Cybersecurity researchers have uncovered an updated version of a backdoor called LODEINFO that’s distributed via spear-phishing attacks.
The findings come from Japanese company ITOCHU Cyber & Intelligence, which said the malware “has been updated with new features, as well as changes to the anti-analysis (analysis avoidance) techniques.”
LODEINFO (versions 0.6.6 and 0.6.7) was first documented by Kaspersky in November 2022, detailing its capabilities to execute arbitrary shellcode, take screenshots, and exfiltrate files back to an actor-controlled server.
A month later, ESET disclosed attacks targeting Japanese political establishments that led to the deployment of LODEINFO.

The backdoor is the work of a Chinese nation-state actor known as Stone Panda (aka APT10, Bronze Riverside, Cicada, Earth Tengshe, MirrorFace, and Potassium), which has a history of orchestrating attacks targeting Japan since 2021.
Attack chains commence with phishing emails bearing malicious Microsoft Word documents that, when opened, execute VBA macros to launch downloader shellcode capable of ultimately executing the LODEINFO implant.
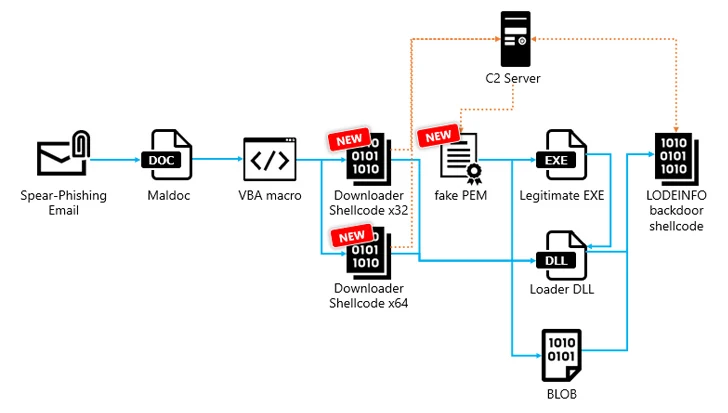
LODEINFO infection paths in 2023 have also been observed making use of remote template injection methods to retrieve and execute malicious macros hosted on the adversary’s infrastructure every time the victim opens a lure Word document containing the template.
What’s more, checks are said to have been added sometime around June 2023 to verify the language settings of Microsoft Office to determine if it’s Japanese, only for it to be removed a month later in attacks leveraging LODEINFO version 0.7.1.

“In addition, the filename of the maldoc itself has been changed from Japanese to English,” ITOCHU noted. “From this, we believe that v0.7.1 was likely used to attack environments in languages other than Japanese.”
Another notable change in attacks delivering LODEINFO version 0.7.1 is the introduction of a new intermediate stage that involves the shellcode downloader fetching a file that masquerades as a Privacy-Enhanced Mail (PEM) from a C2 server, which, in turn, loads the backdoor directly in memory.

The downloader shares similarities with a known fileless downloader dubbed DOWNIISSA based on the self-patching mechanism to conceal malicious code, encoding method for command-and-control (C2) server information, and the structure of the data decrypted from the fake PEM file.
“LODEINFO backdoor shellcode is a fileless malware that allows attackers to remotely access and operate infected hosts,” the company said, with samples found in 2023 and 2024 incorporating extra commands. The latest version of LODEINFO is 0.7.3.
“As a countermeasure, since both the downloader shellcode and the backdoor shellcode of LODEINFO are fileless malware, it is essential to introduce a product that can scan and detect malware in memory in order to detect it,” it added.