A new cybercriminal service called “Leak Bazaar” has surfaced on the Russian-speaking TierOne forum, advertised on March 25, 2026, by a user known as Snow of SnowTeam.
Unlike traditional data leak sites, Leak Bazaar introduces a more structured approach to monetizing stolen corporate data, focusing on processing and refining information rather than simply publishing it.
In many ransomware and data theft cases, attackers exfiltrate massive volumes of corporate data. When victims refuse to pay, this data is often dumped publicly.
However, raw datasets are typically messy and difficult to use. They contain duplicate files, system noise, outdated records, and complex database exports that require significant effort to interpret.
According to the report, Leak Bazaar directly targets this inefficiency. Instead of treating stolen data as immediately valuable, the platform emphasizes transforming disorganized datasets into structured, usable information.
This reflects a growing realization in cybercrime operations: the challenge is no longer just stealing data, but making it actionable and profitable.
A Processing Layer for Cybercrime
Leak Bazaar positions itself as a post-exfiltration service rather than a traditional leak site. According to the advertisement, the platform uses a dedicated infrastructure designed for “deep analytics,” including:
- Automated filtering to remove irrelevant system files.
- Machine learning-assisted text analysis.
- Database parsing and reverse engineering (e.g., SQL, SAP, Oracle).
- Human analyst validation for accuracy.
This combination of automation and manual review is key. While machine processing speeds up data refinement, human analysts ensure the final output is reliable and meaningful.
The end goal is to convert raw stolen data into clean formats such as spreadsheets or categorized datasets that buyers can easily consume.
For example, a complex financial database dump that would normally require technical expertise could be transformed into a readable financial report, making it valuable to a wider range of buyers.
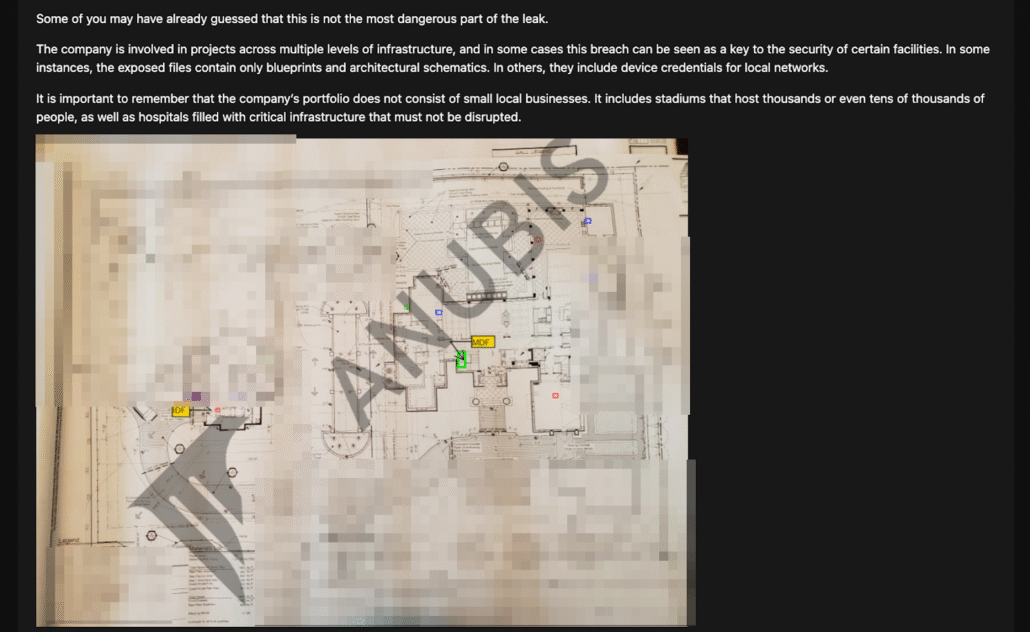
Groups like Anubis, for example, write extensive “investigative journalistic pieces” on their victims after sorting through the datasets.
Another notable feature is how Leak Bazaar categorizes processed data. Instead of preserving the victim’s original file structure, the platform reorganizes information into market-driven categories such as:
- Financial reports.
- Mergers and acquisitions (M&A) data.
- Research and development (R&D) materials.
- Personal and customer data.
This reflects a clear shift toward market segmentation. Each category is tailored to a specific buyer profile, such as traders seeking financial insights or competitors looking for proprietary research. By aligning stolen data with demand, the platform increases its resale value.
Leak Bazaar also introduces a more advanced monetization model. It offers a 70/30 revenue split, with 70 percent going to the data supplier and 30 percent to the platform. More importantly, it supports two sales formats:
- Exclusive sale: Data is sold ერთხელ and removed permanently.
- Multi-buyer sale: Data is sold multiple times at a lower price.
This model allows threat actors to generate ongoing revenue from a single breach, rather than relying solely on ransom payments. In effect, stolen data becomes a reusable asset rather than a one-time leverage tool.
Expanding the Extortion Ecosystem
The platform also attempts to address trust and operational challenges. Transactions are reportedly handled through a guarantor service, and Leak Bazaar offers support in negotiations with victims.
This suggests the service aims to integrate into multiple stages of cybercrime operations, from post-breach analysis to resale and even ransom discussions.
Additionally, Leak Bazaar enforces quality thresholds for submitted data, including minimum size requirements (100 GB to 1 TB), preference for English-language content, and targeting companies with over $10 million in revenue.
Leak Bazaar represents an evolution in the cybercriminal economy. Rather than acting as a simple repository for leaked files, it introduces a structured marketplace built around data processing, segmentation, and resale.
The platform highlights a broader trend: cybercriminals are increasingly treating stolen data as a product that requires refinement, packaging, and strategic distribution.
While it remains unclear how effective Leak Bazaar will be in practice, its model signals a shift toward more professionalized and scalable monetization strategies in the underground ecosystem.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.