Inside ZionSiphon: politically driven malware aims at Israeli water systems

New ZionSiphon malware targets water systems, and allows attackers to alter pressure and chlorine levels. A flaw makes it ineffective for now.
Darktrace analyzed ZionSiphon, a new malware designed to target water treatment and desalination systems, which aims to disrupt operations by altering hydraulic pressure and increasing chlorine levels to unsafe levels.
The malware combines common techniques like privilege escalation, persistence, and spreading via removable media with logic tailored to operational technology environments. ZionSiphon scans networks for OT services, modifies configurations, and focuses on Israeli targets using hardcoded IP ranges. Its code also contains political messages, suggesting ideological motives. However, parts of the implementation appear incomplete, indicating it may still be under development despite its potentially disruptive intent.
“The clearest indicators of intent in this sample are its hardcoded Israel-focused targeting checks and the strong political messaging found in some strings in the malware’s binary.” reads the report published by Darktrace. “In the class initializer, the malware defines a set of IPv4 ranges, including “2.52.0.0-2.55.255.255”, “79.176.0.0-79.191.255.255”, and “212.150.0.0-212.150.255.255”, indicating that the author intended to restrict execution to a narrow range of addresses. All of the specified IP blocks are geographically located within Israel.”
ZionSiphon includes Base64-encoded strings revealing clear political messaging, supporting groups opposing Israel and referencing harm to cities like Tel Aviv and Haifa. These messages highlight ideological motives. The malware also targets Israeli infrastructure, with hardcoded IP ranges and references to key water facilities and desalination plants. It checks for processes and files linked to water treatment systems, confirming a focused intent on disrupting Israel’s water sector.

ZionSiphon starts by checking if it has admin rights. If not, it relaunches itself using PowerShell with elevated privileges. Once active, it installs persistence by copying itself to a hidden path as “svchost.exe” and adding a registry autorun key to blend in with normal system activity.
It then checks if the system matches its target. It verifies the IP against specific ranges and looks for processes, files, and directories linked to water treatment or desalination systems. If the system doesn’t match, it deletes itself and cleans traces.

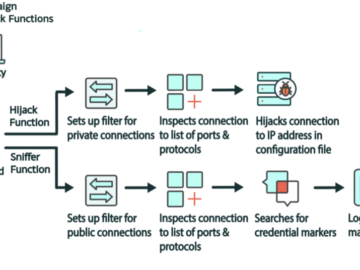
If the target is valid, it modifies local configuration files to increase chlorine levels and pressure. It scans the local network for OT devices using protocols like Modbus, DNP3, and S7, and attempts to interact with them. The Modbus logic is the most developed, allowing it to read and modify registers. Other protocols appear incomplete.
The malware also spreads via USB drives by copying itself as a hidden file and creating fake shortcuts that execute it when opened.
“The malware also includes a removable-media propagation mechanism. The “sdfsdfsfsdfsdfqw()” function scans for drives, selects those identified as removable, and copies the hidden payload to each one as “svchost.exe” if it is not already present. The copied executable is marked with the “Hidden” and “System” attributes to reduce visibility.” continues the report.
Overall, it mixes working capabilities with unfinished parts, suggesting it is still under development.
The researchers note that this version of ZionSiphon contains sabotage and scanning features, but fails in its own targeting logic. The malware compares encoded values to verify if a system belongs to a specific country, but the encryption function produces a different result than expected. Because of this mismatch, the check always fails, even on valid targets, so the malware never activates its payload.
“Although the file contains sabotage, scanning, and propagation functions, the current sample appears unable to satisfy its own target-country checking function even when the reported IP falls within the specified ranges.” continues the report. “This behavior suggests that the version is either intentionally disabled, incorrectly configured, or left in an unfinished state.”
When the target check fails, the malware triggers a self-destruct routine. It removes its persistence from the registry, writes a log message explaining the mismatch, and creates a script that repeatedly tries to delete the malware before removing itself. This suggests the sample is either unfinished, misconfigured, or intentionally disabled.
“Even in its unfinished state, ZionSiphon underscores a growing trend in which threat actors are increasingly experimenting with OT‑oriented malware and applying it to the targeting of critical infrastructure.” concludes the report. “Continued monitoring, rapid anomaly detection, and cross‑visibility between IT and OT environments remain essential for identifying early‑stage threats like this before they evolve into operationally viable attacks.”
Pierluigi Paganini
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, ZionSiphon malware)