Malicious Google Ads are increasingly being used to steal cryptocurrency by draining wallets and harvesting seed phrases from unsuspecting users searching for legitimate DeFi apps and wallet services.
Recent campaigns tracked by SEAL show a sustained, technically advanced operation that actively evades Google’s automated defenses while directly targeting both retail users and crypto organizations.
In just a few weeks, SEAL blocked more than 356 malicious ad URLs, indicating that attackers are continuously rolling out fresh ads and landing pages as older ones are taken down.
Google has suspended all advertiser accounts identified in SEAL’s reporting, but affected users continue to submit new incident reports, showing that the broader ecosystem abuse is still far from contained.
SEAL is tracking multiple threat actors abusing Google Ads to promote fake versions of DeFi applications, wallets, and other crypto services, with activity spiking in March 2026 and continuing at a steady pace for over a year.
These campaigns rely heavily on cloaking and fingerprinting to bypass Google’s automated review systems and frustrate security researchers, only serving the malicious content to carefully selected victims while redirecting others to benign pages such as legitimate documentation or even Wikipedia.
Abusing Trusted Google Properties
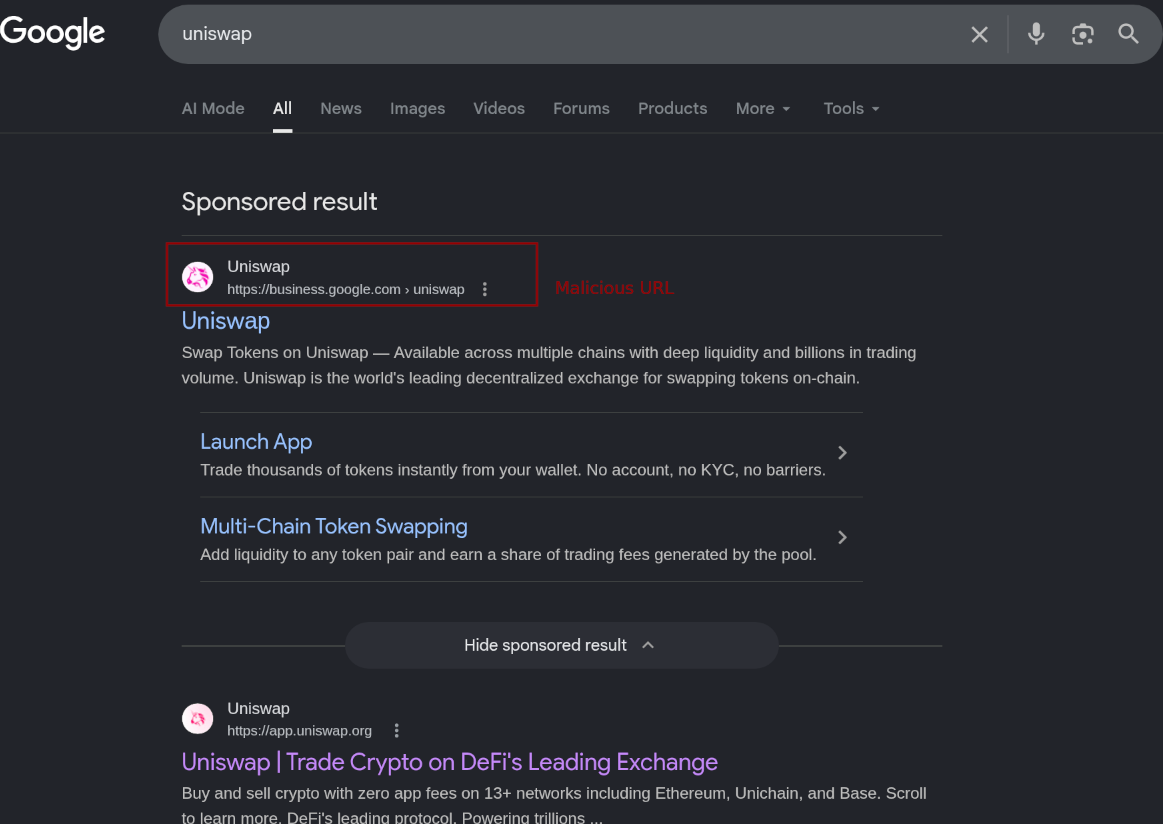
Attackers commonly abuse high‑reputation Google properties like sites.google.com, docs.google.com, and business.google.com as the “primary” frame for their ads, so that Google Search shows a convincing URL, title, description, and logo that appear indistinguishable from a legitimate project.
Behind this façade, the malicious payload is hosted in secondary iframes and off‑platform infrastructure, which means automated policy checks often only inspect the benign wrapper while missing the true attack surface.
