Hackers are abusing a trusted Intel utility to quietly launch advanced malware by hijacking the .NET AppDomain mechanism, allowing malicious code to run inside a signed executable and evade many enterprise defenses.
The campaign, dubbed Operation PhantomCLR by researchers, targets financial and other organizations in the Middle East and wider EMEA region using highly targeted spear‑phishing and stealthy in‑memory techniques.
Researchers observed attackers weaponizing IAStorHelp.exe, a legitimately signed Intel storage utility, as the primary launcher for a multi‑stage post‑exploitation framework.
Because the binary is Authenticode‑signed and widely trusted, security tools are more likely to allow its execution, which the threat actors exploit to proxy all malicious activity through a known‑good process.
The core trick is abuse of .NET’s AppDomainManager feature, which controls how application domains are created inside a .NET process.
At CYFIRMA, continuously monitor evolving cyber threats targeting enterprises and critical sectors.By hijacking this mechanism, attackers force their own .NET code to execute before IAStorHelp.exe’s legitimate logic, without modifying the original Intel binary. This effectively turns the utility into a stealthy malware container while preserving its valid digital signature.
AppDomain hijacking via poisoned config
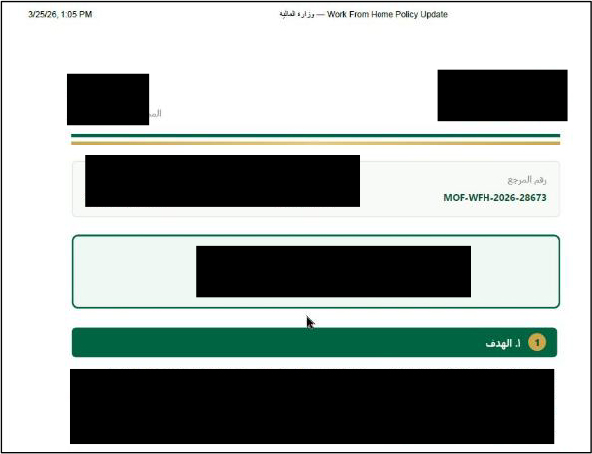
The intrusion typically starts with a spear‑phishing email carrying a ZIP archive that contains the signed IAStorHelp.exe, a malicious IAStorHelp.exe.config file, an obfuscated .NET loader DLL, an encrypted payload, a deceptive “.pdf.lnk” shortcut, and a realistic decoy PDF.
When the victim double‑clicks the shortcut, Windows launches the Intel binary and opens the decoy document, making the activity look like a normal policy or government memo.
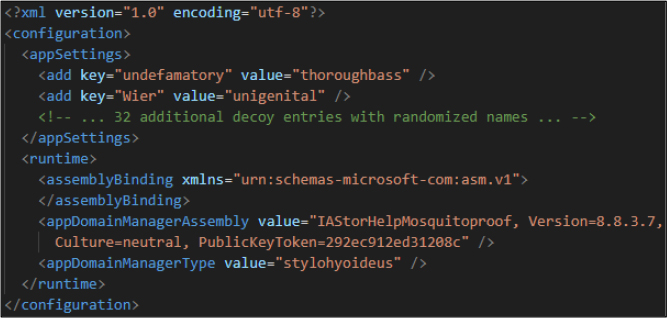
The real compromise happens when the .NET runtime automatically loads IAStorHelp.exe.config from the same folder.
Inside this config, attackers redefine the AppDomainManager to point to their malicious IAStorHelpMosquitoproof.dll and a custom class named “stylohyoideus,” ensuring their code runs first during process initialization.
The document titled “Work From Home Policy Updates” cites Middle Eastern regional security conditions as justification for remote work, demonstrating contextually relevant social engineering.
Because .NET does not enforce code‑signing checks on assemblies loaded via this path, an unsigned, obfuscated DLL silently inherits the trust of the signed Intel host.
Once executed, the framework focuses on staying invisible to sandboxes and endpoint detection tools.
