The popular LottieFiles Lotti-Player project was compromised in a supply chain attack to inject a crypto drainer into websites that steals visitors’ cryptocurrency.
Blockchain threat monitoring platform Scam Sniffer reports that at least one victim allegedly lost $723,000 worth of Bitcoin due to the LottieFiles supply chain compromise.
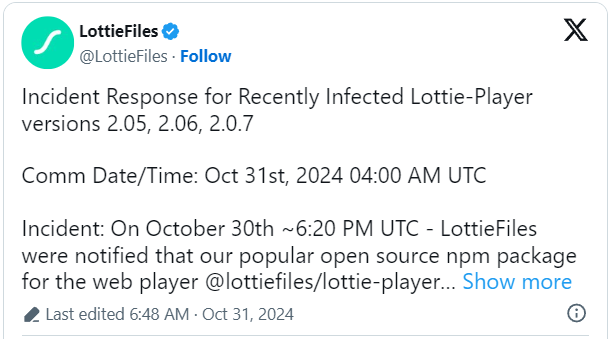
As discovered yesterday, following multiple user reports about strange code injections, Lottie Web Player (“lottie-player”) 2.0.5, 2.0.6, and 2.0.7 were modified yesterday to include malicious code that injects a crypto wallet drainer into websites.
Crypto wallet drainers are malicious scripts injected into websites that display web3 prompts to connect a cryptocurrency wallet. However, when a user connects their wallet, the script will automatically attempt to “drain,” or steal, all assets and NFTs and send them to the threat actors.
LottieFiles quickly released version 2.0.8, which is based on the clean 2.0.4, advising users to upgrade to it as soon as possible.
“A large number of users using the library via third-party CDNs without a pinned version were automatically served the compromised version as the latest release,” explains LottieFiles CTO Nattu Adnan..
“With the publishing of the safe version, those users would have automatically received the fix.”
Those unable to upgrade to the latest release should communicate the risk to Lottie-player end users and warn them about fraudulent cryptocurrency wallet connection requests. Staying on version 2.0.4 is also an option.
LottieFiles is a software-as-a-service (SaaS) platform for creating and sharing lightweight vector-based (scalable) animations that can be embedded in apps and websites.
It’s popular for allowing high-quality visuals at a minimal performance impact on less powerful devices, mobile, and web apps.
