Attackers have weaponized a malicious fork of the legitimate Triton macOS client for omg.lol, turning a trusted open-source project into a delivery channel for Windows malware hosted on GitHub.
The campaign abuses GitHub’s forking model, misleading README content, and obscure asset paths to trick users into downloading a trojanized archive named Software_3.1.zip.
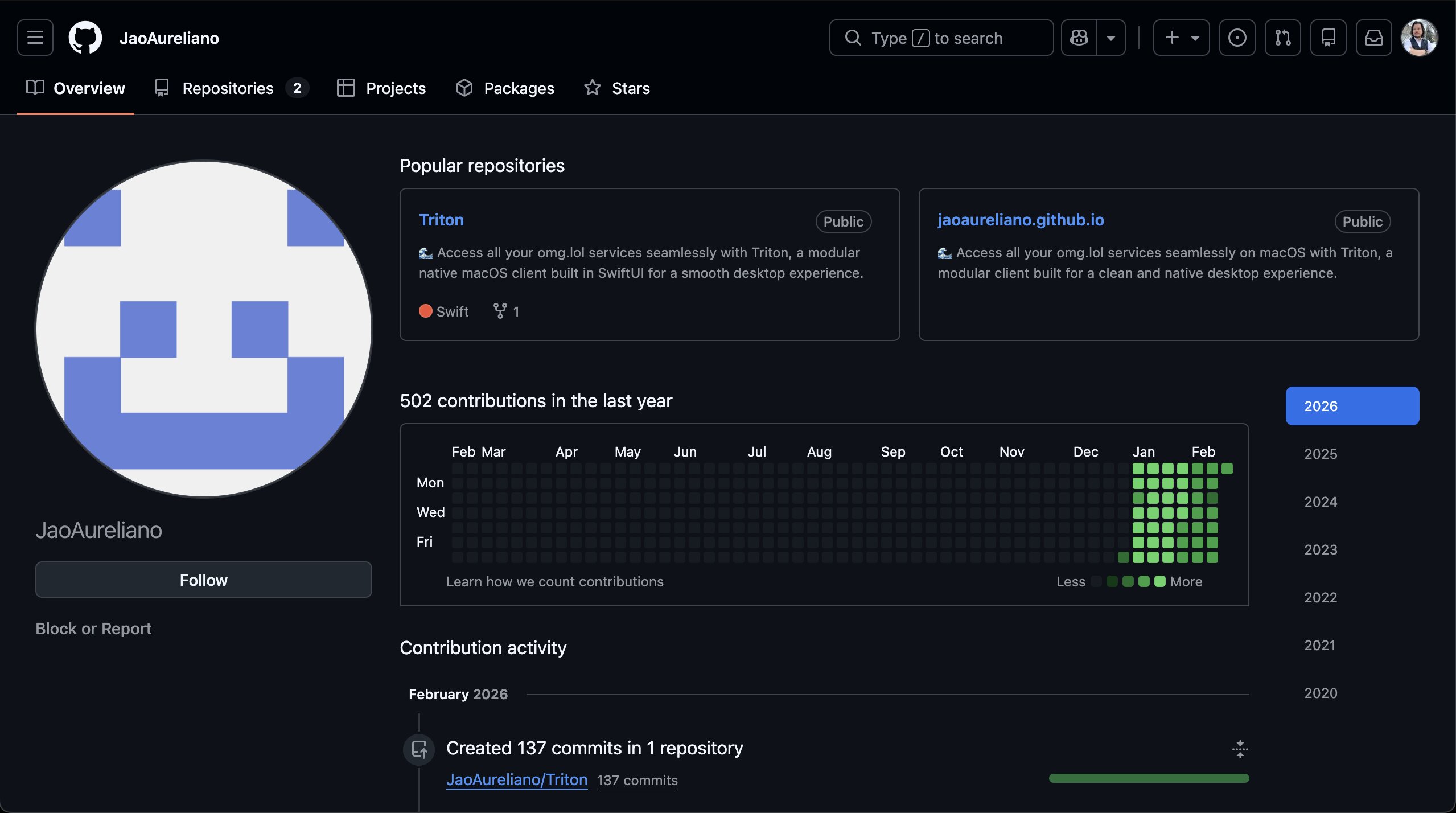
The malicious actor cloned this project under the account “JaoAureliano,” removed visible attribution, and rebranded the fork as if it were the official app while embedding a single ZIP-based payload.
