Learning to Hack in 2021: What resources should you use?

Source link
Related Articles
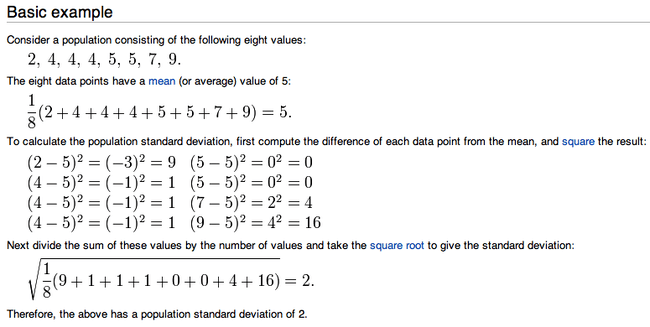
All Mix →Standard Deviations Explained | Daniel Miessler
If you read a lot but aren’t much into math you’ve probably heard the term standard deviation being tossed around, but didn’t know what it…
NIST CSF 2.0, API Security, and CISO Imperatives
Table of Contents The Basics Who’s Using It? The Discussion API Security Last week, our good friend Raj Umadas, Director of Security at ActBlue, teamed…
Node.js and NPM Ecosystem: What are the Security Stakes?
Vladimir de Turckheim, Software Engineer, Sqreen twitter, linkedinabstract slides video For vulnerabilities, a SQL injection example is given as well as regular expression denial of service, the…
5 Things Top Bug Bounty Hunters Do Differently
Table of Contents They Know How to Build They Have An Eye For Anomalies They Submit Quality Reports They Set Goals They Hack together This…
From Password Reset Mechanisms to OpenID: A Brief Discussion of Online Password Security
Table of Contents The ‘Eggs and Baskets’ Counterargument Tradeoffs The Weakest Link: Email Password Reset Mechanisms A Risk Discussion Many Weak Passwords vs. Single Point…
Bug Bounty Vs. Pentest [Differences Explained]unty vs. Penetration Testing: What’s the Difference?
Table of Contents What Is Pentesting? Different Pentesting Methods Which Pentesting Option Is Right for Your Organization? What About a Bug Bounty Program? What Is…