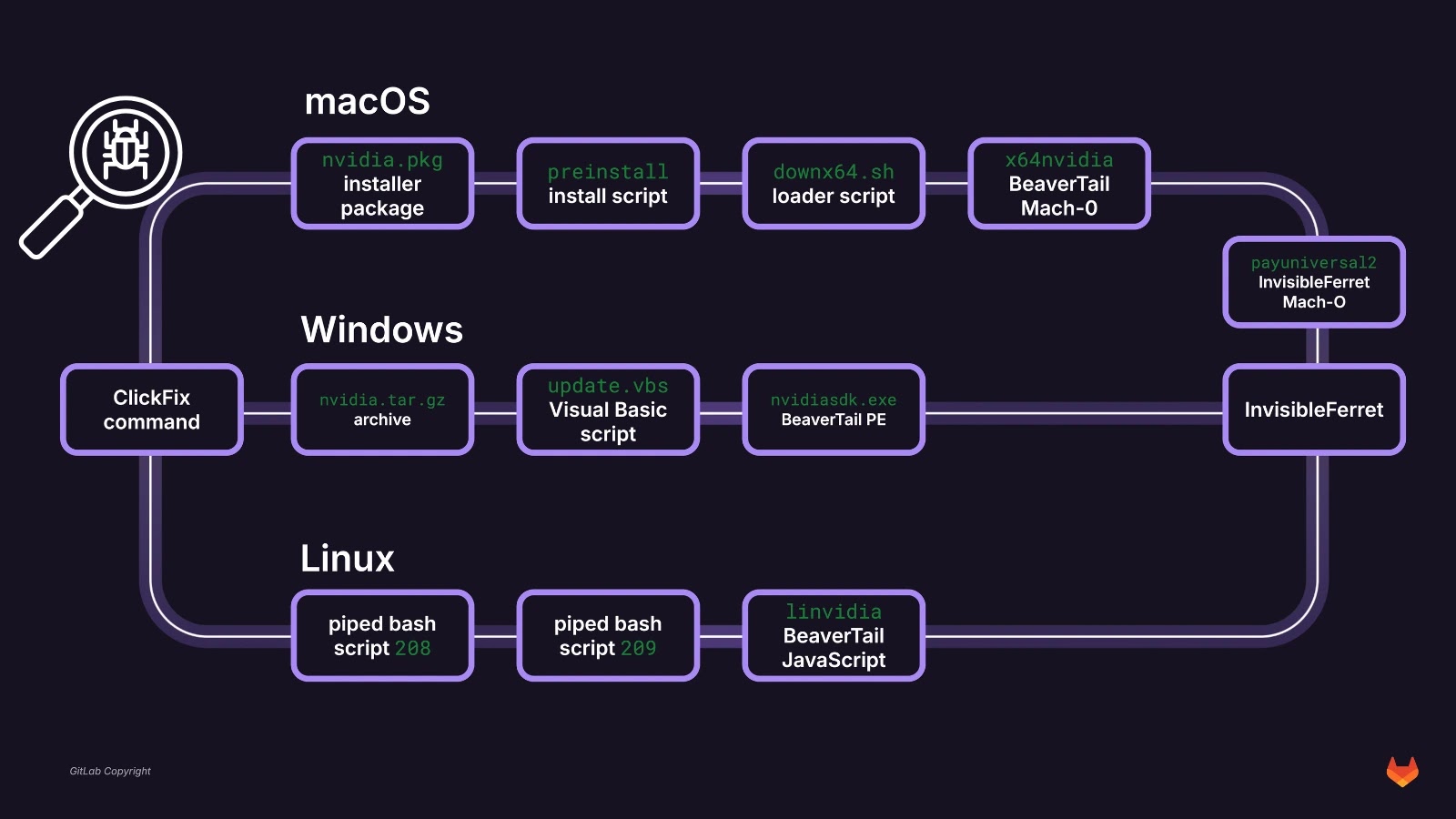
Malicious npm package js-logger-pack is now abusing Hugging Face not just as a malware CDN, but also as a live exfiltration backend for stolen data, turning a popular AI platform into part of a full-featured cross‑platform implant chain.
Earlier campaign phases already used Hugging Face as a simple hosting point for those binaries, but the latest builds go further by pushing victims’ data into private Hugging Face datasets controlled by the attacker.
