LeakNet is scaling its ransomware operation by pairing mass-market ClickFix lures with a stealthy Deno-based loader that executes almost entirely in memory, shrinking the window for defenders to intervene.
Ransomware operator LeakNet is currently averaging around three victims per month. However, recent activity shows the group investing in its own delivery and execution infrastructure to grow that number.
Instead of relying primarily on initial access brokers for ready-made footholds, LeakNet now runs its own campaigns using ClickFix lures hosted on compromised legitimate websites and follows up with a Deno-based loader that behaves like a legitimate developer tool while running malicious code in memory.
In investigations tied to LeakNet, analysts observed two consistent innovations: first, ClickFix prompts that trick users into manually executing an msiexec command; second, a bring-your-own-runtime (BYOR) pattern where a legitimate Deno binary decodes and runs a base64-encoded payload without dropping a traditional malware file on disk.
Both paths feed into the same post-exploitation playbook, giving defenders a predictable sequence of behaviors to hunt for even when the initial infection vector changes.
ClickFix: A New Front Door for LeakNet
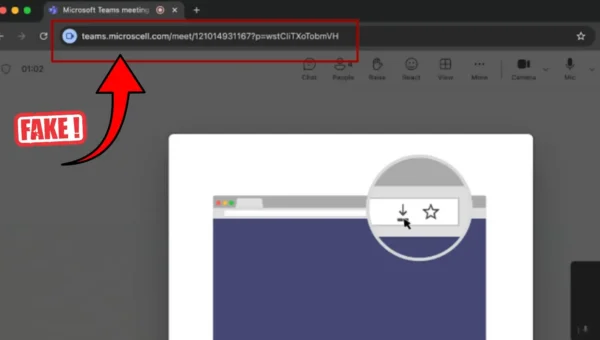
ClickFix is a social engineering technique that abuses fake error messages and verification pages to convince users to copy and run attacker-supplied commands, often via Windows Run (Win+R) or similar entry points.
LeakNet delivers these lures through compromised, otherwise legitimate websites for example, a fake Cloudflare Turnstile verification page that instructs the user to execute an msiexec command pointing to attacker-controlled infrastructure, which then downloads and runs the group’s loader.
Because the lure rides on trusted sites and does not depend on obviously malicious domains or targeted spear-phishing, any employee casually browsing the web can become an entry point with no clear target profile or early warning signal for defenders.
This shift away from exclusive dependence on IAB-sourced credentials lowers LeakNet’s per-victim acquisition cost, removes the bottleneck of waiting for access to be sold, and widens the potential victim pool beyond the lists curated by other threat actors.
Once a victim runs the initial command, LeakNet often pivots into a Deno-based loader that executes base64-encoded JavaScript or TypeScript directly in memory via a data: URL, leaving minimal artifacts on disk.
In observed incidents, the loader chain was kicked off by VBS and PowerShell scripts with decoy names such as Romeo*.ps1 and Juliet*.vbs, reinforcing the appearance of legitimate scripting or troubleshooting activity.
The Deno process collects basic host details like username, hostname, memory, and OS version, hashes them into a unique victim identifier, checks in with attacker-controlled infrastructure to choose a C2 endpoint, and then enters a polling loop that repeatedly fetches and executes additional code.
Because Deno is a signed, widely used runtime, it can bypass simple allowlists, meaning the suspicious element is not the binary itself but its context: unusual command-line arguments, execution outside development environments, unexpected parent processes, and persistent outbound C2 traffic.
Inside LeakNet’s Post-Exploitation Playbook
Despite evolving initial access, LeakNet’s post-compromise behavior is highly consistent, which creates detection opportunities across incidents.
The group begins with DLL sideloading by placing a trojanized jli.dll alongside a legitimate Java binary under C:ProgramDataUSOShared, making the malicious library appear as part of normal Java and Windows Update-related activity.
