🔴 Live Video Editing: Beginners Bug Bounty, Where to Begin

Source link
Related Articles
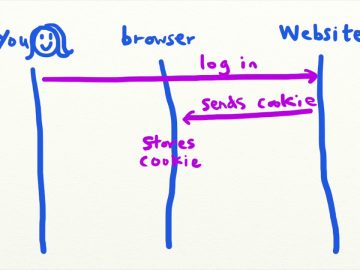
All Mix →Intro to CSRF (Cross-Site Request Forgery) – Security Simplified
Intro to CSRF (Cross-Site Request Forgery) – Security Simplified Source link
Bug Bounty 5 Years In
Table of Contents Why I like bounty programs How to prepare Bug bounty skillset It's alive! The suck Keep it spicy Cause for hope This…
Most Companies Aren’t Anywhere Near Ready for AI
Most of the frustration people have with AI not being able to do what they want is actually them not being able to describe what…
Bash and shell expansions: lazy list-making
Table of Contents Pattern match substitution Substrings Testing variables Changing case Expanding arrays A tour of brace expansion, shell parameter expansions, and playing with substrings…
Improving my Beehiiv Search Experience
I said goodbye to the frustrations of Beehiiv’s built-in search and now enjoy a much more efficient and user-friendly experience. We all have our favorite…
5 Things Top Bug Bounty Hunters Do Differently
Table of Contents They Know How to Build They Have An Eye For Anomalies They Submit Quality Reports They Set Goals They Hack together This…