Supply chain attack loads crypto wallet drainer
Yesterday, developers using the Lottie-Player script discovered that they were affected by a supply chain attack, with websites using the compromised script suddenly displaying prompts to connect a cryptocurrency wallet.
BleepingComputer tested the malicious version of the Lottie-Player JavaScript script [VirusTotal] by adding it to a simple HTML page and can confirm that once it was added, the script would load a crypto drainer.
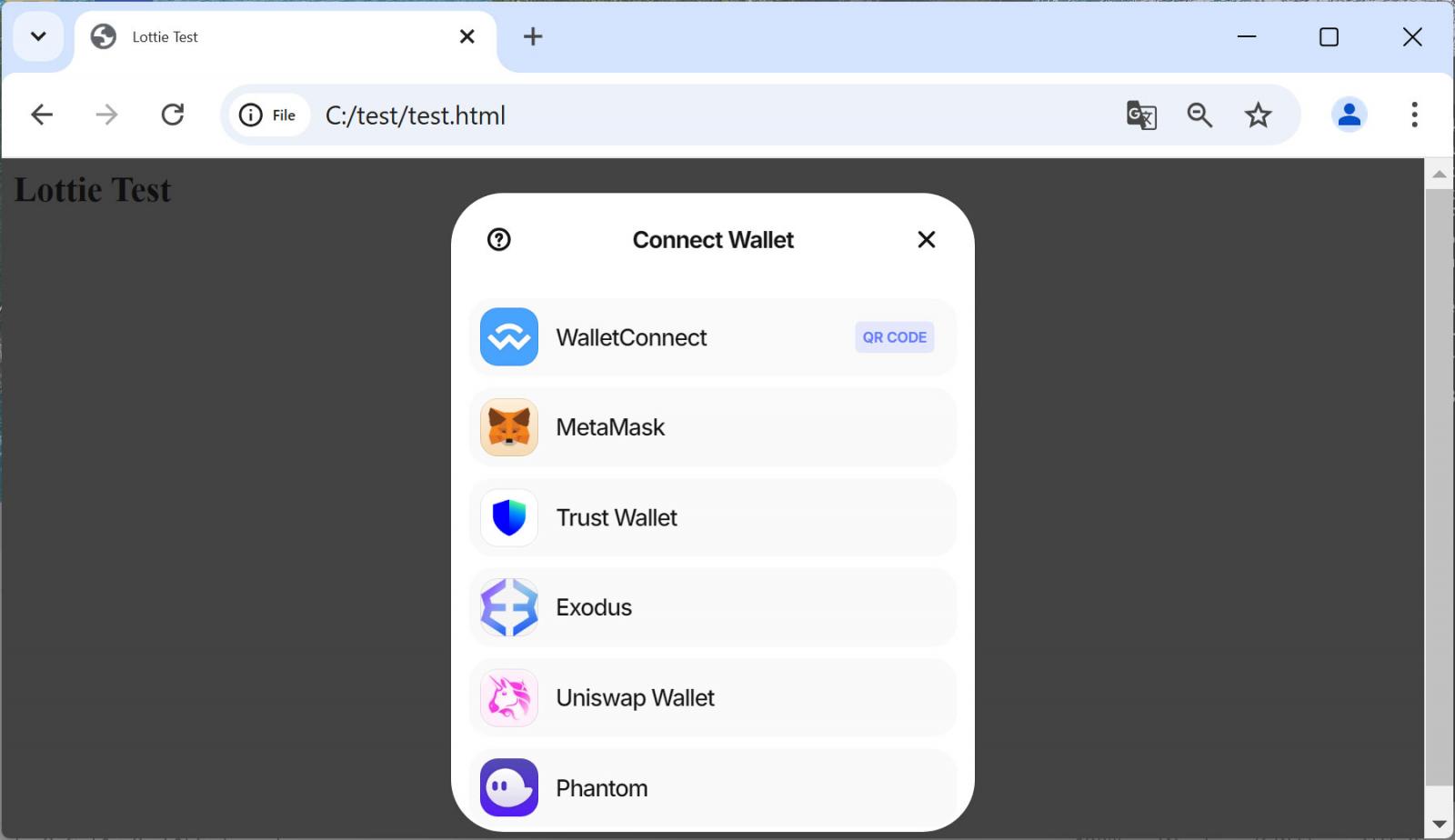
Source: BleepingComputer
If a visitor clicks on one of the buttons to connect to a wallet, the script will make a WebSocket connection to the site castleservices01[.]com [VirusTotal], which has a history of being used in cryptocurrency phishing attacks.
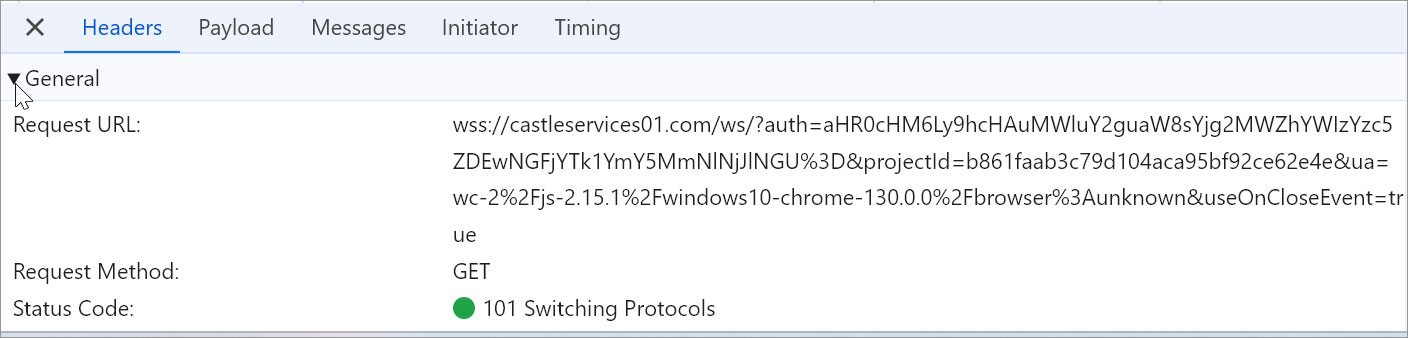
Source: BleepingComputer
LottieFiles says its JavaScript library was compromised after an authentication token for one of its developers was stolen and used to upload the malicious versions of the npm package.
“We have confirmed that our other open source libraries, open source code, Github repositories, and our SaaS were not affected,” assures LottieFiles.
The platform continues its internal investigation of the compromise with the help of external experts, and more details about the incident might be made available in the future.
The exact number of victims and amount of cryptocurrency lost to this scheme are unknown at this time.
Crypto drainers have become a massive problem for the cryptocurrency community, with threat actors hacking well-known X accounts, hacking websites, and using AI videos and malicious advertising to promote websites that utilize the malicious scripts.
In 2023, Google and Twitter ads promoted sites containing a cryptocurrency drainer named ‘MS Drainer’ that stole $59 million from 63,210 victims over nine months.