The README in the fork is effectively a lure: every key section, including the description, “Getting Started,” download button, and even “Contributing Guidelines,” is wired to the same raw GitHub URL pointing to Software_3.1.zip inside an Xcode .xcassets colorset path.
Triton, created by developer Otávio C., is a native macOS client for omg.lol that aggregates services such as Statuslog, PURLs, Web Pages, Now Pages, Weblog, Pics, and Pastebin.
Rather than distributing a built macOS app or source intended for compilation, the repository repeatedly pressures users to download this ZIP directly, masking a Windows-focused malware under the guise of a Triton release.
Account Manipulation and Campaign Signals
The “JaoAureliano” account only hosts two repositories, suggesting a focused operation rather than a long-lived developer profile.
While the malicious Triton repo shows minimal real development activity, the contribution graph on the profile has been artificially inflated through backdated automated commits to create an illusion of history and obfuscate when the malware was introduced.
Repository topics such as “malware,” “deobfuscation,” “pytorch,” “symbolic-execution,” and “llm-training” are attached to the project, likely to appear research-oriented or educational, or simply due to misconfiguration or incompetence.
Combined with the odd README wording and overexposed download links, these signals highlight a poorly disguised but dangerous attempt to abuse GitHub reputation and developer trust.
The payload inside Software_3.1.zip is identified by SHA-256 hash 39b29c38c03868854fb972e7b18f22c2c76520cfb6edf46ba5a5618f74943eac, with a detection rate of 12/66 engines on VirusTotal at the time of analysis.
Although it rides on a macOS-branded app fork, execution is Windows-only, underscoring the opportunistic nature of the campaign and its focus on cross-ecosystem abuse rather than platform alignment.
Execution begins with 7za.exe extracting the password-protected archive (“infected”) into a randomly named temporary directory, followed by cmd.exe launching a batch script (Launcher.cmd) that chains into additional components, including luajit.exe for scripted behavior.
The malware employs anti-analysis measures such as debugger detection, long sleep intervals, and virtualization/sandbox checks, mapping to MITRE ATT&CK tactics including Execution (T1059), Defense Evasion (T1140, T1497, T1562), Discovery (T1082, T1012, T1057), and Command and Control (T1071, T1573, T1090).
Mitigations
Network activity reveals DNS and HTTP traffic toward endpoints including nexusrules.officeapps.live.com, svc.ha-teams.office.com, ip-api.com, polygon-rpc.com, and an IP-based C2 path at 89.169.12.160 under an encoded API route, blending in with legitimate Office and blockchain-related traffic to evade simple monitoring.
This incident underscores how easily a benign open-source macOS project can be turned into a malware distribution vector by a hostile fork, especially when users follow README links instead of verified releases.
On disk, the malware inspects key Windows directories, developer environments (Java, Python, .NET), and security-related logs, while registry access to .NET Framework and system configuration hives supports profiling, persistence groundwork, or tailored payload delivery.
Security teams and developers should validate repository owners, inspect commit histories, and prefer official release artifacts, while defenders should monitor for the listed hash, URLs, processes (7za.exe, Launcher.cmd, luajit.exe), and suspicious traffic to office-themed and blockchain RPC endpoints as indicators of compromise.
Indicators of Compromise (IOCs)
File Hashes
| Indicator Type | Value / Details |
|---|---|
| SHA-256 | 39b29c38c03868854fb972e7b18f22c2c76520cfb6edf46ba5a5618f74943eac |
| File Size | 1.33 MB |
| File Type | ZIP archive containing PE executables |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.