Is Apple deliberately killing our batteries?

Source link
Related Articles
All Mix →Password Reset Mechanisms: The Online Security Threat Nobody’s Talking About
Table of Contents The Real Threat The Mother of All Backdoors So What Can We Do? Links Humans are notoriously poor at weighing risk. We…
Flattr, and Why It’s Brilliant
Flattr is an exciting new social networking / micro-payment service that allows you to set a donation amount that gets divided among all the different…
Geek Battles: A Call for Perspective
Table of Contents The Classics The Linux Case Humans are funny Hardcore Insecurity Why It’s Not Important Objectivity and Perspective Who commands more respect? “Linux…
Reflected XSS at Philips.com. A full write-up; reflected XSS was… | by Jonathan Bouman
Proof of concept Are you aware of any (private) bug bounty programs? I would love to get an invite. Please get in touch with me:…
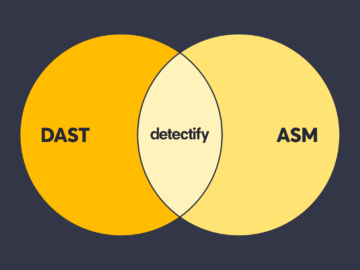
Embracing the best of both DAST and ASM
Table of Contents Differences between manual and automated security testing The history of DAST tools Surface Monitoring + Application Scanning = Best-in-class AST solution Surface…
The Maturity Dilemma | Daniel Miessler
More and more I’ve run into a particular dilemma in life, and I think it’s worth exploring a bit. As I get older, my friends…