Learning SECURE CODE REVIEW!

Source link
Related Articles
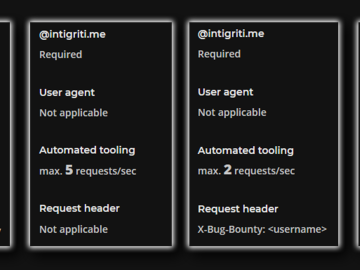
All Mix →Aggressive scanning in bug bounty (and how to avoid it)
Table of Contents What is aggressive scanning? Why should you avoid it? How can you avoid it? Configuring Common Tools ffuf gobuster sqlmap burp Conclusion…
Severe Confluence Vulnerability is an Active Threat (CVE-2022-26134)
Background The vulnerability allows unauthenticated remote code execution (RCE). Exploitation occurs by sending an HTTP request with an attack payload to a vulnerable instance of…
Redirecting a Domain Using .htaccess
Here’s how to redirect from one domain to another within Apache using .htacess. This is how to do it permanently (using an HTTP 301 redirect)…
The Desync Delusion: Are You Really Protected Against HTTP Request Smuggling?
Table of Contents The Hidden Threat That's Slipping Past Your Security Why Other DAST Tools Fall Short Burp Suite DAST: Request Smuggling Detection Reinvented, for…
Proposed Legislation Requires Federal Contractors Implement VDPs
Federal contractors play a critical role in supporting the U.S. government. Because of their access to federal systems and data, they have the potential to…
Understanding DevSecOps | HAHWUL
Table of Contents What is DevSecOps? Why DevSecOps? How to measure maturity? Resources Conclusion Sharing thoughts and approaches on DevSecOps, which integrates development (Dev), security…