can face severe legal consequences.
Key takeaways
- Cybercriminals’ infrastructure often includes several common denominators, such as email addresses and Telegram channels to communicate with customers.
- Aspiring cybercriminals no longer require the technical skills to use info stealers and conduct cybercrime. As little as $150 to run a malware campaign with a multi-featured cybercrime tool will do the trick.
- Cybercriminals can sell not only bank logs but other kinds of logs, like session cookies with sensitive information, and more.
- In this Cybernews article Mars was mentioned. Mars is not ransomware but an info stealer – there are some associations between the two. For example, both ransomware and info stealers target Bitcoin. Ransomware was discovered in late 2020, while info stealer was discovered in June 2021. It’s possible that the “CheckMate” campaign also used the Mars infostealer.
Do you want to know how do we protect against info stealers?
Take a look at the original post at
https://cybernews.com/security/info-stealers-protection-explained/
About the author: Mantas Kasiliauskis, Information Security Researcher at CyberNews
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, Info stealers)