Identified through data captured by our SSH honeypots over two months, this campaign represents a sophisticated blend of eras. It merges “old-school” Internet Relay Chat (IRC) botnet tactics from the late 2000s with modern, automated mass-compromise techniques.
While the infrastructure resembles known threats, SSHStalker is a distinct operation focused on resilience and scale rather than stealth.
What makes SSHStalker unique is its “living off the land” approach to deployment. Rather than simply dropping a pre-made virus, the attacker creates an automated pipeline on the victim’s machine:
- The Entry: The attack begins with a Golang-based binary (disguised as nmap) that scans for servers with open SSH ports (Port 22).
- The Build: Once access is gained, the malware downloads the GCC compiler. It then drops raw C source code files onto the victim’s server and compiles the malware on the spot.
- The Connection: The newly compiled bots immediately connect to an IRC server. This allows the attackers to control thousands of infected machines using chat channels a legacy method that remains highly effective for redundancy.
Flare’s research team has uncovered a undocumented Linux botnet operation dubbed SSHStalker.
Persistence: The 60-Second Watchdog
SSHStalker is designed to be incredibly noisy but difficult to remove. The threat actors prioritize keeping the bot alive over staying hidden.
The botnet maintained persistent access without executing any observable impact operations, despite having in its arsenal capabilities to launch DDoS attacks and conduct cryptomining.
The kit installs a Cron job (a scheduled task) that runs every single minute. This script acts as a “watchdog.”
It checks if the malware process is running; if a defender or antivirus kills the bot, the watchdog script automatically recompiles and relaunches it within 60 seconds.
This aggressive persistence mechanism ensures the botnet remains stable even if individual processes are terminated.
The research revealed a massive library of exploits targeting Linux Kernel versions 2.6.x vulnerabilities dating back to 2009 and 2010.
While these exploits are ineffective against modern, updated Linux servers, they are devastatingly effective against “long-tail” legacy environments.
This includes forgotten cloud instances, old IoT devices, and unmaintained virtual private servers (VPS).
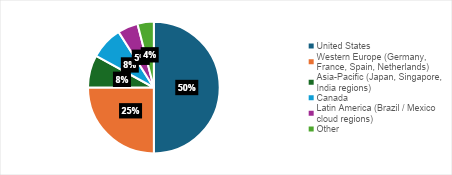
Flare found evidence of nearly 7,000 compromised IPs, heavily concentrated in cloud hosting environments like Oracle Cloud.
The scan results are heavily dominated by cloud hosting providers, with strong indicators of Oracle Cloud infrastructure, which operates large ASN blocks such as AS31898 and related Oracle network ranges.
The attackers appear to be building a massive network of these legacy systems to mine cryptocurrency (specifically Ethereum Classic) and harvest AWS credentials.
The Romanian Connection
The operational fingerprint of SSHStalker strongly resembles the Outlaw (or Maxlas) botnet group.
The file structures, use of IRC, and specific persistence methods are similar. Furthermore, the kit is full of Romanian-language artifacts, slang, and nicknames.
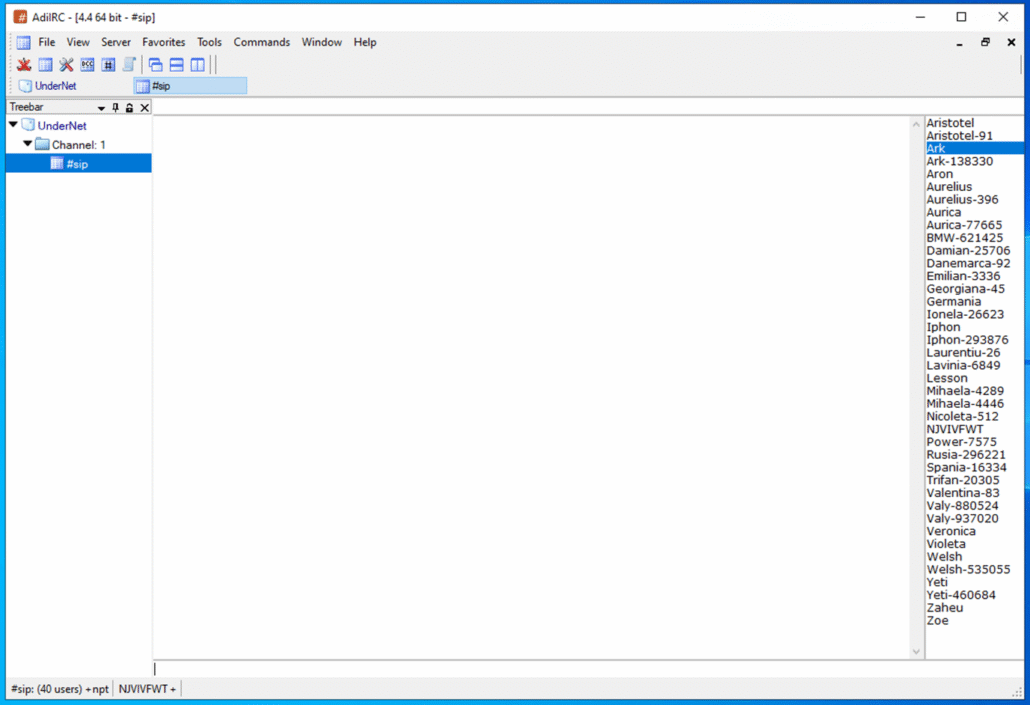
However, no direct identifiers linking it to Outlaw were found. This suggests SSHStalker is likely a “copycat” or a derivative group operating in the same ecosystem, utilizing similar toolkits to achieve different ends.
