Learn WebApp Pentesting: 2023 edition

Source link
Related Articles
All Mix →6 months after the launch of Detectify Crowdsource: What has happened so far?
Table of Contents What is Crowdsource? What have we found? Who has joined Crowdsource? The future of Crowdsource? Utilize our hacker community to test your…
Hacking Salesforce Lightning: A Guide for Bug Hunters
Salesforce Experience (or Community) Cloud is a CRM platform that helps software companies and organizations manage their customer relationships. Software companies and organizations often use…
Bi-directional JIRA integration at HackerOne
Table of Contents Why bi-directional integration is so powerful How it works It will function perfectly behind your Firewall So what’s next How to get…
Who’s building it? · Joseph Thacker
Andrej Karpathy recently tweeted this: “Input optional product Don’t ask your users for input. Coming up with input is hard, and a barrier to use.…
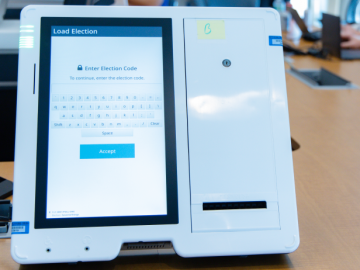
Boosting Election Integrity With Coordinated Vulnerability Disclosure [4 Insights]
Table of Contents 1. This year, The first collaborative engagement dedicated to establishing trust and demonstrating progress through coordinated vulnerability disclosure occurred at the Election…
From Password Reset Mechanisms to OpenID: A Brief Discussion of Online Password Security
Table of Contents The ‘Eggs and Baskets’ Counterargument Tradeoffs The Weakest Link: Email Password Reset Mechanisms A Risk Discussion Phishing So What Do We Do?…