It delays malicious actions using a 60‑second CPU‑intensive prime‑number calculation loop instead of obvious sleeps, then performs an 892,007‑iteration AES key‑derivation cycle to decrypt a large, encrypted payload blob.
These techniques are designed to exhaust automated analysis time windows while appearing as heavy but benign computation.
Rather than using common APIs like VirtualAlloc or WriteProcessMemory, the malware uses a just‑in‑time (JIT) “trampoline” technique: it forces .NET to generate executable code, then overwrites that memory region with shellcode and calls it via a function pointer.
This in‑memory approach reduces traditional telemetry and creates a blind spot for tools that look for classic injection indicators.
The framework further blends in by loading multiple legitimate Windows DLLs, inflating its code with junk classes, and dynamically resolving APIs without standard import tables.
CloudFront‑backed C2 and plugin
On the network side, the malware communicates over HTTPS using Amazon CloudFront as a domain‑fronting layer in front of attacker‑controlled infrastructure hosted on AWS Elastic Load Balancing.
.NET CLR automatically searches for a configuration file matching the pattern
Because traffic appears to go to trusted cloud services, simple IP or domain blocking becomes far less effective. Periodic beacons and tasking travel inside normal TLS, making deep inspection or SSL interception necessary to spot malicious patterns.
Under the hood, the framework operates as a modular plugin platform capable of loading additional capabilities such as data theft, keylogging, or screen capture entirely from memory.
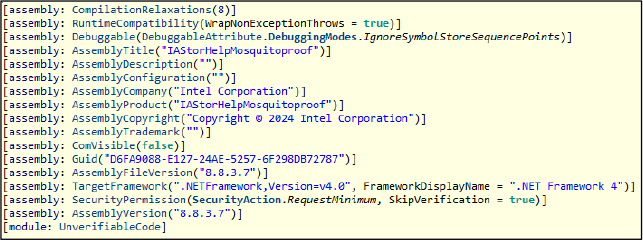
The malware’s assembly metadata is deliberately crafted to appear legitimate, including spoofed attributes such as company name, versioning, and identifiers that mimic trusted software.
It includes resilience features like heap‑walking context recovery and two‑phase memory teardown that wipes payload traces by first blocking access to memory and then freeing it, frustrating forensic efforts.
Defenders should monitor for unusual .exe.config files placed alongside signed binaries, especially where AppDomainManager settings reference unknown or unsigned .NET assemblies.
Security teams are advised to hunt for IAStorHelp.exe executions from user‑writable directories, suspicious .pdf.lnk shortcuts, and Intel processes initiating outbound HTTPS connections to CloudFront or other CDNs.
Vendors and enterprises can harden against similar abuse by tightening application allowlisting, inspecting .NET configuration changes, and adopting behavior‑based detection tuned for JIT abuse, unusual AppDomain activity, and reflective in‑memory loading.
Given the sophistication of this campaign and its focus on trusted execution paths, organizations in financial, government, and critical‑infrastructure sectors should treat any detection associated with IAStorHelp.exe and AppDomain hijacking as a potential full‑domain compromise.
IOCs
| No | IOCs | Type | Remarks |
| 1 | f2266b45d60f5443c5c9304b5f0246348ad82ca4f63c7554c46642311e3f8b83 | SHA-256 | Block |
| 2 | 4f353b9634509a5e1456e54ccb4ce64c1e6d95094df96048ef79b30cc2fda6cb | SHA-256 | Block |
| 3 | 5d784d3ca02ab0015b028f34aa54bc8c50db39f9671dc787bc2a84f0987043b2 | SHA-256 | Block |
| 4 | 8ba1b0392a8fbfb455c43c4e1408352d0e5fc281148810143a5b64938fb0982f | SHA-256 | Monitor |
| 5 | dp8519iqiftub[.]cloudfront[.]net | Domain | Monitor |
| 6 | dunamis-ethos508-prod-va6-856defacfb833db1[.]elb[.]us-east-1[.]amazonaws[.]com | Domain | Monitor |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.