LevelUpX – Series 14: Finding and Exploiting Hidden Functionality in Windows DLLs with Nerdwell

Source link
Related Articles
All Mix →AI State Management (AISM) | Daniel Miessler
Table of Contents The Delta Between Current State and Desired State AI's role in this AISM (AI State Management) Summary One of the biggest pushbacks…
Leaking Session Tokens with CVE-2023-4966
Table of Contents Introduction Patch Diffing Finding the Vulnerable Function Exploiting the Endpoint Verifying the Session Token Final Thoughts Introduction It’s time for another round…
The World’s Elite Hackers Share Tips and Insights
As many hackers on the HackerOne platform know, you can make a good living out of bug-hunting. But a few of our hackers have made a really good…
Meet Detectify! – Detectify Blog
Table of Contents SEPTEMBER Nordic.js Guest lecture for IT security students at Iftac Workshop: Web security for startups – Go hack yourself or someone else will…
CVE-2024–45186: Unauthenticated SSTI bug in Filesender exposes MySQL & S3 credentials and other configuration variables, potentially leaking all (sometimes encrypted) user uploaded files. Dutch Universities affected. | by Jonathan Bouman | Oct, 2024
FileSender is an open-source web application designed for securely transferring large files. The idea for FileSender was born in 2007 during a task-force meeting of…
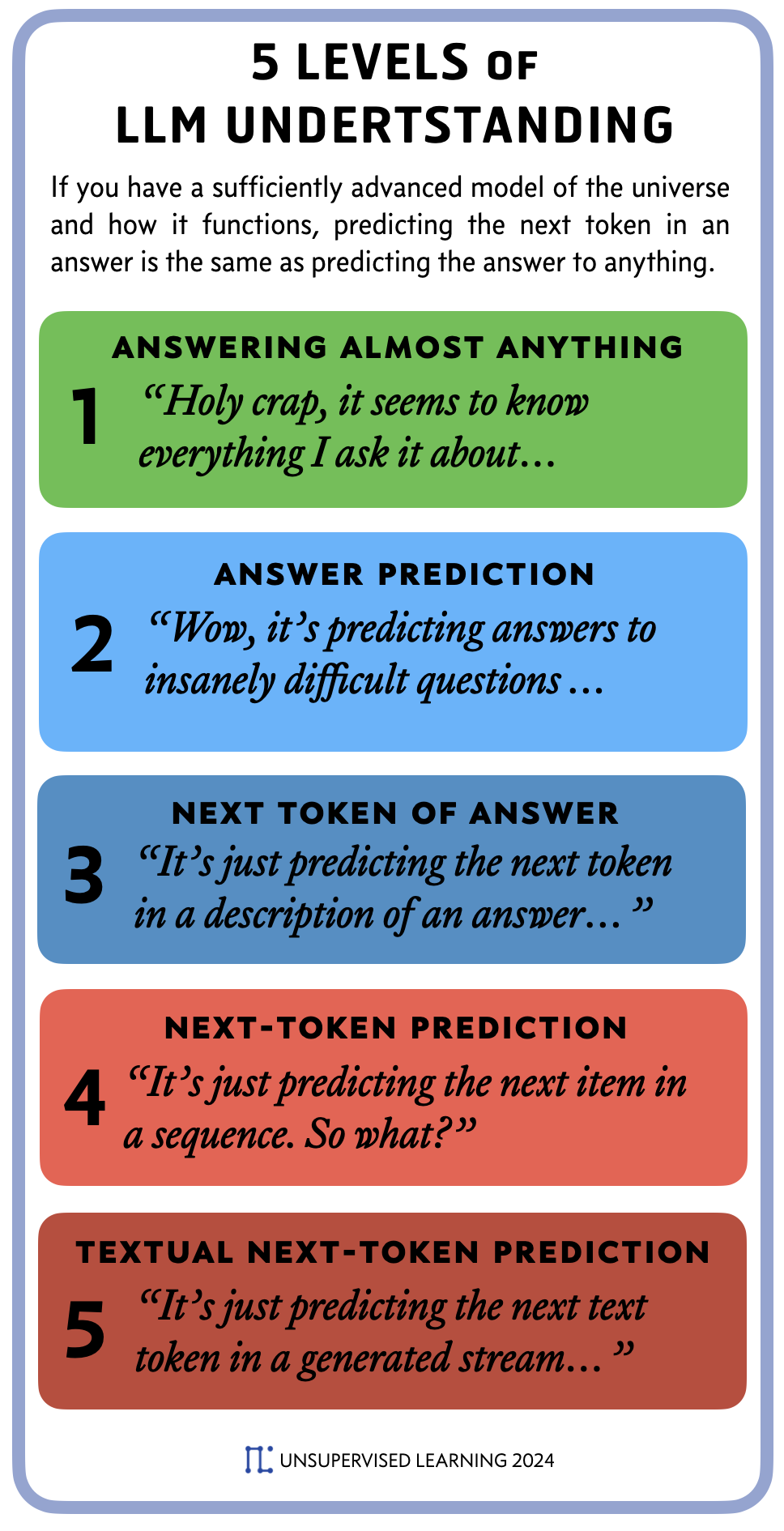
World Model + Next Token Prediction = Answer Prediction
Table of Contents Table of Contents A new way to explain LLM-based AI The 5 Levels of LLM Understanding Answers as descriptions of the world…