INTERVIEW WITH @MR_HACKER | TOP 20 on INTIGRITI | METHODOLOGY, TIPS & TRICKS, ETC.

Source link
Related Articles
All Mix →On the Vim Path
I just uninstalled TextMate. I also just revamped my git workflow, and am going full-on Vim everywhere. That’s MacVim, Janus, using git within Vim, posting…
Offensive Threat Models Against the Supply Chain
Table of Contents General Motives and Probabilistic Analysis Impact Considerations Supply Chain Threat Library & Motives How to Threat Model Your Supply Chain Threat Modelling…
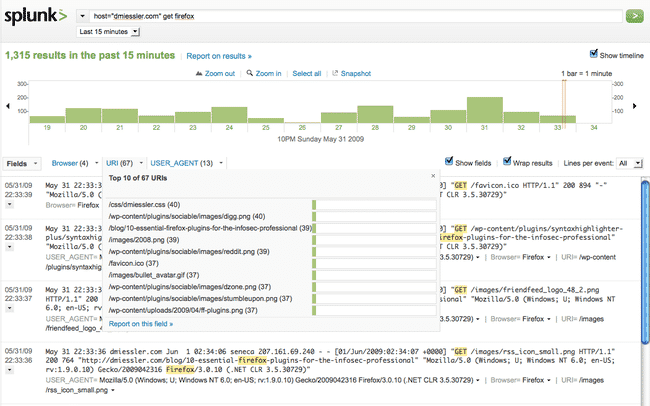
Use Splunk as Your Remote Syslog Server
Table of Contents Syslog Setup netfilter/iptables Apache syslog Links So I’ve been messing with Splunk> a bit recently, and as part of that I’ve been…
[tl;dr sec] #206 – Security Engineer Interview Tips, Security Making Eng Faster, GitHub Action Scanner
Table of Contents 📣 AWS Security Checklist Conferences 📣 Shortcut compliance — without shortchanging security AppSec Web Security Cloud Security Blue Team Red Team Machine Learning +…
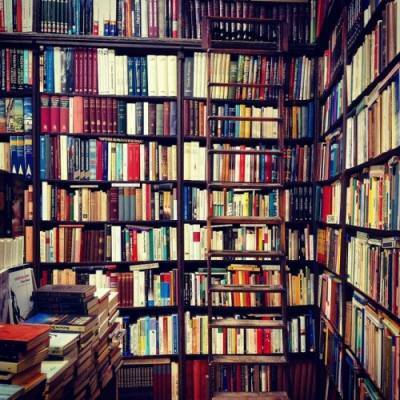
Books and Demons | Daniel Miessler
I have an obsession with reading. Well, actually, as it stands now, it’s more of an obsession with being able to read if I wanted…
New VDP Guidance UK Smart Products [3 Requirements]
Table of Contents Who does the PSTI regulate? What does the PSTI aim to do? What are the PSTI’s security requirements? How does a covered…