Let’s Nmap

Source link
Related Articles
All Mix →Dumping Cursor for VSCode + Claude Code
Table of Contents Cursor: Actually Pretty Great What Cursor Got Right But Then Claude Code Happened Why VSCode + Claude Code Wins No Subscription Required…
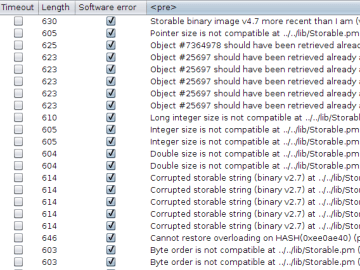
Deserialization in Perl v5.8 | Agarri : Sécurité informatique offensive
Deserialization in Perl v5.8 During a pentest, I found an application containing a form with a hidden parameter named “state”. Encoded as Base64, it contains…
The critical role of VDPs in cybersecurity
Table of Contents What is a vulnerability disclosure policy? Why implement a vulnerability disclosure policy? VDPs encourage responsible reporting Enhanced security posture through better collaboration …
[tl;dr sec] #289 – AI-powered Fuzzing, Incentives in Security, Malware in DNS
Table of Contents Building My Custom AI Therapist AppSec Cloud Security Supply Chain Blue Team Red Team AI + Security Building My Custom…
Unsupervised Learning NO. 387 | Daniel Miessler
Unsupervised Learning is a Security, AI, and Meaning-focused podcast that looks at how best to thrive as humans in a post-AI world. It combines original…
Abusing URL Shortners to discover sensitive resources or assets
September 22, 2015 · websec bruteforce As of late, a fair few companies and startups have been using dedicated URL shortner services to use for…

![[tl;dr sec] #289 - AI-powered Fuzzing, Incentives in Security, Malware in DNS](https://image.cybernoz.com/wp-content/uploads/2025/07/tldr-sec-289-AI-powered-Fuzzing-Incentives-in-Security-Malware.png)