A newly identified malware loader dubbed “Kiss Loader” is emerging as a potential threat, leveraging advanced process injection techniques and dynamic delivery infrastructure.
The loader, still under active development at the time of discovery, demonstrates a blend of stealth, modular staging, and experimental implementation, suggesting it may evolve into a more mature attack tool.
When executed, the file connects to a remote WebDAV resource hosted via a TryCloudflare tunnel. This service allows attackers to expose local servers without dedicated infrastructure, enabling flexible and frequently updated payload delivery.
Analysis of the sample reveals a structured, multi-stage execution flow. The infection begins with a Windows Internet Shortcut file disguised as a PDF document.
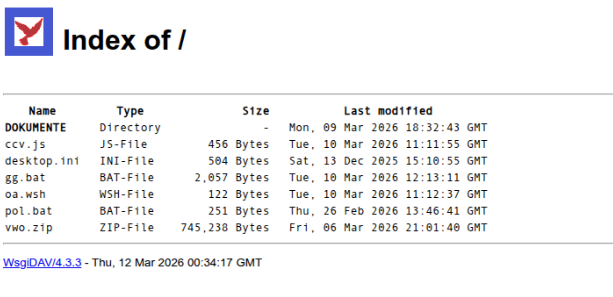
Within the exposed WebDAV directory, a secondary shortcut file triggers further execution. This leads to a Windows Script Host (WSH) process, which chains into a JScript component.
This layered execution approach helps obscure the later stages of the attack and reduces immediate detection.
Kiss Loader Malware
The JScript stage retrieves a batch script responsible for orchestrating the next phase. This script performs multiple functions, including displaying a decoy PDF to the victim, establishing persistence through the Windows Startup folder, and downloading additional payload components.
The exposed WebDAV directory lacked access restrictions, which allowed me to directly enumerate and retrieve its contents.
Among these components is a Python-based loader identified as “Kiss Loader.” The loader uses JSON configuration files to retrieve decryption keys, ensuring that payloads remain encrypted until runtime. This design complicates static analysis and enhances evasion.
The decrypted payloads include a variant resembling VenomRAT or AsyncRAT, along with a .NET Reactor–protected utility.
The shellcode used in execution is generated via Donut, a tool designed for in-memory execution of .NET assemblies.
The final stage of execution relies on Early Bird APC injection, a stealthy process injection technique. The loader creates a legitimate process, such as explorer.exe, in a suspended state. It then allocates executable memory within the process and writes the decrypted shellcode.
Instead of spawning a new thread, the malware queues an Asynchronous Procedure Call (APC) to the primary thread.
When the thread resumes, the queued APC executes before normal process initialization, allowing the malicious code to run under a trusted process context. This significantly improves stealth and bypasses conventional detection mechanisms.
Signs of Active Development
Several indicators suggest that Kiss Loader is still in a development phase. The WebDAV repository used for payload delivery was publicly accessible and lacked authentication controls, allowing direct enumeration of hosted files.
Observations show that the files were recently deployed, indicating an ongoing campaign setup.
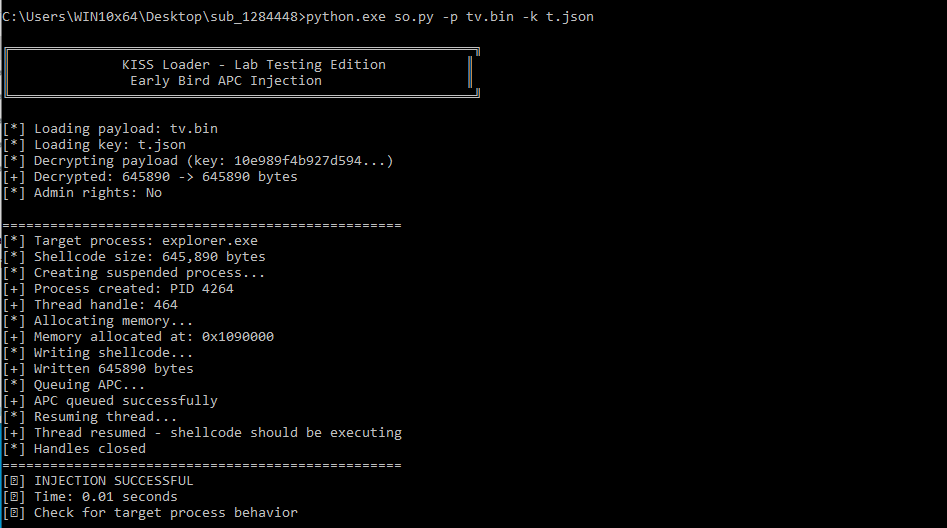
Additionally, the loader’s code contains extensive inline comments explaining core routines such as decryption and injection.
