LevelUpX – Series 9: 8 Ways to (Almost) Never Get a Dupe Again with InsiderPhD (Katie Paxton-Fear)

Source link
Related Articles
All Mix →Cloud Security Alliance Webinar Recap: Avoid the Breach with Shopify’s Andrew Dunbar
In this Cloud Security Alliance (CSA) fireside chat, Shopify’s VP of Security Engineering and IT sat down with HackerOne’s Luke Tucker to talk about how…
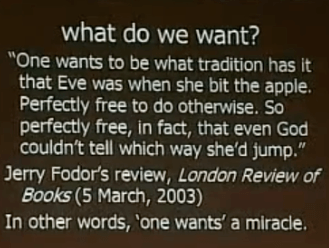
The Problem With Daniel Dennett’s Free Will
Before going into my qualms with Daniel Dennett’s capability/evitibility-based free will, I want to point out that most supporters of Daniel Dennett’s brand of free…
Make Your Cybersecurity Dollars Last Longer
Table of Contents Harness AI To Do More With Less Manage Reduced Headcount Without Burning Out Staff By Effective Prioritization And Vendor Consolidation Innovate Securely…
Your bug bounty journey, our priority
The foundation of a successful partnership is a shared commitment to mutual growth – this is something we firmly believe at Intigriti. That’s why when…
8 essential tools for performing effective reconnaissance
Table of Contents Amass Google/Bing/GitHub dorking Eyewitness Wappalyzer GAU (GetAllUrls) Ffuf Arjun LinkFinder We all know that reconnaissance is important in bug bounty, in fact,…
Building the Ideal 100-word Password List
There’s some phenomenal password research here from clarkson.edu that talks about common passwords found during Internet attacks. I’ve taken those entries and put them into…