Daniel Rhyne, a 59-year-old former core infrastructure engineer, pleaded guilty on April 1, 2026, to federal hacking and extortion charges.
He admitted to locking out administrators and sabotaging systems at his former New Jersey-based employer in an attack that began in November 2023. Rhyne entered his plea before U.S. District Judge Michael A. Shipp in a Trenton federal court.
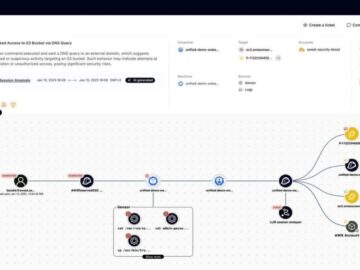
Rhyne deployed an unauthorized hidden virtual machine to access the company’s domain controller via remote desktop sessions.
From this concealed environment, he created automated scheduled tasks designed to systematically compromise the victim’s network.
These tasks were programmed to delete 13 domain administrator accounts and change the passwords of 301 domain users to “TheFr0zenCrew!”.
Massive Impact on Infrastructure
The malicious scheduled tasks targeted local administrator credentials across the industrial company’s extensive IT infrastructure.
This action effectively locked the organization out of 254 Windows servers and 3,284 employee workstations.
Furthermore, Rhyne scheduled commands to randomly shut down dozens of critical servers over several days in December 2023.
On November 25, 2023, Rhyne executed the cyberattack and sent an alarming email to employees titled “Your Network Has Been Penetrated”, as reported by Court Document.
He demanded a ransom of 20 Bitcoin, which was valued at approximately $750,000 at the time of the incident. The message threatened that 40 servers would be shut down daily for ten days if the payment was not received.
Rather than using advanced malware, Rhyne leveraged built-in administrative tools to avoid detection while orchestrating the attack.
He utilized the “net user” command-line utility to modify domain accounts and eliminate existing network administrators.
Additionally, he deployed the Sysinternals “PsPasswd” tool to remotely alter local administrative credentials across thousands of corporate endpoints.
Investigators discovered that Rhyne’s company laptop was previously used to search for specific commands on how to remotely change local administrator passwords.
Remote access logs also showed unauthorized connections originating directly from his home IP address in Warren County, New Jersey.
Authorities ultimately confirmed his identity when they found that the extortion email account used the exact same “TheFr0zenCrew!”
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.