Japan’s Computer Emergency Response Center (JPCERT/CC) has shared tips on detecting different ransomware gang’s attacks based on entries in Windows Event Logs, providing timely detection of ongoing attacks before they spread too far into a network.
JPCERT/CC says the technique can be valuable when responding to ransomware attacks, and identifying the attack vector among various possibilities is crucial for timely mitigation.
Finding ransomware traces in Event Logs
The investigation strategy proposed by JPCERT/CC covers four types of Windows Event Logs: Application, Security, System, and Setup logs.
These logs often contain traces left behind by ransomware attacks that could reveal the entry points used by the attackers and their “digital identity.”
Here are some examples of ransomware traces highlighted in the agency’s report:
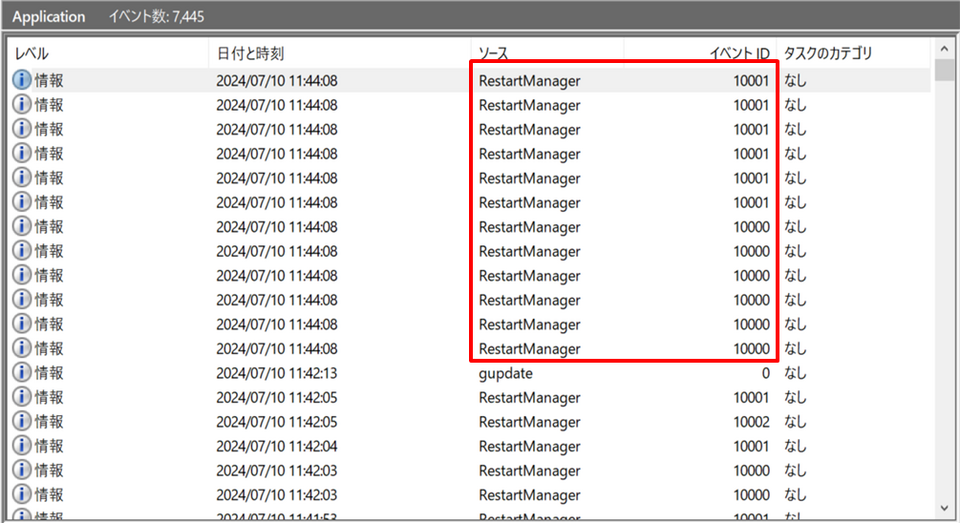
- Conti: Identified by many logs related to the Windows Restart Manager (event IDs: 10000, 10001).

RestartManage notifications from Conti-based encryptors
Source: JPCERT/CCSimilar events are generated by Akira, Lockbit3.0, HelloKitty, Abysslocker, Avaddon, Bablock, and other malware created from Lockbit’s and Conti’s leaked encryptor.
- Phobos: Leaves traces when deleting system backups (event IDs: 612, 524, 753). Similar logs are generated by 8base and Elbie.
- Midas: Changes network settings to spread infection, leaving event ID 7040 in logs.
- BadRabbit: Records event ID 7045 when installing an encryption component.
- Bisamware: Logs a Windows Installer transaction’s start (1040) and end (1042).
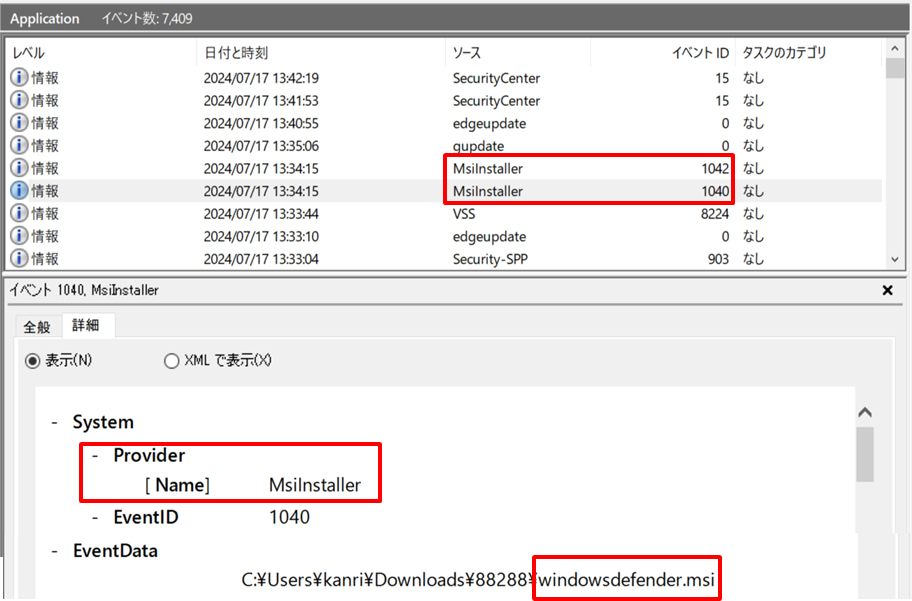
Source: JPCERT/CC
JPCERT/CC also notes that seemingly unrelated ransomware variants such as Shade, GandCrab, AKO, AvosLocker, BLACKBASTA, and Vice Society, leave behind very similar traces (event IDs: 13, 10016).
Both errors are caused by a lack of permissions when accessing COM applications to delete Volume Shadow Copies, which ransomware typically deletes to prevent easy restoration of encrypted files.
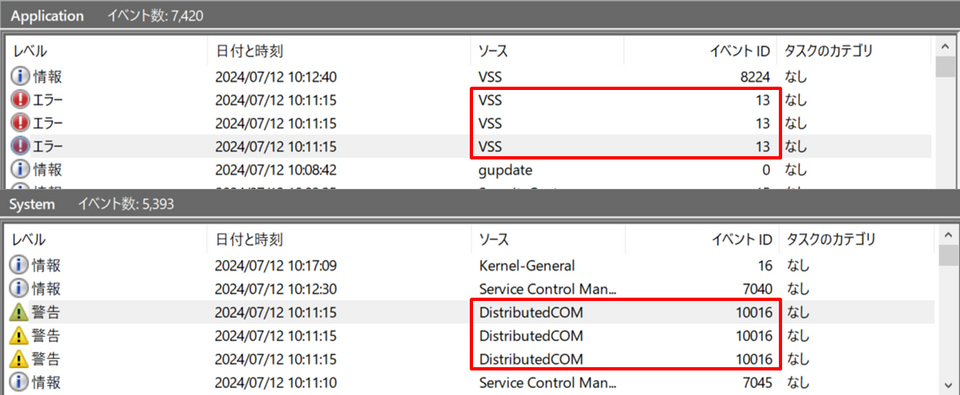
Source: JPCERT/CC
It’s important to note that no detection method should be taken as a guarantee for adequate protection against ransomware, but monitoring for specific logs can prove game-changing when combined with other measures to detect attacks before they spread too far into a network.
JPCERT/CC notes that older ransomware strains such as WannaCry and Petya did not leave traces in Windows logs, but the situation has changed on modern malware, so the technique is now considered effective.
In 2022, SANS also shared a guide on detecting different ransomware families using Windows Event Logs.