Learn to Hack Web Apps – Live | #APIs #BOLA #brokenAuth

Source link
Related Articles
All Mix →Nmap: Use the –top-ports Option for Both TCP and UDP Simultaneously
I’m a big fan of nmap‘s –top-ports option, which gives you the ability to leverage Fyodor’s latest Internet research on open ports on the Internet.…
One Month of Learnings from Flo Health’s Bug Bounty Program: A Q&A with CISO, Leo Cunningham
The CISO of Flo Health, the world’s most popular women’s health app, knows that enabling his security team with the most advanced security testing methods…
[Alert] New WordPress XSS Vulnerability Discovered
Are you running WordPress 4.2.0 to 4.5.1? Time to upgrade to 4.5.2! It was recently discovered that WordPress versions 4.2.0 to 4.5.1 are vulnerable against a reflected…
TTL Caging: How to Fight Malware Using Reduced TTL Values
My buddy and co-worker Steve Crapo (pronounced CRAY-poe) recently told me about an idea he had a while back about how to keep malware on…
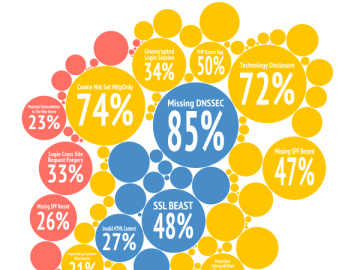
First encounters through the eyes of the Detectify scanner
What do typical websites look like through the eyes of our vulnerability scanner the first time they are tested? How does that picture change over time?…
Optimizing ZAP and Burp with JVM
Table of Contents JVM Options JVM Options in ZAP JVM Options in BurpSuite Optimizing with JVM Memory Garbage Collector AggressiveOpts Deduplication Strings Conclusion 누군가가 저에게…