Microsoft 365 tenants in the Middle East are facing a new password spray campaign tied to an Iran-linked threat actor.
Rather than starting with malware files or software exploits, the attackers are trying to break in through weak passwords and exposed cloud accounts.
The case shows how a basic identity attack can still open access to email, documents, and admin tools inside a single tenant.
According to the report, the activity came in three waves on March 3, March 13, and March 23, 2026, with the main focus on Israel and the United Arab Emirates.
More than 300 organizations in Israel and over 25 in the UAE were affected, while smaller sets of targets were also seen in Europe, the United States, the United Kingdom, and Saudi Arabia. Government entities, municipalities, energy groups, and private companies were all in scope.
After the second wave drew attention, Check Point researchers identified the operation as an Iran-linked campaign aimed at Microsoft 365 cloud environments.
The company assessed with moderate confidence that the actor originates from Iran, based on the sectors targeted, the regional focus, and the technical behavior seen in login logs.
The researchers also linked the targeting of Israeli municipalities to possible support for kinetic operations and bombing damage assessment during March.
Password spraying differs from a classic brute-force attack because it tries a few common passwords against many accounts instead of repeatedly attacking one user.
In this campaign, the actor used many source IP addresses, which made simple IP-based blocking less useful and made the activity easier to miss as background login noise.
Once valid credentials were found, the attackers could move into mailboxes and other sensitive cloud data without dropping loud malware first.
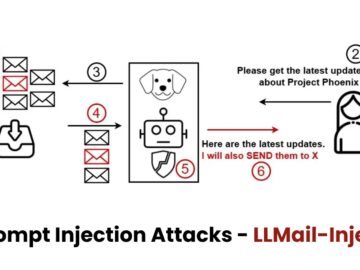
Attack cycle
The attack cycle gives the clearest view of how the operation worked. While the Iran-nexus Password Spraying Volume Over Time March 2026 shows that the login activity rose in distinct bursts, suggesting planned waves instead of random scanning.
.webp)
The attack cycle describes three stages: scan, infiltrate, and exfiltrate. During scanning, the actor used Tor exit nodes that changed often and sent requests with a user agent made to look like Internet Explorer 10 on Windows 7.
.webp)
That rotation reduced the value of single indicators and forced defenders to look at timing, volume, and the spread of failed logins across accounts.
The next step began when the attackers found working credentials. Check Point said the full login process then shifted to commercial VPN ranges tied to Windscribe and NordVPN that were geolocated in Israel, a move that may have helped the actor pass geo-restrictions or reduce alerts tied to foreign access.
“Example Organization – A failed sign-in attempts for accounts in the tenant” captures the type of failed sign-in pattern that can appear before a successful compromise.
.webp)
By entering through valid accounts, the actor could reach personal email content and other sensitive cloud information while avoiding the noise that often comes with malware delivery or destructive actions.
The report says Israeli municipalities appeared to be the main focus, both in the number of organizations targeted and in the volume of password-spraying attempts, but government, energy, and private-sector targets were also hit.
The recommendations are straightforward: watch sign-in logs for many failures across different accounts from one source, apply location-based access controls, block Tor where possible, enforce tenant-wide multi-factor authentication, improve password hygiene, and keep audit logs enabled for post-compromise investigation.
These steps matter because a password spray attack does not need advanced malware to cause harm; one weak password can quietly give an adversary lasting access to a cloud workspace that staff trust every day.
That is why identity monitoring now matters as much as endpoint monitoring for organizations that rely on Microsoft 365 for daily communication, because the simplest attack path can create the biggest opening when many services, users, and records sit behind one password.
Follow us on Google News, LinkedIn, and X to Get More Instant Updates, Set CSN as a Preferred Source in Google.