Live Hacking On Indeed with Tess 💥 | Hacker2Hacker

Source link
Related Articles
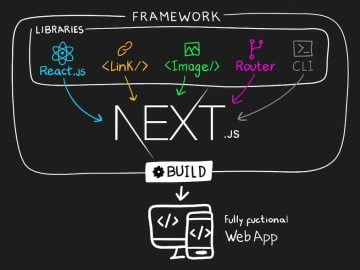
All Mix →Exploiting Web3’s Hidden Attack Surface: Universal XSS on Netlify’s Next.js Library
Table of Contents Overview Introduction How do static Web3 websites differ from a security perspective? Methodology Discovery and Findings (1) Open Redirect on “_next/image” via…
Adult Memory: Bad or Just Full?
This Wired piece supports a thought that I’ve had for sometime about the failing of memory with age. Don’t get me wrong, I’m sure there…
HackerOne Named “Leader” in the 2023 GigaOm PTaaS Radar Report
Table of Contents PTaaS: Revolutionizing Security Testing HackerOne Is Positioned to Deliver High-Impact and Efficient Community-driven PTaaS HackerOne Capabilities by Key Criteria and Evaluation Metrics…
10 LLM Vulnerabilities and How to Establish LLM Security [OWASP]
Table of Contents LLM01: Prompt Injection What Is Prompt Injection? Solutions to Prompt Injection LLM02: Insecure Output Handling What Is Insecure Output Handling? Solutions to…
Are Creativity and Materialism Opposites?
I’ve been thinking a lot about what matters in life recently–specifically about focusing in on the things that matter, and trimming much of the rest.…
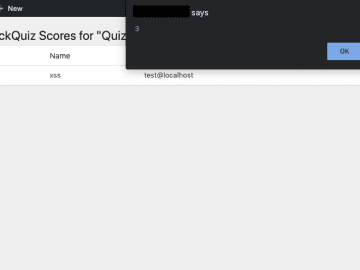
From Quiz to Admin – Chaining Two 0-Days to Compromise An Uber WordPress – RCE Security
Table of Contents TL;DR CVE-2019-12517: Going From Unauthenticated User to Admin via Stored XSS CVE-2019-12516: Authenticated SQL Injections To the Rescue Connecting XSS and SQLi…