44% of unfolding ransomware attacks were spotted during lateral movement, according to Barracuda Networks.
25% of incidents were detected when the attackers started writing or editing files, and 14% were unmasked by behavior that didn’t fit with known activity patterns.
Barracuda researchers analyzed a sample of 200 reported incidents covering August 2023 to July 2024, involving 37 countries and 36 different ransomware groups.
RaaS models most common in recent ransomware attacks
The sample shows that 21% of incidents hit healthcare organizations, up from 18% a year ago, while 15% of reported attacks were against manufacturing and 13% targeted technology companies. Incidents involving education halved from last year’s 18% to account for 9% in 2023/24.
The most prevalent ransomware groups were ransomware-as-a-service (RaaS) models. These include LockBit, which was behind one in six in the last 12 months, or 18% of attacks where the attacker’s identity is known.
ALPHV/BlackCat ransomware accounted for 14% of attacks, while Rhysida, a relatively new ransomware group, accounted for 8% of named attacks.
“Ransomware-for-rent attacks can be hard to detect and contain. Different cybercriminal customers can use different tools and tactics to deploy the same payload, resulting in considerable variation,” said Adam Khan, VP, Global Security Operations at Barracuda Networks.
“Fortunately, there are tried and tested approaches that most attackers rely on, such as scanning, lateral movement, and malware download. These can trigger security alerts that provide security teams with several opportunities to detect, contain, and mitigate ransomware incidents before they have a chance to fully unfold. This is particularly important in IT environments where not all machines are completely secured,” added Khan.
Leading indicators of ransomware activity
According to detection data from Barracuda, in the first six months of 2024 the top indicators of likely ransomware activity include:
- Lateral movement: 44% of the ransomware attacks were spotted by detection systems monitoring for lateral movement.
- File modifications: 25% were detected by the system that notes when files are being written or modified and analyses them to see if they match any known ransomware signatures or suspicious patterns.
- Off-pattern behavior: 14% were caught by the detection system that identifies abnormal behavior within a system or network. This system learns the typical behavior of users, processes, and applications. When it detects deviations (such as unusual file access, tampering with operating system components, or suspicious network activity), it triggers an alert.
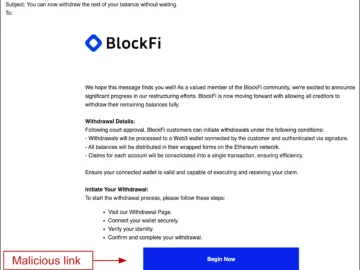
The detailed investigation of a mitigated PLAY ransomware attack targeting a health technology business and an 8base incident hitting a car care company found that attackers try to establish footholds on unprotected devices to launch the next phase of their attack and hide malicious files in rarely used music and video folders.
Multiple detection layers are essential in the battle against active threats such as ransomware, where attackers often leverage commercially available tools used legitimately by IT teams and can make real-time adjustments in their behavior and tactics to succeed.