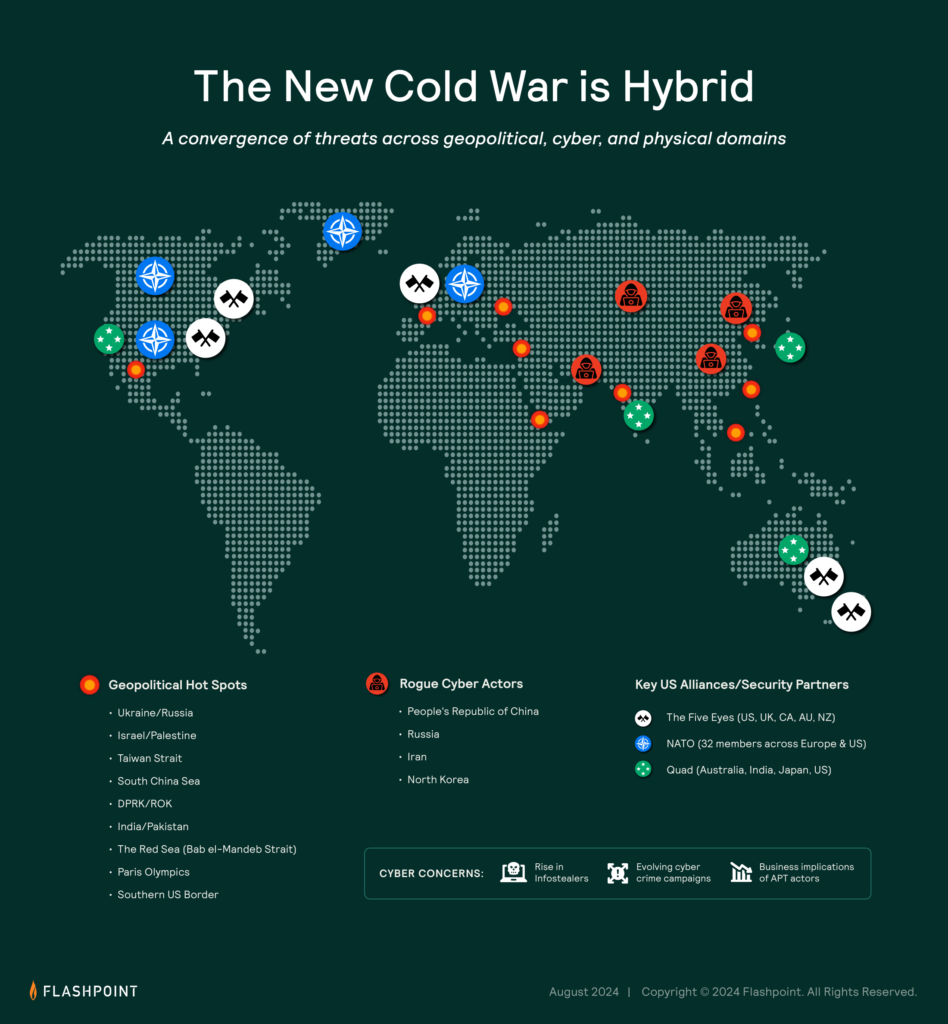
In 2026, the threat landscape operates as a single, connected system. Identity, malware, and infrastructure are now part of the same attack chain, executed at a speed that compresses the time between access and impact.
What once required multiple stages and specialized tooling is now streamlined and automated.
Flashpoint recently hosted an on-demand webinar, “Inside the 2026 Cyber Threat Landscape: Data-Driven Security Priorities,” where our intelligence team broke down the trends driving this shift. Drawing from primary source intelligence across forums, marketplaces, and closed communities, the session examined how modern attack chains are forming and evolving, as well as where defenders still have opportunities to intervene.
Here are the key takeaways you need to know to prioritize threats and protect your organization.
AI Is Being Operationalized Across the Attack Lifecycle
Artificial intelligence is now embedded across multiple stages of attacker workflows.
Flashpoint tracked more than 1.5 billion mentions of AI in illicit communities in 2025, with activity accelerating sharply toward the end of the year. These discussions center on how AI can be applied to real operations, including phishing, malware development, and fraud.
As Ian Gray, Vice President of Intelligence at Flashpoint, noted during the session, “Adversaries are extremely adept, and they’re constantly looking at how they can use the newest state-of-the-art tools—whether that’s commercial models or their own implementations—and how they can jailbreak them or adapt them to their workflows.”
One of the most notable developments is the use of agentic AI systems to automate tasks that were previously manual. These systems are being used to:
- Test stolen credentials across VPNs, SaaS platforms, and cloud environments
- Rotate infrastructure during active operations
- Generate and refine attack inputs based on previous outcomes
Alongside this, threat actors are actively exploring ways to bypass safeguards in commercial AI tools, including:
- Jailbreaking model restrictions
- Embedding hidden instructions through prompt injection
- Manipulating AI-powered features within enterprise applications
This activity reflects a sustained effort to integrate AI directly into attack execution rather than treating it as a standalone capability.
Identity Is Driving Initial Access
The fundamental mechanics of cybercrime have shifted from breaking in to logging in, as attackers leverage stolen session cookies to behave like legitimate users.
As Gray explained, “Threat actors are finding a variety of ways to get into enterprise networks, and typically it’s through the human element. While humans can be trained or educated, it’s not something that can be patched in the traditional sense.”
This dynamic is already visible at scale.
Flashpoint observed 11.1 million infected devices and 3.3 billion stolen credentials in 2025. These credentials are extracted through infostealers and circulated across marketplaces, enabling direct access into enterprise environments.
