The Jenkins project released a critical security advisory addressing seven vulnerabilities across multiple widely used plugins.
The disclosed flaws include high-severity path traversal and stored cross-site scripting (XSS) vulnerabilities that could allow threat actors to execute arbitrary code or hijack user sessions.
All vulnerabilities were responsibly disclosed through the Jenkins Bug Bounty Program, which the European Commission sponsors.
System administrators are strongly advised to update their environments immediately to prevent exploitation in their continuous integration and continuous deployment (CI/CD) pipelines.
The most severe vulnerability addressed in this advisory is a high-severity path traversal flaw tracked as CVE-2026-42520.
This issue impacts the Credentials Binding Plugin up to version 719.v80e905ef14eb_. The plugin previously failed to sanitize file names for file and zip file credentials.
This oversight allows attackers who can provide credentials to a job to write files to arbitrary locations on the node’s filesystem.
If a Jenkins environment is configured to allow a low-privileged user to configure file credentials for a job running on the built-in node, this path traversal can easily escalate to remote code execution (RCE).
The vulnerability is patched in version 720.v3f6decef43ea_ by enforcing proper file name sanitization.
Stored XSS Flaws in GitHub and HTML Publisher Plugins
The advisory also highlights two high-severity stored XSS vulnerabilities impacting popular plugins.
- GitHub Plugin (CVE-2026-42523): Versions 1.46.0 and earlier improperly process the current job URL during JavaScript validation for the “GitHub hook trigger for GITScm polling” feature. Non-anonymous attackers possessing Overall/Read permissions can exploit this flaw to inject malicious scripts. It is resolved in version 1.46.0.1.
- HTML Publisher Plugin (CVE-2026-42524): Versions 427 and earlier fail to safely escape the job name and URL within legacy wrapper files. Attackers with Item/Configure permission can exploit this to launch stored XSS attacks. Version 427.1 corrects this behavior for newly generated wrappers, and environments strictly enforcing Content Security Policy (CSP) protections are inherently mitigated against this flaw.
Medium-Severity Security Issues
Additionally, the update addresses four medium-severity flaws that could facilitate information disclosure or phishing campaigns:
- Script Security Plugin (CVE-2026-42519): A missing permission check in an HTTP endpoint allows attackers with Overall/Read permission to enumerate pending and approved classpaths improperly.
- Matrix Authorization Strategy Plugin (CVE-2026-42521): An unsafe deserialization bug allows attackers with Item/Configure permission to instantiate arbitrary types by invoking parameterless constructors, potentially leading to unauthorized information disclosure.
- GitHub Branch Source Plugin (CVE-2026-42522): A missing permission check enables attackers to perform unauthorized connection tests using attacker-specified GitHub App credentials.
- Microsoft Entra ID Plugin (CVE-2026-42525): An open redirect vulnerability allows attackers to conduct phishing attacks by redirecting users to malicious external sites immediately following successful authentication.
To secure their CI/CD infrastructure, administrators must immediately update all affected components to their patched versions immediately.
