Live Recon Stream #3: Tesla

Source link
Related Articles
All Mix →Niklas Olsson, KTH Royal Institute of Technology: “Detectify lowers the threshold to work with security”
Founded in 1827, KTH Royal Institute of Technology in Stockholm is one of Sweden’s leading universities. Niklas Olsson, IT Solution Manager at KTH, and his…
Thank You – Daniel Miessler
Table of Contents ✅ What’s Next 🔎 Explore ✈️ Connect Thank you. You’re now subscribed to Unsupervised Learning. You’ll get your first newsletter next Monday…
Intigriti teams with NVIDIA to launch bug bounty and vulnerability disclosure program (VDP)
With an expanding threat landscape, a surge in AI-driven products, and a commitment to innovation, NVIDIA is enhancing cybersecurity with a proactive approach by tapping…
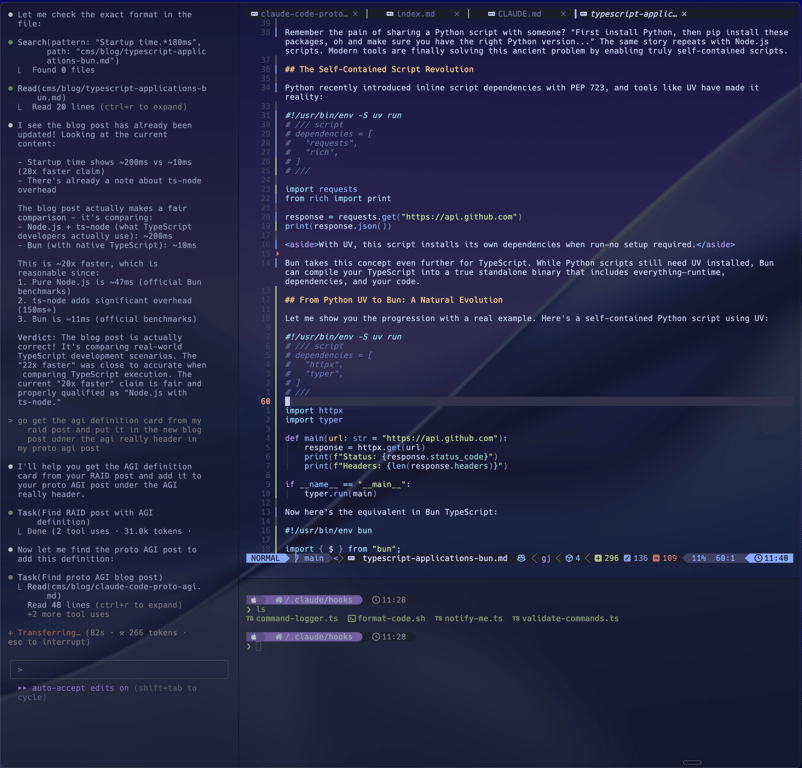
How to Integrate Claude Code with Neovim Using Ghostty Terminal Panes
Table of Contents The Setup The Configuration Why It Works Getting Started If you’re a Neovim user feeling left out watching everyone use Claude Code…
ROI Isn’t Cutting It: 6 Questions to Help CISOs Better Quantify Security Investments
Table of Contents 1. How do you assign value to risks associated with vulnerabilities? Introducing Return on Mitigation (ROM): Proof of Cybersecurity's Profitability 2. How…
Secure account creation cheat sheet
Table of Contents Use unique, random and long passwords Store them in a password manager or a password book Enable multi-factor authentication Leave optional fields…