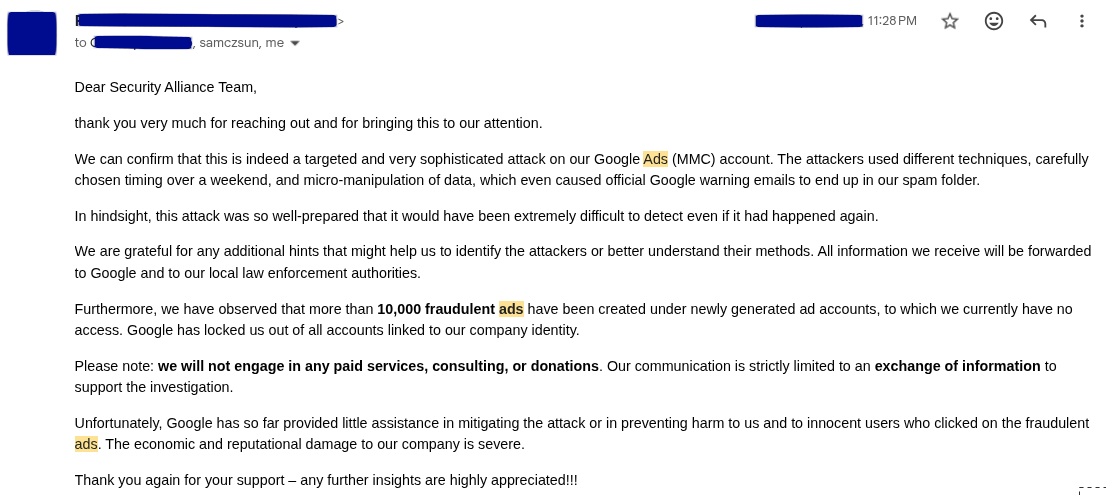
Threat actors obtain access to ad slots via hacked advertiser accounts as well as verified accounts purchased on underground crime markets, including screenshots and forum logs showing access to large brand accounts such as Apple’s being abused to push malicious crypto ads.
SEAL is tracking multiple drainer‑as‑a‑service families abusing Google Ads, with Inferno Drainer and Vanilla Drainer among the most commonly observed across ongoing campaigns.
These JavaScript‑based drainers trick users into signing malicious blockchain transactions in‑browser, silently transferring control of assets to the attacker while the interface appears to function normally.
Other campaigns focus on seed phrase theft by cloning hardware wallet sites such as Ledger, prompting users to enter their recovery phrase, or distributing malicious browser extensions via Chrome Web Store links designed to capture seed phrases and wallet data.
Drainer‑as‑a‑service operators typically provide obfuscation, automated deployment, and transaction generation infrastructure in exchange for roughly 20% of each successful theft, making it easy for less technical threat actors to launch large‑scale campaigns.
Front-End and Proxy Architecture
Advanced campaigns use a three‑layer web architecture to evade detection and maximize control over victim interactions.
A small “entry document” is often hosted on Arweave‑backed domains such as arweave.mainnet.irys.xyz, fully spoofing the target protocol’s metadata while pointing all assets to a Cloudflare Workers instance on *.workers.dev via a hardcoded configuration variable.
The cloned front end sometimes several megabytes in size renders a near‑pixel‑perfect copy of sites like Uniswap, even loading token images from legitimate sources such as CoinGecko and Trust Wallet to reinforce authenticity.
Obfuscated payloads stored on *.irys.xyz relies on runtime code construction and compressed strings consistent with sophisticated drainer families like Vanilla Drainer, while a man‑in‑the‑middle proxy layer transparently reroutes all API, GraphQL, and Ethereum RPC traffic through attacker‑controlled domains such as thirdtemple.top.
This gives operators full visibility into wallet balances and transactions and allows them to inject tailored malicious payloads based on the victim’s assets, with additional logic wiping caches and simulating normal browser behavior to avoid detection.
Many campaigns are heavily automated: when a URL is blocked at the wallet level by defenses such as open‑source blocklists, the backend quickly relaunches with new ad creatives and landing page URLs, sometimes hiding the final payload behind multiple chained iframes that mimic commercial Traffic Distribution Systems.
This constant churn contributes to a long‑running cat‑and‑mouse game in which security vendors like SEAL can limit damage but cannot fully solve abuse on the ad platforms’ behalf.
SEAL recommends that cryptocurrency users and organizations avoid relying on Google Search to reach wallet or DeFi applications, instead using only trusted bookmarks and independently verified URLs.
Users can cross‑check services through crypto‑specific indexing tools such as DefiLlama’s search portal, and should never enter seed phrases, private keys, or recovery data into web forms especially those reached via ads.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.