The most distinct red flag for this campaign is the activity of compilers on production servers. Defenders should monitor for the execution of gcc, make, or build tools in directories like /tmp or /dev/shm.
Additionally, blocking outbound IRC traffic and monitoring for Cron jobs that execute every minute can help detect an infection before it becomes a persistent foothold.
Indicators of Compromise
| # | Type | Value | MD5 Hash | Comments / Detection |
|---|---|---|---|---|
| 1 | ELF file | h32 | 0d01bd11d1d3e7676613aacb109de55f | Prochider rootkit |
| 2 | ELF file | h64 | 1e288bb6920d9cf07d0e5dbc8614469d | Prochider rootkit |
| 3 | ELF file | run32 | 32ee52b2918e06e3925eaccb0bea2d66 | IRCbot |
| 4 | ELF file | run64 | 88a31724d376ba7ac8ce5c10f97da83d | IRCbot |
| 5 | ELF file | nmap | f8f76d8772f07b716913ba85f3af8380 | Classified as payload (scanned under cr4myx.exe) |
| 6 | Shell file | autorun | 5b9d4ff6a89da88dcf1d7d04b6d1e976 | Creates cron persistence and runs “run” |
| 7 | Shell file | go | 4c3d248b1fc8d4963ebdded4aecfcb8e | Win.Trojan.Tsunami-5 |
| 8 | Shell file | run | 70677ce8be9ebc5f81c299f753b98d66 | Runs the rootkits |
| 9 | Shell file | update | 26ad93d703a565a2642c422b2434fc78 | — |
| 10 | Tar file | bootbou.tgz | 98f1ac9c9baf2562eb00b7d4f89dc0dc | Contains malware and scripts |
| 11 | IP address | 64.227.142.133 | — | Marked malicious; no specific detections |
| 12 | C file | 1.c | 6ca73134ee02fb373ebaf9321b9840c8 | Win.Trojan.Tsunami-5 |
| 13 | C file | 2.c | a24cabef282713b6c0e3f9c3efdabd91 | Win.Trojan.Tsunami-5 |
| 14 | Zip file | gs.zip | 3b64c2ecd7ea152f9d4af9d0461db265 | Contains malware and scripts |
| 15 | Tar file | gs.tar | fb2ddb699bed59ff420b43f5640e7e0c | Contains malware and scripts |
| 16 | C file | a.c | a8d19e08aa022bacd8a76777874fad8a | Win.Trojan.Tsunami-5 |
| 17 | Perl file | bot | 1d4c9039ca7e0b3e93c708f5d02f92a0 | Win.Trojan.Tsunami-5 |
| 18 | C file | clean.c | 077cdcbe6c1bf4a0f4bc81feaf283be3 | Clean access records and logs |
| 19 | C file | cls.c | 2b31ba929f3e4f8e8c84b3815b0e4909 | Cleans login logs |
| 20 | Shell file | distro | 94e513b01f26399ae16ac91b50fde268 | — |
| 21 | Shell file | go | fd55f0754084ba041539bb469f06a83d | — |
| 22 | C file | ping.c | 4777d24c864c04a6bfabb836811edf2d | Privileged backdoor |
| 23 | IP address | 185.243.218.59 | — | IRC channels #xx and #SIP |
| 24 | IP address | 154.35.175.201 | — | IRC channels #xx and #SIP |
| 25 | IP address | 94.125.182.255 | — | IRC channels #xx and #SIP |
| 26 | IP address | 23.228.66.219 | — | IRC channels #xx and #SIP |
| 27 | IP address | 199.71.214.87 | — | IRC channels #xx and #SIP |
| 28 | IP address | 172.83.156.122 | — | IRC channels #xx and #SIP |
| 29 | Domain | irc.undernet.org | — | IRC channels #xx and #SIP |
| 30 | Domain | plm.ftp.sh | — | IRC channels #xx and #SIP |
| 31 | Domain | gsm.ftp.sh | — | IRC channels #xx and #SIP |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.