In many cases, attackers are using:
- Session cookies and tokens to bypass authentication flows
- Browser fingerprints and system metadata to replicate legitimate user behavior
- Valid credentials to access SaaS platforms, VPNs, and internal systems
Once access is established, activity often blends into normal user behavior, making detection more difficult. Compromised identities are also reused across multiple services, expanding the scope of potential exposure.
This pattern continues to appear in intrusion activity tied to SaaS platforms and third-party integrations, where access to one system can provide visibility into multiple environments.
Infostealers Are Enabling Scalable Access
Infostealers remain a primary driver of credential exposure.
Logs containing credentials, cookies, and system data are continuously harvested and made available through criminal marketplaces and subscription-based services. These logs are used directly or integrated into automated workflows that test and validate access at scale.
Gray pointed to how this plays out in practice: “Infostealers have really commoditized access. They harvest credentials, identify which ones are useful, and then test them at scale across VPNs, SaaS platforms, and cloud environments.”
The ecosystem continues to shift as law enforcement activity disrupts established players and new variants gain traction. Families such as Vidar, Lumma, and others maintain a strong presence due to accessibility and ongoing development.
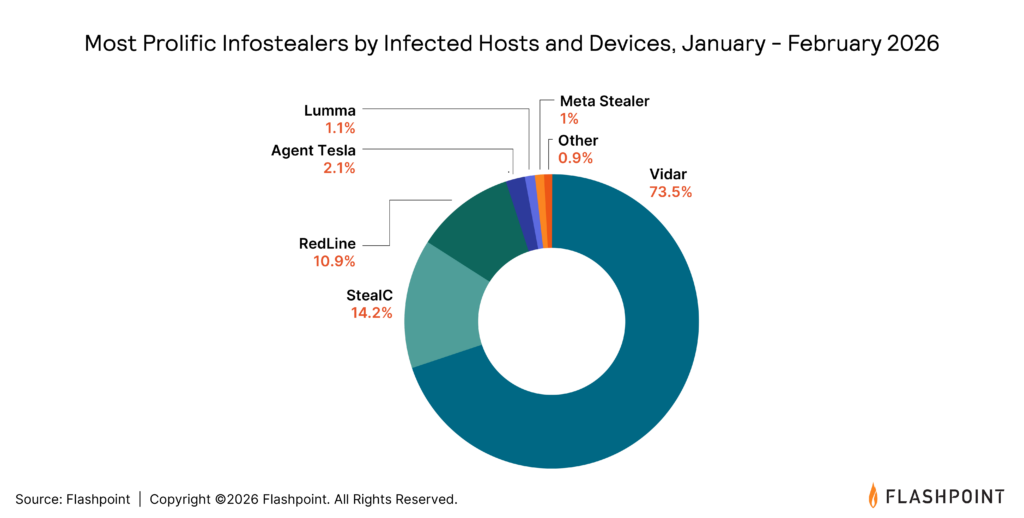
In parallel, credential harvesting is feeding downstream activity, including:
- Account takeover
- Fraud operations
- Data exfiltration and extortion
This linkage between initial access and follow-on activity is consistent across multiple reporting streams.
Vulnerability Exploitation Is Moving Faster
Vulnerability volume continues to increase alongside exploitation speed.
Flashpoint recorded more than 44,000 disclosed vulnerabilities in 2025, with over 14,000 tied to publicly available exploits. In several cases, exploitation activity followed disclosure within a day.
As Gray put it, “With vulnerabilities, it can feel like you’re trying to boil the ocean. There’s such a high volume of disclosures, but in reality, there’s a smaller set—those that are remotely exploitable, have proof-of-concept code, and are being actively used—that you need to focus on.”
Attacker focus is concentrated in areas that provide broad access or downstream impact, including:
- Software supply chains and CI/CD environments
- Open-source dependencies
- Widely used enterprise platforms
Given the volume of disclosures, prioritization remains critical. Vulnerabilities that are remotely exploitable and paired with public exploit code present immediate risk, particularly when active discussion or exploitation is observed.
Ransomware Activity Continues to Shift
Ransomware activity increased by 53%, with continued changes in how operations are carried out.
Gray framed the shift this way: “Why even bother to develop ransomware? That takes time, resources, and overhead—when you can gain access through a compromised account or third-party platform and immediately move to extortion.”
In addition to traditional ransomware deployment, there is sustained activity centered on:
- Data exfiltration followed by extortion
- Use of compromised credentials for direct access
- Targeting of third-party providers and SaaS platforms
Intrusions tied to help desks, identity workflows, and federated applications continue to appear in reporting, often involving social engineering or unauthorized access provisioning.
There is also ongoing activity related to insider recruitment, with threat actors seeking individuals who can provide direct access or privileged information.
Industries with higher operational dependencies, including manufacturing, technology, and healthcare, continue to be targeted due to the potential impact of disruption.
Translating Intelligence Into Action
The trends shaping 2026 are grounded in how attackers are currently operating across multiple domains.
As Gray emphasized, “You have to take into account vulnerabilities, exposures, infostealers, and identity compromise all at the same time. These aren’t separate problems anymore—they’re all part of the same attack chain.”
Security teams should focus on:
- Identifying exposures with a high likelihood of exploitation
- Monitoring for compromised credentials tied to organizational domains
- Reviewing identity access and third-party integrations
- Prioritizing vulnerabilities with active exploit availability
- Tracking attacker activity across forums, marketplaces, and communication channels
These actions align with observed attacker behavior and provide a clearer path to prioritization.
Watch the Full Webinar and Explore the Data
The trends shaping 2026 are grounded in how attackers are already operating.
Flashpoint’s full webinar provides a deeper look at the data, along with practical guidance on how to translate intelligence into action.
Watch the on-demand session to see the full breakdown of these trends, or download the 2026 Global Threat Intelligence Report to explore the underlying data and analysis in more detail.