The creator of this Invicta malware is heavily active on social networking sites, using them to advertise their information-stealing malware and its deadly powers.
GoDaddy refund emails have become a common tool hackers use to deceive customers into downloading malware.
They decided to launch the payload with a particularly novel approach, or a collection of ones. The payload is a special free open-source Invicta Stealer.
The Invicta Stealer can gather system data, hardware information, wallet data, browser data, and information from applications like Steam and Discord.
Cyble Research and Intelligence Labs (CRIL) discovered this new stealer, termed Invicta Stealer.

“CRIL has noticed a significant increase in the prevalence of the Invicta Stealer due to its builder availability on the GitHub page, leading to numerous TAs actively employing it to infect unsuspecting users,” researchers explain.
Phishing in the GoDaddy Refund Email
According to researchers, the infection starts with a spam email that contains a misleading HTML page intended to fool the recipients into thinking it is an actual refund invoice from GoDaddy.

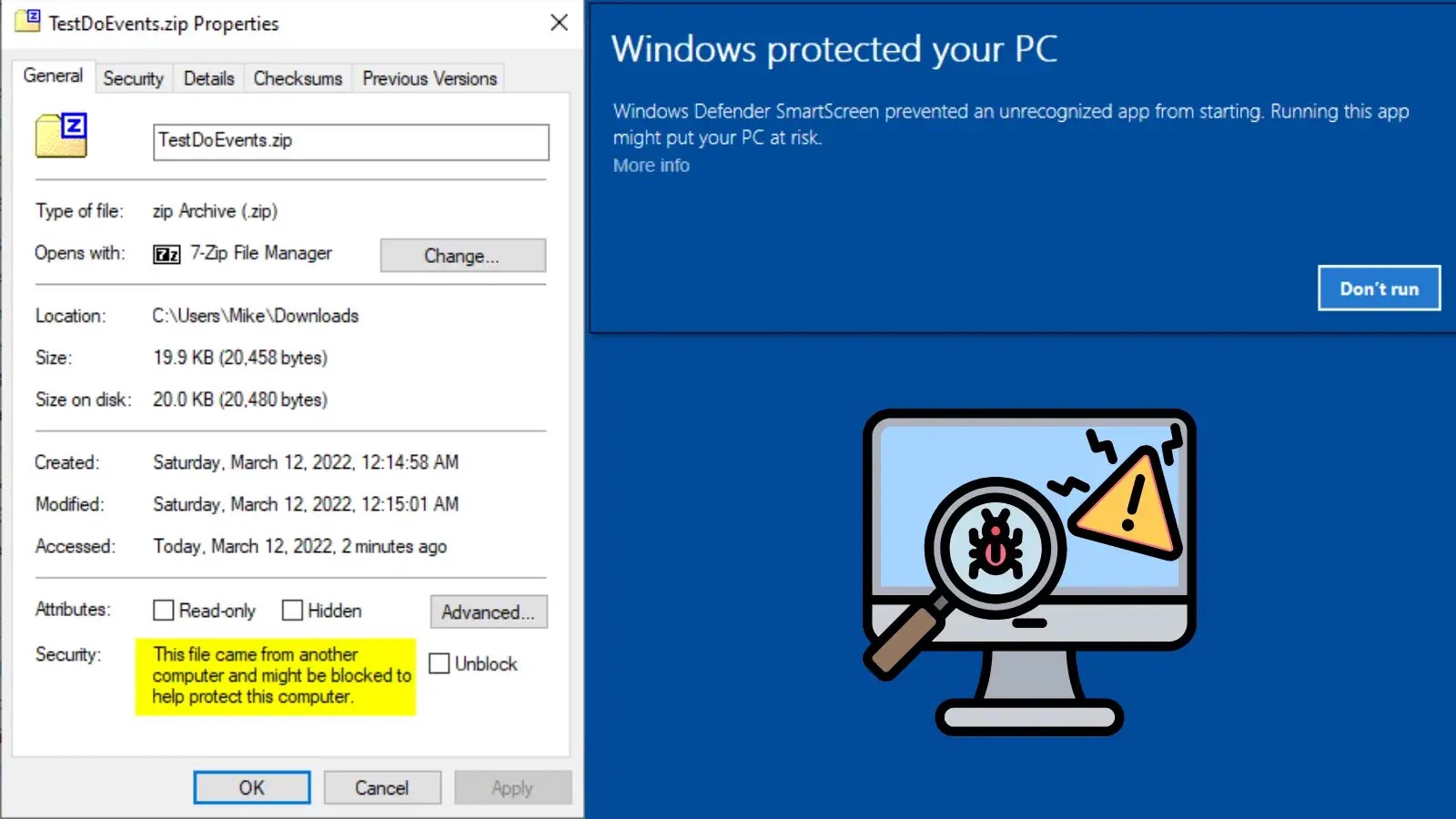
Users that view the phishing HTML page are immediately taken to a Discord URL, where they can download the “Invoice.zip” file. The mechanism by which the HTML page directs users to the Discord URL where they can download “Invoice.zip”.

“Inside the “Invoice.zip” archive file, there is a shortcut file named “INVOICE_MT103.lnk”. When the user opens this .LNK file, it triggers a PowerShell command that runs a .HTA file hosted on the TAs Discord server”, researchers.

This HTA file has VBScript code in it, and that VBScript code then runs a PowerShell script. The PowerShell script downloads an extremely nasty Invicta Stealer.
Following the execution, the stealer gathers a wide variety of system data.
There are specifics like the computer’s name, the system username, the system time zone, the system language, the operating system version, and the names of the processes currently running.
The stealer also uses methods to gather hardware-related data from the computer, such as the amount of main RAM, the number of CPU cores, the screen resolution, the device ID, the IP address, and the geo-IP information.

List of targeted web browsers:

List of targeted cryptocurrency wallets:

Researchers say, “Its objective is to steal crucial information such as active gaming sessions, usernames, and a comprehensive list of games installed by the user on the system.”
It can also target the less popular but still expected KeyPass password manager application.
Final Thoughts
Due to its capacity to target numerous types of extremely sensitive information across different applications and browsers, the Invicta Stealer stands out as a particularly formidable danger.
Attackers can use this stolen information to initiate assaults on other people or companies as well as use it to increase their financial benefit. It is imperative to recognize the seriousness of this threat and take the necessary precautions to safeguard against such nefarious acts.
Shut Down Phishing Attacks with Device Posture Security – Download Free E-Book