| Plugin Name | Vulnerability | Affected Versions | Patched Version |
|---|---|---|---|
| Credentials Binding | Path Traversal | ≤ 719.v80e905ef14eb_ | 720.v3f6decef43ea_ |
| GitHub | Stored XSS | ≤ 1.46.0 | 1.46.0.1 |
| HTML Publisher | Stored XSS | ≤ 427 | 427.1 |
| Script Security | Missing Permission Check | ≤ 1399.ve6a_66547f6e1 | 1402.v94c9ce464861 |
| Matrix Authorization Strategy | Unsafe Deserialization | ≤ 3.2.9 | 3.2.10 |
| GitHub Branch Source | Missing Permission Check | ≤ 1967.vdea_d580c1a_b_a_ | 1967.1969.v205fd594c821 |
| Microsoft Entra ID (Azure AD) | Open Redirect | ≤ 666.v6060de32f87d | 667.v4c5827a_e74a_0 |
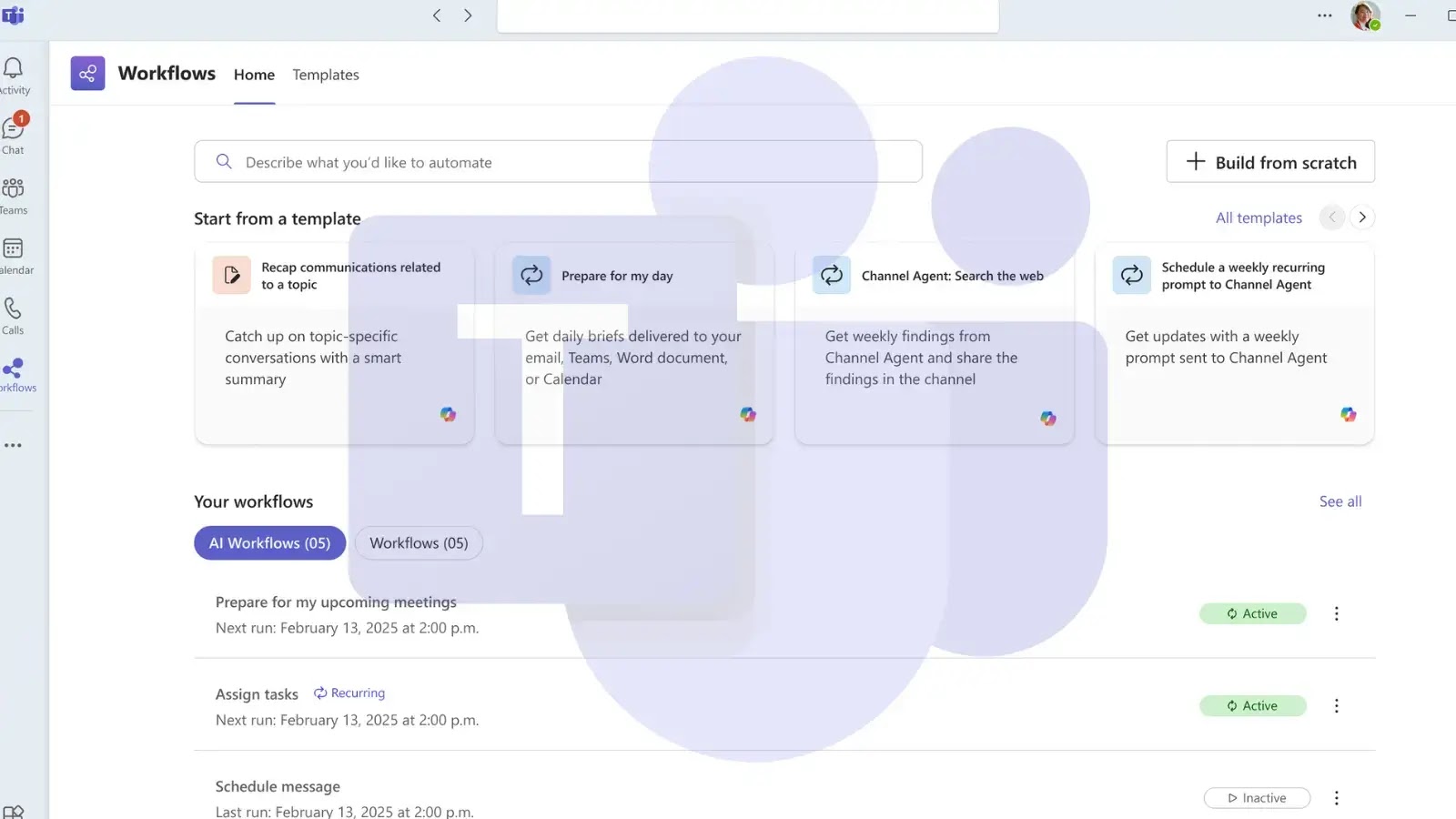
Organizations are advised to prioritize patching the Credentials Binding, GitHub, and HTML Publisher plugins due to their high severity scores and potential for severe system impact. Updates can be directly applied through the Jenkins Update Center interface.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.