The result is a supply-chain attack where a seemingly harmless npm logging library becomes an infostealer, keylogger, and remote access tool that blends into normal developer workflows.
On npm, js-logger-pack appears to be a legitimate logging utility: dist/index.js contains a plausible, benign logger implementation that passes casual inspection.
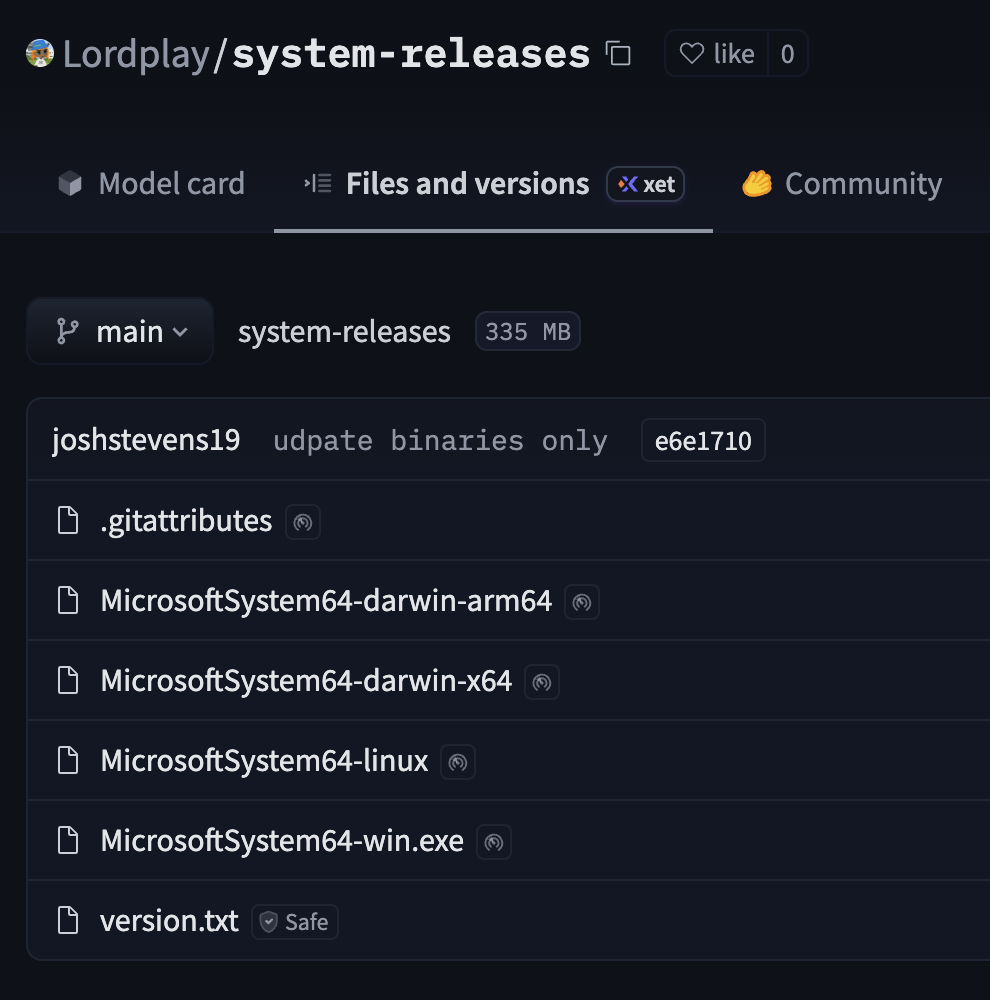
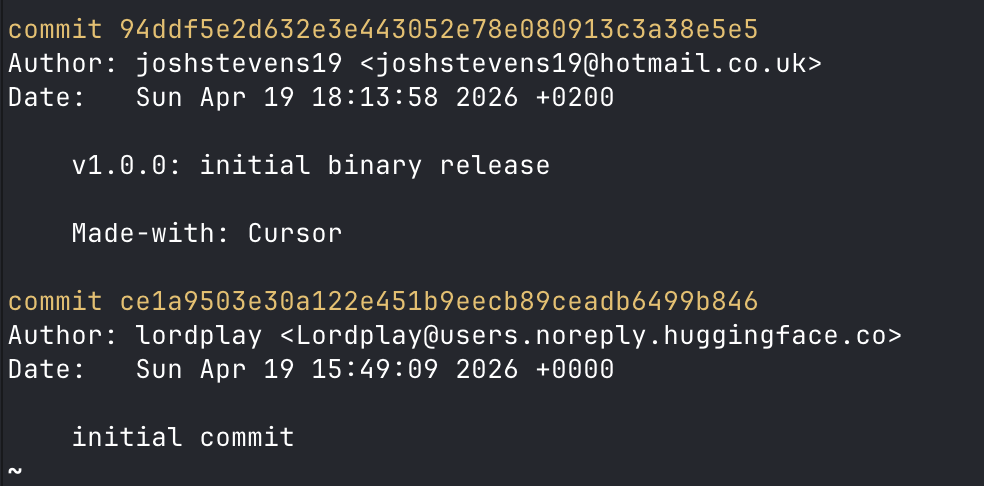
Recent versions of js-logger-pack, including 1.1.27, download a binary called MicrosoftSystem64 from the public Hugging Face repository Lordplay/system-releases and execute it as a second-stage payload.