The presence of testing utilities, helper functions, and verbose runtime output further supports the conclusion that the malware is being actively tested and refined.
During controlled analysis, an unexpected event occurred: the system appeared to be actively accessed by an external operator. Tools were abruptly terminated, and cursor movement was observed without user input.
In a controlled experiment, a message left in a Notepad window received a response, confirming live interaction with the threat actor.
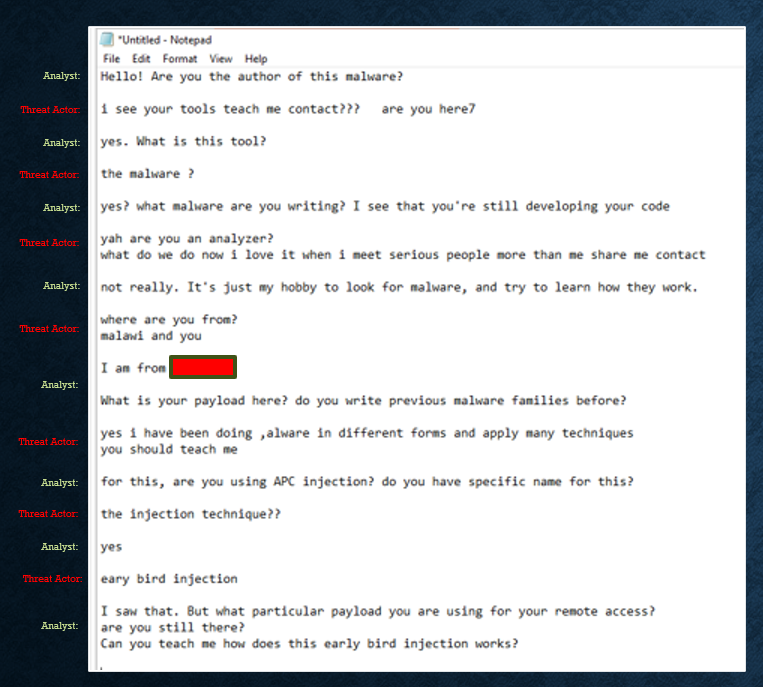
The individual acknowledged developing the malware and confirmed the use of Early Bird injection. The interaction, though brief, provided rare real-time insight into the development process and attacker intent.
Kiss Loader highlights the increasing sophistication of loader-based malware and the growing use of flexible infrastructure like Cloudflare.
Its use of layered execution, encrypted payload staging, and advanced injection techniques underscores its potential as a future threat.
The case also serves as a reminder that malware analysis can occasionally extend beyond code, revealing the human element behind cyber threats.
As attackers continue to experiment and adapt, maintaining strict isolation and controlled environments remains critical for safe and effective analysis.
IOCs
| 6abd118a0e6f5d67bfe1a79dacc1fd198059d8d66381563678f4e27ecb413fa7 | DKM_DE000922.pdf.url |
| e8f83d67a6b894399fad774ac196c71683de9ddca3cf0441bb95318f5136b553 | oa.wsh |
| 549c1f1998f22e06dde086f70f031dbf5a3481bd3c5370d7605006b6a20b5b0b | ccv.js |
| 6d62b39805529aefe0ac0270a0b805de6686d169348a90866bf47a07acde2284 | gg.bat |
| b4525711eafbd70288a9869825e5bb3045af072b5821cf8fbc89245aba57270a | pol.bat |
| e8dbdab0afac4decce1e4f8e74cc1c1649807f791c29df20ff72701a9086c2a0 | vwo.zip |
| 5cab6bf65f7836371d5c27fbfc20fe10c0c4a11784990ed1a3d2585fa5431ba6 | so.py |
| 20a585c4d153f5f551aaa509c8c1fa289fa6f964fe53f241ef9431a9390b3175 | tv.bin |
| 6a7c3029cd4f7ffe9a24ea5d696e1f612ada91b5a5ca5b28d4972d9c772051fd | t.json |
| 665f44b5a46947ad4fdac34a2dca4cf52b3e7e21cfa3bd0fc3ef10bd901ad651 | ov.bin |
| b3737f621eb2ee6d784a6b9d695b890a5f22ee69e96058c99d9048b479451fbd | a.json |
| 130ca411a3ef6c37dbd0b1746667b1386c3ac3be089c8177bc8bee5896ad2a02 | decrypted ov.bin (VenomRAT) |
| 2b40a8a79b6cf90160450caaad12f9c178707bead32bcc187deb02f71c25c354 | decrypted tv.bin (Kryptik) |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.