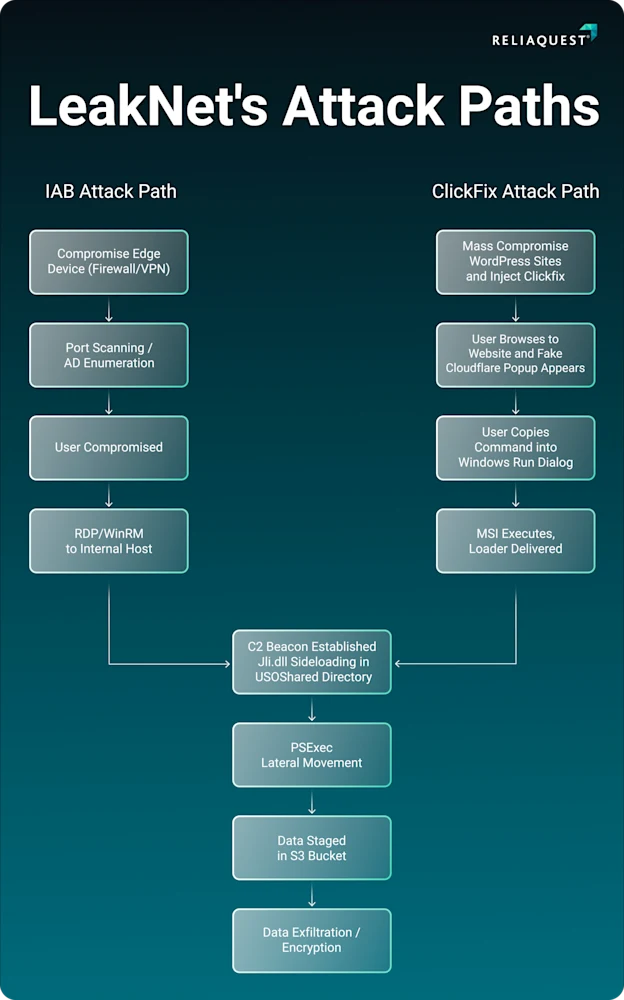
After establishing execution, LeakNet shifts to command-and-control using a repeatable URL pattern for beaconing, then pivots to lateral movement with PsExec after first running “cmd.exe /c klist” to enumerate active Kerberos tickets and identify reachable accounts.
For staging and exfiltration, the operators use S3 bucket infrastructure that blends into ordinary cloud traffic, further masking malicious transfers behind services defenders expect to see in enterprise environments.
Because LeakNet leans on trusted binaries, cloud services, and compromised websites, defenders need to move beyond signature-only detection and focus on behavioral signals across the chain.
High-value detections include: msiexec commands spawned from browsers or Win-R dialogs, Deno executing base64 data URLs or running outside known developer machines, java.exe loading jli.dll from C:ProgramDataUSOShared, anomalous PsExec usage from non-admin accounts, and unexpected outbound connections to S3 buckets tied to staging or C2.
Organizations can further reduce risk by enforcing policies that block newly registered domains where feasible, preventing regular users from invoking Win-R or PsExec, and pairing these controls with automated response playbooks.
IOCs
| Artifact | Details | Artifact | Details |
|---|---|---|---|
| tools.usersway[.]net | Clickfix Domain on Compromised Websites | okobojirent[.]com | Deno C2 Domain |
| apiclofront[.]com | Clickfix Domain | mshealthmetrics[.]com | Deno C2 Domain |
| sendtokenscf[.]com | Clickfix Domain | verify-safeguard[.]top | Deno C2 Domain |
| binclloudapp[.]com | Clickfix Domain | 194.31.223[.]42 | Deno C2 IP Address |
| neremedysoft[.]com | Sideloaded jli.dll C2 Domain | 144.31.2[.]161 | Deno C2 IP Address |
| ndibstersoft[.]com | Sideloaded jli.dll C2 Domain | 87.121.79[.]6 | Deno C2 IP Address |
| windowallclean[.]com | Sideloaded jli.dll C2 Domain | 87.121.79[.]25 | Deno C2 IP Address |
| cnoocim[.]com | Deno C2 Domain | 144.31.54[.]243 | Deno C2 IP Address |
| delhedghogeggs[.]com | Deno C2 Domain | 144.31.224[.]98 | Deno C2 IP Address |
| serialmenot[.]com | Deno C2 Domain | fastdlvrss.s3.us-east-1.amazonaws[.]com | Malicious S3 Bucket |
| crahdhduf[.]com | Deno C2 Domain | backupdailyawss.s3.us-east-1.amazonaws[.]com | Malicious S3 Bucket |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.