The real trigger hides in package.json, where a postinstall hook quietly runs node print.cjs during npm install, then backgrounds itself so the installation appears to complete normally while the malware downloader continues running.
print.cjs reaches out to https[:]//huggingface.co/Lordplay/system-releases/resolve/main/ and pulls one of four MicrosoftSystem64 binaries based on OS and architecture (Windows PE, macOS Intel/ARM Mach-O, and Linux ELF).
These binaries are not four different families, but the same cross-platform implant wrapped into Node.js Single Executable Application (SEA) containers, with an identical embedded JavaScript bundle across all platforms.
Implant capabilities and C2
Once launched, the MicrosoftSystem64 process registers persistence (via scheduled tasks or Run keys on Windows, LaunchAgents on macOS, and systemd/XDG autostart on Linux), connects to a hard-coded controller at 195[.]201[.]194[.]107:8010 over WebSocket and HTTP, and begins harvesting data.
Out of the box, it logs keystrokes, monitors the clipboard, scans for secrets and sensitive files, and maintains a live connection to receive operator commands.
The implant exposes a rich task protocol that lets the attacker list and read files, delete or create directories, scan recursively for credentials and wallets, exfiltrate Telegram Desktop data, deploy arbitrary binaries, clear browser sessions, and update itself on demand.
File operations accept arbitrary absolute, UNC, and drive-letter paths with no sandboxing, giving the operator broad access to any user-reachable data on compromised machines.
Hugging Face plays two roles in this attack chain: it hosts the MicrosoftSystem64 binaries and also acts as the exfiltration backend for stolen data.
The malware periodically checks a version.txt file in the Lordplay/system-releases repository to see if a new binary is available, then self-updates by downloading and restarting without any signature or checksum verification.
Lordplay identity break (Source : JFrog).For data theft, the operator can issue an upload_folder_hf task that instructs the implant to archive chosen files or directories into gzip, create or reuse a private dataset derived from the victim’s agentId and path, and upload the archive using the embedded Hugging Face client library.
Upload state is tracked locally and resumed after reconnect, meaning the attacker never has to keep large stolen datasets on the C2 server itself, and can instead leverage Hugging Face’s infrastructure for storage and distribution.
Cross-platform keylogging and OSINT links
Because the core payload is JavaScript, it dynamically compiles or invokes native helpers on each platform to capture keystrokes and clipboard data in a platform-native way.
On Windows it compiles C# code via PowerShell, on macOS it compiles temporary Swift programs, and on Linux it uses X11 tooling or raw /dev/input access, ensuring deep visibility into user input across desktops.
Open-source intelligence around the Lordplay Hugging Face namespace shows an unusual identity shift: older benign model repositories use one consistent author identity, while the malicious system-releases repo switches to a different author string that matches a real engineering executive, likely as deliberate impersonation.
Additional overlaps with the whisdev / snipmaxi / jrodacooker.dev cluster suggest campaign-adjacent personas and infrastructure, but the available evidence does not conclusively attribute the operation to a specific individual.
Any environment that installed [email protected], or any release that downloads MicrosoftSystem64 binaries, should be treated as fully compromised, including CI/CD runners and developer workstations.
Defenders should rotate all secrets exposed on affected hosts, remove persistence artifacts across Windows, macOS, and Linux, wipe local implant data directories, purge the malicious npm package and lockfiles, and reinstall dependencies with script execution disabled by default.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.